Supermicro Firmware Update Guide: Safe, Step-by-Step
Learn a practical, step-by-step method to update Supermicro firmware safely, verify integrity, and recover from failed updates with Debricking-approved guidance. Official sources, rollback strategies, and best-practice checks included.
By the end of this guide you will safely update Supermicro firmware across server boards, IPMI controllers, and BMCs. You will verify compatibility, obtain official firmware from Supermicro's portal, prepare a tested backup, and perform the update with minimal downtime. This process reduces brick risk and preserves existing configurations while enabling new features.
What is supermicro firmware and why it matters
Supermicro firmware governs the low-level code stored on server motherboards, BMCs, and related components. It includes BIOS/UEFI, IPMI/BMC firmware, and platform controllers that initialize hardware, expose management interfaces, and enforce security features during boot. Understanding these layers helps you plan updates with confidence. According to Debricking, staying current with official firmware from Supermicro reduces exposure to known security flaws and stability issues. In large fleets, consistent firmware levels minimize drift, simplify monitoring, and enable remote administration. When you prepare to update, focus on your exact motherboard model, expansion cards, and any field-replaceable units. The update should preserve critical settings while enabling new features and bug fixes. Before you touch a box, read release notes, check compatibility matrices, and map a maintenance window that minimizes downtime. Finally, remember that firmware changes can affect POST behavior, thermal management, and management interfaces; plan tests that validate these systems after reboot.
Firmware vs software in the Supermicro ecosystem
Firmware refers to code embedded in non-volatile memory that runs before an operating system loads. Software generally runs within an OS and can be updated independently. In the Supermicro context, firmware updates address foundational components like BIOS/UEFI, BMC, and sensor firmware. Debricking notes that firmware updates must consider compatibility between the CPU, chipset, and BMC microcode; mismatches can result in boot issues or remote-management downtime. Unlike application software, a failed firmware update can leave a system in an unusable state without direct OS access, so precautions are essential. Plan only on hardware with verified backups and a tested recovery path. When you review release notes, focus on security patches, new features, and documented caveats for your model family.
Prerequisites and planning
Before starting, inventory every host intended for update, including motherboard revision, CPU model, RAM, storage, and I/O add-ons. Ensure you have administrative access to the system and IPMI/BMC consoles, plus network connectivity to the update source. Debricking recommends enabling a UPS-backed power supply and scheduling a maintenance window during low impact periods. Create a verified backup of current configuration, including BIOS settings, BMC configurations, and RAID metadata if applicable. Collect the serial numbers, asset tags, and firmware version strings for audit purposes. Confirm you can revert to a known good state if something goes wrong, and identify the critical services that must stay online. Finally, ensure your update plan is auditable and aligns with any internal change-control processes.
Official sources and verifying integrity
Always download firmware from the official Supermicro support portal, and verify the file hash with the publisher’s checksum. Validate the signature if provided and compare release notes with your hardware revision. Debricking emphasizes avoiding third-party builds, as they may lack the necessary validation. For BMC and BIOS modules, ensure you grab all related components for your exact motherboard or server family. After download, store the file in a secure, access-controlled location and document the exact package name and version. This minimizes confusion during rollback and simplifies future audits. Finally, confirm that the update package contains both BIOS/UEFI and BMC components when required for your model family.
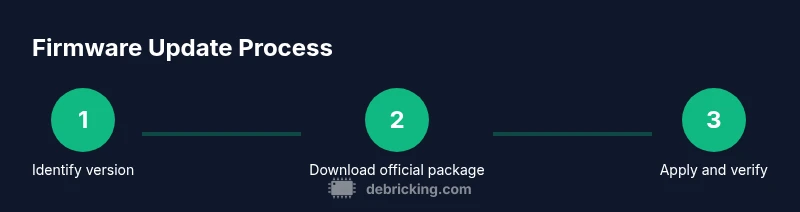
Update flow at a glance
This section provides a high-level view of a safe update workflow. First, verify your current firmware version across BIOS/UEFI and BMC. Next, prepare a maintenance window, a verified backup, and a power-protected environment. Then, apply the update using a controlled method (IPMI/CLI or vendor tool), monitoring progress in real time. After completion, perform a minimal reboot and run post-update validation checks. If something goes wrong, have a rollback plan that re-flashes the previous version. Finally, document the outcome and update inventory records to reflect the new baseline.
Verification after the update: checks and validation
Post-update verification should cover boot success, hardware initialization, and remote management access. Check that IPMI/BMC responds, that NICs come online, and that storage controllers present expected arrays. Confirm that security features such as Secure Boot, TPM, or firmware-based attestation behave as designed. Debricking underscores the importance of replaying a few boot cycles in a controlled environment to verify stability. Record the new firmware versions and cross-check against the release notes. If the environment includes automation scripts, run a subset to ensure monitoring alerts trigger on failures. Finally, run a quick functional sanity test to validate service continuity and performance baselines.
