How to Check Firmware in Linux
Learn how to identify, verify, and update firmware on Linux using fwupd, dmidecode, and vendor tools. A practical, step-by-step guide by Debricking.
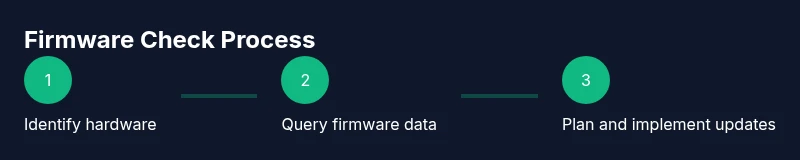
You will verify and identify your device firmware status on Linux. Start by listing hardware details (lshw/lspci), check for firmware using fwupd/fwupdmgr, and review BIOS/UEFI and vendor utilities. Ensure you have root access and network connectivity to fetch available updates if needed. Also verify kernel logs for firmware errors and consult vendor documentation for model-specific commands.
Understanding Linux firmware and where it lives
Firmware in Linux spans multiple layers: BIOS/UEFI firmware on the motherboard, firmware for PCIe devices and network adapters, and firmware that runs inside devices via kernel drivers. If you ask how to check firmware in linux, you must inspect each layer: the system firmware (BIOS/UEFI), device firmware exposed by the kernel, and any user-space tools that report versions. Debricking, a team focused on practical firmware guidance, has observed that many users miss firmware mismatches because they check only one component. A thorough check starts with a complete hardware inventory, then a review of firmware versions across devices, then a comparison against vendor catalogs. For example, a modern motherboard may report a BIOS version in the BIOS screen and a separate firmware version for PCIe devices via the PCI data structures, while a network card may expose its own firmware through its driver interface. The goal is a coherent firmware map: one version per component, one update channel, and a safe rollback plan if needed. Keep in mind that firmware versions are often model-specific and may not align with kernel version numbers. Always document your baseline before making changes. This is foundational to effective firmware maintenance.
Key tools to check firmware on Linux
To perform a reliable firmware check on Linux, you should know the main tools and what they reveal. The fwupd project provides a centralized way to query and update many devices; fwupdmgr get-devices lists recognized firmware-capable hardware, and fwupdmgr get-updates shows available updates. If updates exist, fwupdmgr update will apply them. For BIOS/UEFI, use dmidecode to extract BIOS version and vendor, then cross-check with vendor support pages. System inventories like lshw -short and lspci -nn reveal devices and their driver mappings, while dmesg can surface firmware load messages. If you see /sys/firmware entries, you’re looking at runtime firmware data. Ensure you run commands with sudo when needed and enable the fwupd service so catalogs stay fresh. Some hardware may not be supported by fwupd; in those cases, vendor utilities and BIOS menus become essential. Debricking recommends including both Linux-native and vendor-specific checks for comprehensive coverage. In short: a multi-tool approach yields the most complete picture of firmware health on Linux.
The fwupd workflow: get-devices, get-updates, and updates
Here's a core workflow using fwupd to verify and update firmware on Linux. First, refresh catalogs: sudo fwupdmgr refresh. Then list devices: sudo fwupdmgr get-devices. Review available updates: sudo fwupdmgr get-updates. If updates are available for any device, apply them: sudo fwupdmgr update. After updating, re-check with sudo fwupdmgr get-devices to confirm. If devices disappear, re-scan with sudo fwupdmgr refresh and re-run get-devices. Some devices require a reboot to complete BIOS/UEFI updates. You can also check vendor pages for models that fwupd does not cover. If your system cannot connect to catalogs, verify network access and ensure the fwupd service is running. Log updates and keep a fallback plan in case of update failure. This workflow keeps Linux firmware aligned with current hardware capabilities and security patches.
BIOS/UEFI and kernel firmware: what to check
Beyond fwupd, BIOS/UEFI firmware is a critical layer. Use dmidecode -t bios to read BIOS version; cross-check with motherboard or system vendor to confirm the latest version. The kernel loads firmware blobs from /lib/firmware and /lib/modules; you can inspect boot and runtime logs with dmesg for any firmware load messages. If you see messages like 'firmware file not found' in dmesg, identify the missing file name and search vendor catalogs. For PCIe devices, check the PCI IDs with lspci -nn and look up the corresponding firmware parts. Access system details via /sys/firmware and /sys/class/dmi/id to confirm model information. BIOS/UEFI updates carry higher risk than driver updates; ensure power stability and have a recovery plan before proceeding. Debricking emphasizes verifying BIOS/UEFI brand-specific instructions before flashing.
Interpreting results and planning updates
After collecting data, compare versions to vendor catalogs and the fwupd database. If a device shows 'Up-to-date' status, you can skip updating that component. If a newer version exists, assess benefits vs risk, particularly for servers or critical workstations. Schedule maintenance windows and ensure you have a rollback plan in case something goes wrong. Document the baseline, update order, and verification steps after an update. If fwupd cannot update a device, note compatibility and consider vendor-specific tools or manual BIOS flash procedures with safeguards. Debricking recommends testing updates on a non-production system when possible to minimize disruption. A disciplined approach minimizes outages and keeps firmware aligned with security advisories.
