Firmware Like BIOS: BIOS/UEFI vs Alternatives — A Practical Comparison
An objective, side-by-side guide comparing BIOS/UEFI-like firmware with vendor-specific boot firmware across devices, focusing on security, update methods, recovery, and best-practice strategies for tech enthusiasts and device owners.
Firmware like bios refers to the boot firmware that initializes hardware and starts the OS. The comparison here pits BIOS/UEFI-based firmware against vendor-specific boot firmware and embedded variants, focusing on security, update methods, and recovery options. Debricking guides you through practical choices, safe flashing, and reliable rollback to minimize boot failures.
What firmware like bios really means for devices
When people talk about firmware like bios, they are referring to the core software that runs at startup, initializes hardware, and hands control to the operating system. In practice, this category includes traditional BIOS and modern UEFI implementations, plus similar boot firmware used by embedded devices, routers, and printers. For readers of Debricking, understanding this layer is essential because a failed firmware update can prevent a device from booting, complicating recovery. Throughout this guide, we treat firmware like bios as the family of boot-time firmware that governs the initial handshake between hardware and software, as well as subsequent recovery pathways. Debricking’s analysis emphasizes practical steps, safe update practices, and device-specific nuances. We discuss why BIOS/UEFI matters beyond the PC world and how other devices rely on adapted versions of this firmware. In every case, the goal is to ensure reliable startup, consistent hardware recognition, and predictable recovery options if something goes wrong. The Debricking team found that most failures occur during update attempts, so the focus here is on prevention, validation, and tested rollback strategies rather than blind updates.
The boot firmware landscape: BIOS/UEFI and beyond
Firmware like bios sits at the intersection of hardware and software. BIOS and its modern successor, UEFI, define how a system powers up, runs a POST check, and then hands off control to the operating system. Beyond PCs, embedded devices such as routers, printers, and some consumer electronics implement similar boot firmware with vendor-specific extensions. The landscape includes legacy BIOS compatibility layers, secure boot features in UEFI, and occasional proprietary extensions that optimize startup for a particular family of hardware. Debricking emphasizes that the choice between traditional BIOS, UEFI, and vendor-specific boot firmware hinges less on abstract labels and more on practical outcomes: reliability during power cycles, availability of recovery options, and the quality of vendor support during updates.
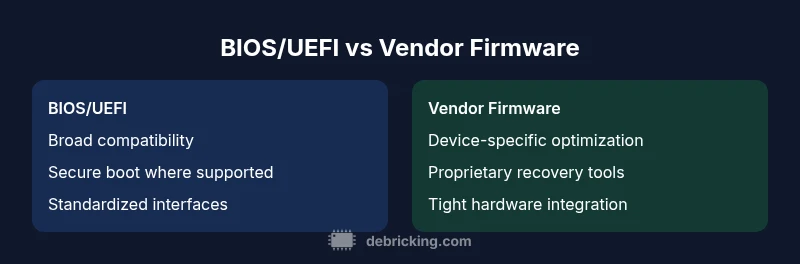
BIOS/UEFI vs vendor-specific firmware architecture
BIOS/UEFI architectures prioritize broad compatibility and standardized interfaces, which helps with cross-platform boot behavior and easier rollback through well-understood methods. Vendor-specific firmware, by contrast, is tightly integrated with a single device family, delivering hardware-specific optimizations, driver integration, and sometimes extended features like vendor recovery consoles. This section explains how these differences affect everyday use: boot speed, security posture, and the availability of hardware-level diagnostics. Debricking notes that while BIOS/UEFI provides a common ground, some devices rely on embedded controllers and firmware layers that sit beneath the main boot firmware to handle low-level tasks. Understanding these layers helps when diagnosing boot issues or planning updates across a mixed device environment.
Security implications: secure boot, firmware signing, and recovery options
Security is central to boot firmware. BIOS/UEFI implementations often include secure boot, measured boot, and firmware signing to prevent unauthorized code from executing at startup. Vendor-specific firmware adds another layer of protection, sometimes tied to hardware keys or secure elements. A practical takeaway is to ensure you enable secure boot where available, verify signatures before flashing, and maintain a trusted recovery path. Debricking’s guidance stresses that misconfigured security settings can paradoxically brick a device or disable legitimate updates. Recovery options—like dual-BIOS setups, hardware jumpers for recovery, or vendor-provided fallback tools—are invaluable, especially when an update goes wrong. In short, strong security and robust recovery plans are mutually reinforcing in boot firmware.
Update pathways and safety best practices
Firmware updates are the primary line of defense against evolving threats and hardware quirks. BIOS/UEFI updates typically come from motherboard manufacturers or OEMs, delivered via dedicated update utilities or bootable media. Vendor-specific firmware often uses product-specific channels, sometimes requiring login credentials or specialized software. The key practice is to follow official update paths exactly, back up configuration and current firmware when possible, and validate the update in a controlled environment. Debricking highlights the importance of offline update media, power stability, and verifying post-update boot behavior. Before updating, document the device model, current firmware version, and any unique recovery steps. This reduces the risk of bricking and eases rollback if something unexpected occurs.
Recovery and failure handling: bricking risk, recovery modes, and rollback options
The risk of bricking is real whenever firmware code changes at the boot level. BIOS/UEFI environments often include recovery modes, backup BIOS options, or dual-BIOS setups to restore functionality after a failed flash. Vendor firmware may provide similar capabilities but with device-specific limitations. A disciplined approach to recovery includes having a tested rollback plan, access to safe-mode diagnostics, and readiness to revert to a known-good firmware image. Debricking recommends simulating recovery scenarios in low-risk environments, documenting commands, and keeping a spare recovery tool ready. By anticipating failure modes, you reduce downtime and preserve device longevity.
