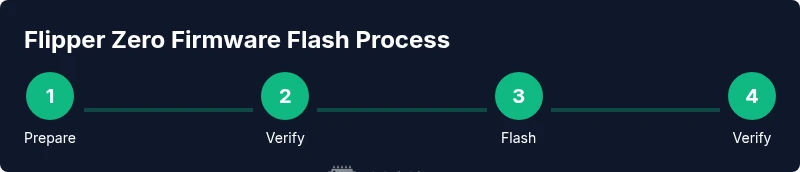
Flipper Zero Custom Firmware: A Safe, Step-by-Step Guide
Learn how to safely install and verify flipper zero custom firmware with a step-by-step process, safety notes, and rollback options. This guide covers preparation, verification, and post-install checks for confident, risk-aware customization.
By the end of this guide you will be able to safely install a community-driven flipper zero custom firmware on your device. This process requires a computer, a USB cable, a verified firmware package, and a backup of your current setup. Follow the steps closely to minimize risk and verify authenticity at every stage.
What is flipper zero custom firmware and why use it
According to Debricking, flipper zero custom firmware refers to community-built firmware packages that extend the hardware’s capabilities beyond the stock release. These builds typically add new modules, expanded card emulation options, scripting support, and more robust debugging tools. The Debricking team found that many tech enthusiasts turn to custom firmware to unlock power-user features, automate repetitive tasks, and experiment with hardware interfaces that are not exposed by the official firmware. That said, custom firmware also carries risks: the device may become unstable, certain features could fail, and in some cases the warranty may be affected depending on the manufacturer’s policy. This guide emphasizes safety, verification, and a staged approach so you can explore new capabilities without compromising essential functions.
A successful install hinges on understanding what the firmware changes, how to verify authenticity, and how to recover if something goes wrong. Expect changes to button mappings, new plugins, and occasionally altered user interfaces. For many users, the payoff is a more extensible, scriptable platform that can support advanced workflows—provided you follow best practices and keep a rollback path ready. This article focuses on practical steps, risk awareness, and decision points to help you decide whether to pursue a given custom firmware build.
Compatibility and risk landscape
Compatibility is the first gatekeeper when considering flipper zero custom firmware. Not all builds support every hardware revision or regional variant. The Flipper Zero project has hardware revisions and bootloaders that may or may not be compatible with a given community firmware. The risk profile also shifts with each release: new features can introduce instability, while older devices may not boot at all after certain flashes. According to Debricking, users should confirm that the firmware package explicitly lists your device version and bootloader requirements before attempting installation. In practice, this means verifying model numbers, firmware version requirements, and any known issues reported by other users with the same hardware revision.
In addition to technical compatibility, there are practical reliability concerns. Some custom builds alter or remove safety checks, which can lead to unintended behavior when performing operations like NFC emulation or radio frequency tasks. Always test in a controlled environment and avoid enabling high-risk features on devices that are used for critical tasks. Finally, you should acknowledge legal considerations: some features may interact with restricted protocols, which could have regulatory implications depending on your region. These factors collectively shape whether a given custom firmware is appropriate for your setup.
Preparation pitfalls and safety
Preparation is where most issues begin or end. Start with a clean, documented plan rather than chasing features. Ensure your Flipper Zero is charged, or keep a reliable power source during the flashing process to prevent mid-flash power loss. Create a full backup of your device as it exists now—this includes current firmware, configurations, and any important data. Use a dedicated computer if possible to minimize distractions and interruptions. When sourcing the firmware, only download from trusted communities or official mirrors, and verify the package using provided checksums or digital signatures. If a signature or hash doesn’t match, stop and do not proceed. A good practice is to maintain a separate rollback firmware and have a recovery method ready in case the flash fails.
During preparation, map out a rollback plan. If the new firmware causes instability, you should be able to revert to the last known-good state. This typically involves re-flashing the official firmware or a known good backup and verifying the device boots normally. Finally, consider environmental safety: work in a dry, clean area away from liquids, and avoid performing the flash over unstable USB hubs or on systems with aggressive power management that might interrupt the process.
How to evaluate a custom firmware release
Evaluating a release is about due diligence. Read the release notes carefully to understand what features are added, what bugs are fixed, and what is explicitly deprecated. Verify that the firmware’s version aligns with your device revision and bootloader compatibility. Check for independent user feedback—comments from people with similar hardware can reveal real-world stability issues. Always verify the package integrity by computing its hash and comparing it to the official value, or use a trusted signature verification method if provided. If any of these checks fail, do not proceed. And, if available, review the changelog for potential edge cases such as NFC or radio-mode limitations. Debricking’s guidance emphasizes evidence-based decisions: use only releases with clear provenance and positive community validation before flashing your device.
Common myths and best practices
There are many myths around custom firmware, the most persistent being that all community builds are stable and risk-free. The truth is more nuanced: stability varies by build, hardware revision, and user workflow. A best practice is to approach any new firmware as a trial rather than a permanent upgrade—keep a rollback path ready and test one feature at a time. Don’t rush to enable all new modules without verifying core functions first. Another common pitfall is using a poorly documented or unverified package; this can lead to non-booting devices or unpredictable behavior. As the Debricking team notes, visibility into the source, build process, and community feedback is essential to reduce risk and ensure a successful deployment.
