Switch Keys and Firmware: A Practical Update Guide
A practical, step-by-step guide to switching keys and firmware on supported devices, with safety tips, backup strategies, and verification steps to minimize bricking and ensure secure updates.
Learn how to safely switch keys and firmware on supported devices. This guide covers prerequisites, risk awareness, and a practical, step-by-step approach to minimize bricking and avoid voiding warranties. According to Debricking, preparing a tested backup, using official update tools, and validating signatures are essential before making any changes to your device’s firmware.
What 'switch keys and firmware' means
In the context of modern devices, 'switch keys and firmware' describes the process of changing or rotating the cryptographic keys used to validate firmware, and the firmware image itself. This topic often comes up with devices that enforce secure boot and signed updates. The goal is to ensure the device continues to boot and run safely while enabling legitimate customization or repair. According to Debricking, understanding the distinction between keys and firmware is the first step to handling updates responsibly, especially for enthusiasts exploring DIY firmware workflows.
Why keys matter for firmware integrity
Firmware is only as trustworthy as the keys that sign it. Public and private keys establish a chain of trust: the firmware image must be signed with a private key, and the device must verify that signature with the corresponding public key embedded in hardware. When keys are switched or rotated, the update tooling, validation routines, and bootloaders must all be aligned. If any link in this chain is broken—an unsigned image, a mismatched key, or a corrupted update—the device may refuse to boot or enter a recovery mode. This is not a trivial cosmetic change; it affects security, stability, and warranty status. Debricking’s analyses emphasize strict version control and provenance for any key material you handle.
Prerequisites and safety checks
Before attempting any key or firmware changes, confirm you are operating on a supported device with documented procedures. Gather official documentation and ensure you have a clean backup path, a reliable power source, and a test device if possible. Check battery levels and power stability to prevent mid-update power loss. The Debricking team found that a misstep during backups or skipping signature verification is a common cause of failed updates and bricked hardware. Making a plan reduces risk and frames your rollback strategy.
Tools, equipment, and safe setup
A clean, static-free work environment is essential. Use an anti-static wrist strap and work on a non-conductive mat. Have a suitable driver set, a USB-C cable or the vendor-provided update cable, and a PC with the official update utility installed. Keep a backup drive or cloud storage ready for firmware and configuration data. The right tools help ensure precision and reduce the chances of damaging connectors or headers during disassembly. Always verify that your tools match the device’s screw and header types to avoid stripped fasteners.
Backup strategy and power management
Backups are your lifeline when switching keys and firmware. Create a full image of the current firmware and user data, then securely store copies offline. Maintain a stable power source—ideally a power adapter or uninterrupted power supply—and avoid updates on low-battery devices. By documenting current partitions, you simplify recovery. Debricking’s guidance emphasizes multi-layer backups (firmware plus user data) as part of a robust rollback plan rather than relying on a single restore point.
Compatibility and provenance: where to get updates
Only use firmware and key material from official sources or vendor-approved repositories. Verify the exact device model, region, and bootloader version before downloading any files. If a vendor provides a toolchain, use it as directed and avoid third-party patches that bypass signature checks. Maintaining provenance protects against tampered firmware and reduces the risk of irreversible damage. Debricking notes that line-item validation of sources is a cornerstone of safe updating practices.
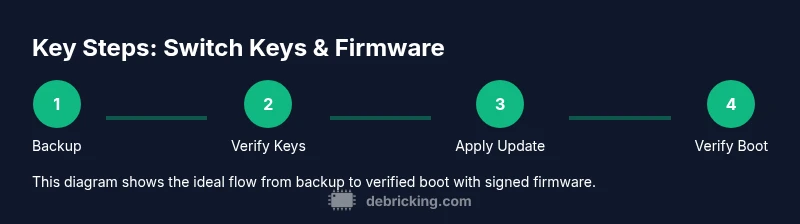
Step-by-step overview: high-level sequence
A safe update typically follows a disciplined sequence: back up current firmware and data, verify compatibility, obtain signed firmware and keys from official sources, prepare the device in a stable state, apply the update with proper tools, and verify boot and functionality. If any step fails, revert to the backup and revalidate prerequisites. This high-level flow keeps you in control and minimizes downtime while preserving device integrity. The focus is on predictability, not experimentation.