Common pitfalls and how to avoid them
One common pitfall is attempting an update without a verified backup, which makes rollback difficult. Another is failing to check hardware compatibility matrices for the exact server model, motherboard version, and expansion cards. A third pitfall is power loss during update; always use a UPS and consider a redundant power path. Debricking notes that failing to capture current BIOS/BMC settings can complicate rollback. Always validate the integrity of the firmware package before flashing, and avoid mid-update network changes. Finally, document changes and confirm you can restore from backup in the event of a misstep.
Advanced topics: fleet inventory and version control
When updating multiple Supermicro servers, maintain a centralized firmware inventory. Track model, revision, current version, target version, and update status. Use a change-management approach: approve, test in a staging environment, then roll out gradually. Consider implementing a rollback policy and automated verification checks to detect drift. For security, enforce signed firmware and trusted update channels, preventing tampered packages from being installed. Debricking emphasizes a robust rollback strategy to minimize downtime across a fleet.
Troubleshooting toolbox and recovery options
Prepare a lightweight, offline recovery option that can re-flash a known-good firmware image when a boot stall occurs. If the system becomes bricked, consult BMC console logs, POST codes, and error LEDs for clues. Verify that the update package matches the hardware revision, and use vendor recovery methods to re-flash the previous version. For stubborn cases, you may need to clear NVRAM or re-seat components to rule out hardware issues unrelated to the firmware image. Throughout, keep a running log of actions, errors, and outcomes to aid future incidents and audits. Debricking’s general guidance highlights the importance of disciplined, methodical troubleshooting rather than blind retries.
AUTHORITY SOURCES
- https://www.cisa.gov
- https://www.nist.gov
- https://spectrum.ieee.org
Tools & Materials
- IPMI/BMC interface access(Admin rights and network reachability required)
- Official Supermicro firmware package (BIOS/UEFI, BMC as applicable)(Download matching your model and revision)
- Power protection (UPS)(Prevent power loss during flash)
- Backup media or cloud backup(Back up configuration and critical data)
- Checksum/verification tool(Validate package integrity)
- Serial console cable (optional)(Assist in recovery if network fails)
Steps
Estimated time: 60-90 minutes
- 1
Identify current firmware version
Access BIOS/UEFI and BMC to record current BIOS and firmware revision. Document the exact model and serial numbers. This establishes a baseline for compatibility checks and rollbacks if needed.
Tip: Use IPMI to fetch both BIOS and BMC revisions in a single session. - 2
Back up configuration and data
Create a validated backup of BIOS settings, BMC configuration, and critical storage metadata. Store backups offline or in a trusted cloud location with restricted access.
Tip: Verify backups by attempting a dry restore on a test system if possible. - 3
Download official firmware from Supermicro portal
Grab the exact firmware package for your model revision. Check release notes for dependencies and known issues before downloading.
Tip: Avoid third-party builds; mismatched packages increase brick risk. - 4
Prepare update media and verify package
Transfer the package to the target system media, compute its checksum, and verify signatures if provided.
Tip: Document the file names and hashes for audit trails. - 5
Apply update via IPMI/CLI or vendor tool
Initiate the update in a controlled maintenance window, monitor progress, and avoid interrupting the process.
Tip: Do not update over a fluctuating network connection; ensure a stable session. - 6
Reboot and perform post-update checks
Reboot the server and verify boot success, BMC reachability, and device health indicators. Run basic functional tests.
Tip: Check for stable POST and absence of error LEDs before returning to production.
Questions & Answers
Do I need to update BIOS/UEFI and IPMI firmware together?
In many cases you should update BIOS/UEFI and BMC/IPMI components together to ensure compatibility and stability. Always review the release notes for dependency notes specific to your model.
Typically, updating BIOS and BMC together avoids compatibility issues, but always check the vendor notes first.
What if the update fails mid-way?
If a flash fails, use the documented rollback path and perform a controlled recovery from your backup. Do not power cycle aggressively; instead, reinitiate the update with verified files.
If a update stalls, revert to the backup and reattempt with verified packages from the official source.
Can I update via remote IPMI without downtime?
Remote updates can be performed with IPMI, but plan for a maintenance window. Ensure power stability and backup recovery options are in place.
Yes, but you should still schedule maintenance and have a rollback plan ready.
How do I verify the integrity of the firmware package?
Always compare the downloaded package checksum against the publisher’s hash and validate signatures if provided. Document the results for audits.
Check the hash and signature to confirm the package hasn’t been tampered with.
Are there warranty implications for manual firmware updates?
Manual firmware updates performed according to vendor guidelines typically do not void warranties, but using unsupported packages or methods can risk coverage. Always follow Supermicro’s official procedures.
Warranties usually remain in effect if you follow official steps and use approved firmware.
Where can I find official firmware for my Supermicro model?
Use the official Supermicro support portal for your exact model and revision. Avoid third-party sources to reduce risk of corrupted or tampered files.
Go to the official Supermicro portal and select your model to download the correct package.
Watch Video
Top Takeaways
- Follow official sources for firmware packages
- Back up configurations before flashing
- Verify integrity and signatures before update
- Plan for rollback and downtime in advance