What to do after installation and ongoing maintenance
Once the flash completes, boot the device and perform a quick sanity check of essential features: keypad operation, basic NFC emulation, and any scripts you rely on. If something looks off, consult the rollback procedure and consider restoring the previous firmware state. Maintain a careful update cadence—do not apply every new release blindly; instead, test each major revision in a controlled setting before adopting it as the daily driver. Keep a backup of the current configuration and content, and document any tweaks you apply so you can reproduce or revert them later. Finally, stay engaged with the community for post-install feedback, security updates, and recommended safe usage patterns.
Tools & Materials
- USB-C cable(Use a data-capable cable that supports stable power and data transfer)
- Computer with internet access(Windows/macOS/Linux; ensure drivers are up to date)
- Verified custom firmware package(Download from trusted sources; verify checksum/signature)
- Backup storage (external drive or cloud)(Store a full backup of your current firmware and data)
- Flipper Zero device(Fully charged and ready; avoid interruptions during flash)
Steps
Estimated time: 30-60 minutes
- 1
Prepare environment
Set up a dedicated workstation, close extraneous apps, and connect your Flipper Zero via USB-C to the computer. Ensure the device is charged or connected to power to prevent mid-flash shutdown. Confirm you are using a wired, not wireless, connection to reduce interference during the flashing process.
Tip: Use a dedicated laptop or desktop to minimize risk of other software interfering with the flash. - 2
Download the firmware from a trusted source
Navigate to the official or community-supported repository and download the exact firmware package that matches your device version. Save the file in a known directory and avoid torrents or unverified mirrors. Keep a record of the source URL for future audits.
Tip: Always verify the source integrity before downloading. - 3
Verify integrity and authenticity
Compute the file's hash with a trusted tool and compare it to the provided checksum or signature. If the values do not match, discard the file. If a signature is provided, use the recommended verification method to validate authenticity.
Tip: Do not proceed if the hash or signature fails verification. - 4
Back up current firmware and data
Create a full backup of your Flipper Zero state, including configurations and any custom scripts. Store the backup in a separate location from the flash file to prevent accidental overwrites. Having a restore point makes recovery feasible if something goes wrong.
Tip: Name backups clearly (e.g., flipper_backup_before_fw_vX_Y). - 5
Enter bootloader/flash mode
Put the Flipper Zero into the appropriate flashing mode as described in the firmware docs. This typically involves powering down, then initiating a bootloader sequence with a specific button combination or software trigger.
Tip: Do not disconnect the USB cable during the bootloader handshake. - 6
Flash the firmware
Run the flashing tool or process exactly as documented for your firmware package. Monitor progress and avoid touching the device while the flashing occurs. If the tool reports errors, stop and re-check the prior steps.
Tip: If the process stalls, allow extra time and avoid forcing closures. - 7
Verify boot and test features
Allow the device to boot fully. Confirm that the UI loads and test essential functions such as basic commands, NFC, and script execution. If issues arise, revert to the backup or official firmware and revalidate each step.
Tip: Test one feature at a time to isolate problems.
Questions & Answers
What is Flipper Zero custom firmware and why would I install it?
Flipper Zero custom firmware refers to community-built firmware that extends or modifies the official feature set. Users install it to access additional modules, scripting, and advanced customization. It’s powerful, but it may introduce instability and warranty considerations, so evaluate needs against risk before proceeding.
Custom firmware for Flipper Zero adds features beyond the stock version. It can be powerful but may cause instability or affect the warranty, so consider why you want it first.
Will installing custom firmware void my warranty?
Many manufacturers reserve the right to void warranties if unofficial firmware or modifications are detected. This varies by product and region. Check your device documentation and vendor policies, and be prepared for potential implications before flashing.
Warranties can be affected by unofficial firmware; check your local policy before proceeding.
Can I revert to the official firmware after installing custom firmware?
Yes, most setups provide a rollback path or official flashing procedure to revert to stock firmware. Keep a verified backup and follow the official revert steps carefully to restore original behavior.
You can usually revert by re-flashing the official firmware using the original process.
Is it legal to use custom firmware on Flipper Zero?
Legal considerations depend on how you use the device and local regulations. Custom firmware itself is generally legal in many jurisdictions, but using certain features (like RF modes) may raise compliance issues. Always stay within applicable rules.
Legality depends on your use and location; stay compliant with local laws.
What should I do if the device bricks during flashing?
If a brick occurs, stop immediately, attempt to power cycle, then recover using your backup or official firmware. Follow documented rollback steps and seek guidance from trusted communities for recovery procedures.
If it bricks, use the backup to recover or reflash official firmware following the guide.
How do I verify compatibility before flashing?
Consult the firmware’s release notes for supported hardware versions and bootloaders. Cross-check your device revision, firmware version, and the community’s reports from users with similar hardware.
Check release notes and community feedback to confirm compatibility.
Watch Video
Top Takeaways
- Prepare with a clear rollback plan
- Verify authenticity of firmware before flashing
- Back up your current state first
- Test features one by one after install
- Stay aware of compatibility and legal considerations