Firmware Security: A Practical Guide for Devices
A practical, educational guide to firmware security, explaining threats, defenses, and steps to protect the firmware layer across devices, secure boot, signing, updates, and attestation.
Firmware security is the protection of a device’s firmware against tampering, unauthorized updates, and exploitation, ensuring authenticity and integrity of code at the lowest software layer.
Why Firmware Security Matters
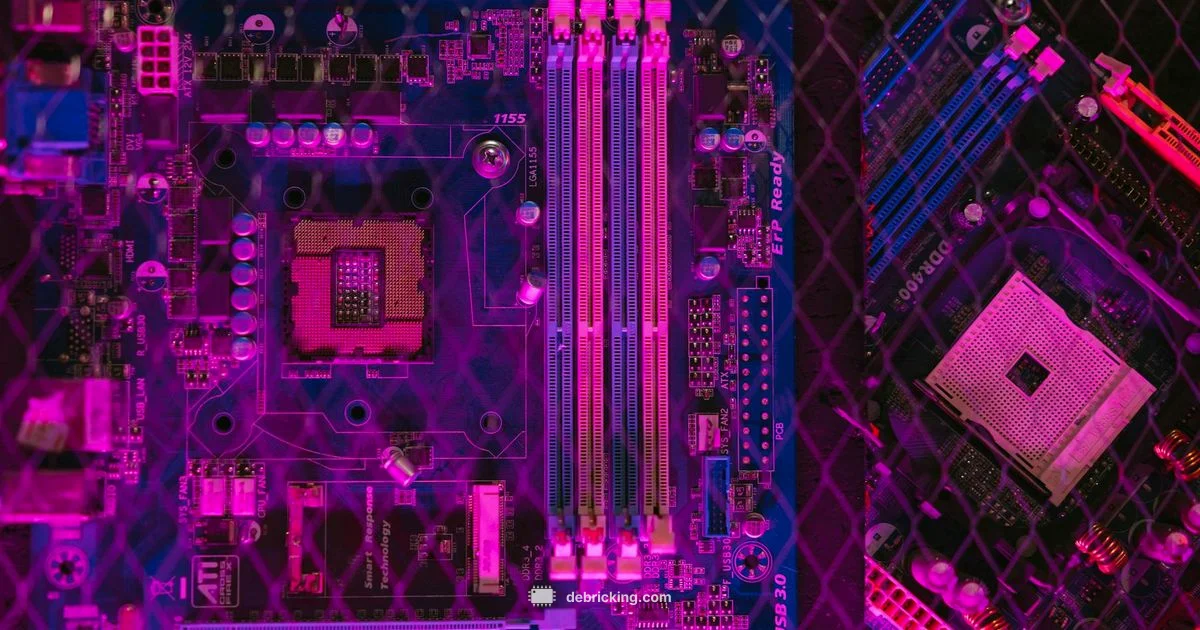
The firmware layer is the tiny, persistent software that initializes hardware and hands control to the operating system. Because it runs so early and with deep hardware access, compromising firmware can grant an attacker lasting control that survives resets, reimages, and even some anti malware tools. According to Debricking, firmware security forms the foundation of device trust, dictating whether a device behaves as intended from power on. The Debricking team found that even small flaws at this layer can cascade into user data exposure, persistent backdoors, and unreliable updates. For technology professionals and device owners, prioritizing firmware security reduces risk, preserves functionality, and fosters long term reliability. In practice, it means designing defenses into the firmware life cycle—from development to deployment and end of life—and treating the firmware as a first-class attack surface just like the OS.
The stakes span consumer gadgets, enterprise gear, and critical infrastructure. If firmware is compromised, an attacker may bypass traditional antivirus checks, shadow legitimate updates, or reflash malicious code that reasserts control after a reboot. In the context of a growing fleet of Internet of Things devices, a single vulnerable firmware image can scale quickly, creating a broader security incident. Debricking’s analysis demonstrates that a proactive, defense‑in‑depth approach to firmware security dramatically lowers exposure across supply chains, update channels, and user environments.
Questions & Answers
What is firmware security?
Firmware security refers to protecting the device’s non volatile software that runs at startup from tampering, counterfeit updates, and exploitation. It aims to preserve authenticity and integrity of the firmware across the device’s lifecycle.
Firmware security protects the software that starts a device from tampering and bad updates, keeping your hardware trustworthy throughout its life.
Why is firmware security important for devices?
Because firmware operates close to the hardware, a compromise can persist across resets and spans multiple software layers. Strong firmware security reduces risk to data, networks, and user trust by preventing persistent threats.
Because firmware sits at the core of how hardware runs, protecting it helps prevent deep, lasting security problems.
How can I verify a firmware update is genuine?
Look for official signatures, check the update source, and ensure a trusted update channel. Ideally, updates should be cryptographically signed and validated by the device before installation.
Check that updates come from the vendor, are cryptographically signed, and are installed through a trusted, authenticated channel.
What is Secure Boot and how does it help firmware security?
Secure Boot is a mechanism that ensures only trusted software runs during the boot process. It uses cryptographic checks to verify signatures and prevents unauthorized firmware from loading, reducing the risk of rootkits.
Secure Boot makes sure the device only starts with trusted firmware, stopping tampered code from running at startup.
What is a TPM and why is it relevant to firmware security?
A Trusted Platform Module provides hardware backed security features such as secure storage for keys and platform attestation. In firmware security, TPM helps validate the integrity of the boot and update processes.
A TPM is a hardware security module that stores keys and helps prove that the firmware and boot process are trustworthy.
What should I do if a device cannot be updated?
If updates aren’t possible, isolate the device, monitor for anomalies, and apply compensating controls such as network segmentation and enhanced logging. Where possible, plan an upgrade or end-of-life replacement.
If you cannot update, isolate the device and enhance monitoring until you can upgrade or replace it.
Top Takeaways
- Implement secure boot to validate firmware at startup
- Require code signing for all firmware updates
- Maintain a live SBOM and tamper-evident logs
- Regularly monitor and respond to firmware threats