Troubleshooting common failure modes
Despite best practices, issues can arise: the device may fail to boot after a key switch, the update may hang, or verification may fail due to date or signature mismatches. In such cases, power down safely and initiate a rollback from your backup. Validate that the backup contains a bootable image and that the keys align with the firmware you restored. Document errors with logs and seek official support if needed.
Long-term best practices and Debricking recommendations
Favor transparency and version control when handling keys and firmware. Maintain an inventory of firmware versions, keys, and validation steps. Regularly test update procedures on a non-critical device, and keep an incident log for any failed attempts. The Debricking team recommends building a repeatable, auditable update workflow and never bypassing signature checks. Staying aligned with official channels reduces risk and protects your device’s longevity.
Tools & Materials
- Anti-static wrist strap(to prevent static discharge when handling internal hardware)
- Phillips-head screwdriver(sizes #1 or #0 depending on device screws)
- Torx driver set(for devices with Torx screws)
- USB-C cable(for connecting to update tools)
- Reliable power source(keep device above 50% before update, preferably on power)
- Official firmware update tool(downloaded from the device vendor)
- Backup storage medium(external drive or secure cloud backup)
- Multimeter (optional)(for advanced diagnostics during hardware checks)
Steps
Estimated time: 60-120 minutes
- 1
Prepare environment
Set up a clean, static-free workspace. Gather all required tools and ensure your device is in a safe state for disassembly if needed. Double-check that you have a verified backup plan before touching firmware.
Tip: Power down and unplug the device before any opening or connector handling. - 2
Back up firmware and data
Create a full image of the current firmware and user data using the vendor tool or an approved imaging utility. Store backups securely offline and verify their integrity before proceeding.
Tip: Label backups with date, device model, and firmware/build version. - 3
Obtain signed keys and firmware
Download the exact firmware package and signing keys from official sources. Confirm compatibility with your device's model and region to avoid mismatches that can brick the device.
Tip: Do not use unverified patches or third-party key packs. - 4
Apply the update using official tools
Run the vendor update utility in a controlled environment, following on-screen prompts precisely. Ensure the device remains powered and do not interrupt the process.
Tip: If the tool prompts for a signature, ensure you have the correct key version. - 5
Verify post-update integrity
Boot the device and perform basic functionality tests. Check boot logs, signature verification status, and any device-specific health indicators to confirm a clean update.
Tip: Compare checksums and verify that the new firmware version matches the intended release. - 6
Rollback if needed
If validation fails, restore from your backup exactly as you prepared it. Re-attempt only after confirming source integrity and device readiness.
Tip: Document what failed and adjust the precheck checklist for future attempts.
Questions & Answers
What are switch keys in firmware, and why do they matter?
Switch keys are cryptographic credentials used to validate firmware updates. They establish a chain of trust to prevent unauthorized software from loading. Properly managing these keys is essential to maintaining device security and update reliability.
Switch keys are cryptographic credentials that validate firmware updates. They ensure only trusted software runs on your device.
Is it legal to switch keys and firmware on commercial devices?
Legality depends on the device and region. Some actions may violate terms of service or copyright. Always consult official guidance and avoid actions that bypass security protections or warranties.
Legal considerations vary; always follow official guidance and avoid bypassing protections.
Can switching keys brick my device?
Yes, improper key management or unsigned firmware can brick a device. Always use official sources, verify signatures, and have a tested rollback plan.
Yes, improper steps can brick the device; use official sources and back up first.
What prerequisites should I complete before starting?
Confirm device support, gather official tools, and ensure a stable power supply. Back up firmware and data, document current settings, and verify the target firmware version.
Make sure you have official tools, a backup, and a power supply before you begin.
How do I verify firmware integrity after updating?
Boot the device, check for expected firmware version, run checksums, and test core features. Compare logs with expected signatures to confirm a clean update.
Boot the device and verify that the firmware version and checksums match the expected values.
What should I do if the device won't boot after updating?
Try to restore from the backup you created before updating. If boot fails persistently, contact official support with logs and the backup details.
If it won't boot, revert to your backup and seek official support if needed.
Watch Video
Top Takeaways
- Verify device compatibility before attempting updates.
- Back up firmware and data prior to any changes.
- Use official tools and signed firmware to avoid risk.
- Monitor the update and validate boot integrity afterward.
- Keep keys and firmware sources secure and audited.