Compatibility and cross-device considerations
Cross-device compatibility is a practical constraint in boot firmware. BIOS/UEFI aims for broad support across diverse motherboards and PC generations, but firmware updates can introduce vendor-specific quirks. Embedded devices and consumer gadgets often prioritize compatibility within a single product family, which can simplify rollbacks but limit portability. Debricking emphasizes mapping firmware strategies to device families: use standard interfaces where possible, stay within supported hardware revisions, and plan updates around the vendor’s recommended maintenance windows. When managing fleets of devices, document differences between BIOS/UEFI and vendor firmware to prevent confusing update campaigns.
Practical workflow: planning, backup, and validation before flashing firmware like bios
A repeatable workflow reduces firmware risk. Start with an inventory of devices and their current boot firmware versions, then categorize devices by risk level and update urgency. Create backups of current firmware images where possible and prepare a validated recovery plan. Test critical updates on a representative device before broader rollout, monitor boot logs, and verify that secure boot and diagnostic features remain intact after the update. Debricking’s recommended workflow also includes keeping a log of changes, using verified media for offline updates, and scheduling updates during low-usage windows. This disciplined approach yields smoother maintenance cycles and faster recovery if things go awry.
Debricking’s practical guidance for firmware like bios updates
For devices ranging from desktops to embedded systems, the safest path is to rely on official update channels, enable protections like secure boot, and maintain a tested rollback strategy. If you encounter a failure, avoid repeated flashing and instead use documented recovery modes and manufacturer tools. Debricking advocates documenting your exact device model, the firmware image used, and any error codes observed during the update. This information speeds up support and helps you learn from each update cycle. In short, treat boot firmware as a critical, safety-oriented component that deserves careful planning, verified media, and disciplined rollback procedures.
Comparison
| Feature | BIOS/UEFI (traditional boot firmware) | Vendor-specific firmware (embedded/controller) |
|---|---|---|
| Initialization speed | Moderate to fast with modern UEFI/fast boot | Often optimized per device, variable speed |
| Security features | Secure boot and measured boot in many implementations | Custom signing and hardware checks vary by vendor |
| Update process | Flashing via motherboard/BIOS utilities | Vendor tools or product-specific update channels |
| Recovery options | BIOS recovery modes, dual-BIOS in some boards | Vendor recovery tools and fallback modes |
| Platform support | Broad PC compatibility across brands | Tightly coupled to a single device family or vendor |
| Rollback/backup | Backup/dual-BIOS options exist on many boards | Rollback depends on hardware design and tooling |
Positives
- Offers broad compatibility and standard interfaces
- Supports clear rollback options in many implementations
- Separates firmware concerns from the operating system
- Provides well-documented recovery paths in common platforms
Disadvantages
- Bricking risk during updates if steps are skipped
- Security misconfigurations can expose boot vulnerabilities
- Vendor-specific firmware may limit cross-device portability
- Some devices require vendor tooling or accounts for updates
BIOS/UEFI-based firmware generally provides more universal reliability and safer rollback paths, while vendor-specific firmware can deliver tighter device integration and faster optimization.
For most devices, BIOS/UEFI offers a safer, more standardized boot firmware path with robust recovery options. Vendor firmware shines when hardware-level integration matters most. Choose based on device type, update support, and security requirements.
Questions & Answers
What is firmware like BIOS?
Firmware like BIOS refers to the boot-time software that initializes hardware and starts the operating system. It includes BIOS and UEFI implementations, plus similar boot firmware in embedded devices. Understanding this layer helps you diagnose boot issues and plan safe updates.
Firmware like BIOS is the boot software that starts your device. It includes BIOS and UEFI, and sometimes vendor-specific boot firmware in devices. Knowing how it works helps you update safely.
BIOS vs firmware: is there a difference?
BIOS is a type of firmware used for booting computers. Firmware in other devices may be embedded controllers or vendor-specific boot code. The key difference is context and integration: BIOS/UEFI aims for broad compatibility, while other firmware is specialized for a single device family.
BIOS is a kind of firmware used for booting, while other firmware is more device-specific.
Is BIOS/UEFI secure by default?
Security features like secure boot and firmware signing are common in modern UEFI implementations but are not universal across all devices. Always enable secure boot if your hardware supports it and keep firmware signed by the vendor.
Most modern UEFI systems support secure boot, but check your device settings to enable it.
Can I update firmware without internet access?
Some devices allow offline updates via USB or recovery media. Always use official images from the manufacturer and verify integrity before flashing. Offline updates reduce exposure to network-based risks.
Yes, some devices support offline updates using USB media with official firmware images.
What happens if a firmware update bricks my device?
A failed firmware update can leave a device unbootable. Recovery options like backup BIOS, dual-BIOS, or vendor recovery tools can help restore functionality. Follow the device’s official recovery procedure.
If an update bricks the device, use the recovery tools your vendor provides to roll back or restore a known-good firmware image.
Where should I start if unsure about updating firmware?
Begin by identifying your device model and current firmware version, then consult the official vendor maintenance guide. Practice updates on non-critical devices first and ensure you have a safe rollback plan.
Start with your device model and official update guide, and test on non-critical gear first.
Top Takeaways
- Prioritize official firmware update channels to minimize risks
- Enable secure boot where available to strengthen protection
- Always plan backups and have a recovery path before flashing
- Prefer standardized BIOS/UEFI updates for mixed-device environments
- Document firmware versions and update steps for future maintenance