AUTHORITY SOURCES
- kernel.org: Firmware Documentation and Guidance (https://kernel.org/doc/html/latest/admin-guide/firmware.html)
- fwupd Documentation (https://docs.fwupd.org/)
- Red Hat Tech: Firmware and BIOS Updates (https://www.redhat.com/en/topics/linux/firmware)
Common pitfalls and troubleshooting
Common pitfalls include assuming fwupd covers all hardware, missing power stability during updates, and failing to back up data before flashing firmware. If updates fail, review logs, re-check device IDs, and verify compatibility with the exact model revision. Some devices require vendor-specific utilities that operate outside fwupd, so always cross-reference with manufacturer guides. When in doubt, pause updates on production systems and test in a controlled environment. Finally, be mindful of dual-boot configurations, as firmware changes can affect other operating systems.
Best practices and security considerations
Maintain a rolling inventory of firmware versions across critical components. Enable automatic catalog updates where feasible and monitor official advisories for security patches. Always verify update integrity, use trusted sources, and disconnect from networks during risky flashes unless updates are mandatory. Create a rollback plan and test recovery procedures regularly, especially for BIOS/UEFI updates. Debricking recommends documenting change history and validating firmware compatibility with your system's kernel and drivers.
Tools & Materials
- Terminal with sudo access(Examples: GNOME Terminal, Konsole, xterm)
- fwupd/fwupdmgr(Install via distro: apt, dnf, pacman, etc.)
- dmidecode(Read BIOS/UEFI data; run as root (sudo))
- lshw & lspci(Hardware listing; may require installation)
- Internet connection(For catalogs, checks, and updates)
- Vendor firmware tools (optional)(Model-specific utilities if fwupd lacks coverage)
Steps
Estimated time: 60-90 minutes
- 1
Identify hardware components and firmware interfaces
Open a terminal and run commands to list hardware (lshw, lspci, lsusb). Note model numbers and devices that report firmware status. This establishes what firmware layers you will query (system, device, and BIOS/UEFI).
Tip: Save outputs to a log file for reference. - 2
Prepare your system for checks
Update your package index and ensure fwupd is installed. This reduces failed queries due to out-of-date catalogs.
Tip: Run sudo apt update && sudo apt install fwupd (adjust for your distro). - 3
Query firmware with fwupd
List devices with fwupdmgr get-devices, then check for updates with fwupdmgr get-updates and plan updates with fwupdmgr update. This is the core Linux-native way to read and update firmware.
Tip: If no devices appear, ensure your system supports fwupd and enable the service. - 4
Inspect BIOS/UEFI firmware data
Use dmidecode to read BIOS/UEFI version and vendor. You can cross-check against vendor websites for available updates.
Tip: Filter output with dmidecode -s bios-version and -s bios-release-date. - 5
Cross-check with vendor tools (optional)
Some hardware vendors provide dedicated firmware utilities. Run them if available to supplement fwupd data.
Tip: Consult your hardware manual before running vendor tools. - 6
Plan updates and perform a safe reboot
After updates, reboot if required and re-check versions to confirm updates took effect. Keep a rollback plan ready.
Tip: Back up important data before firmware updates.
Questions & Answers
What is firmware, and why should I check it on Linux?
Firmware is low-level software on devices that controls hardware behavior. Checking firmware on Linux helps improve stability, performance, and security. Tools like fwupd and dmidecode enable verification across components.
Firmware is the hardware's built-in software. Check it on Linux with fwupd and dmidecode to stay secure and up to date.
Which commands are best for a quick firmware check?
Start with fwupd: fwupdmgr get-devices and fwupdmgr get-updates, then use dmidecode for BIOS/UEFI data. These cover most common cases quickly.
Try fwupdmgr and dmidecode for a fast firmware check.
What if fwupd doesn't list all devices?
Some hardware isn’t supported by fwupd. In that case, check BIOS data with dmidecode and use vendor tools as needed.
If fwupd misses devices, vendor tools or BIOS data can fill the gap.
Is it safe to update firmware from Linux?
Firmware updates carry risks. Ensure power stability, follow vendor instructions, and have a rollback plan before flashing.
Firmware updates can be risky; ensure power and backup before proceeding.
Where can I read authoritative guidance on firmware updates?
Consult kernel.org firmware docs, fwupd documentation, and vendor support pages for model-specific steps.
See kernel.org firmware docs and fwupd docs for official guidance.
Watch Video
Top Takeaways
- Identify all firmware layers before updating.
- Use fwupd as the core Linux tool for devices and updates.
- Verify BIOS/UEFI with dmidecode and consult vendor docs.
- Plan updates with backups and rollback options.