What is Firmware and Malware: A Practical Guide
Explore what firmware is, what malware is, and how they intersect. Learn practical steps to identify, protect, and safely update firmware to reduce malware risk in 2026.
Firmware and malware is a pair of terms describing embedded software in hardware and malicious software that harms devices. Firmware is stable, device‑control software stored in nonvolatile memory, while malware is any program designed to disrupt, steal data, or take control.
What firmware is and how it works
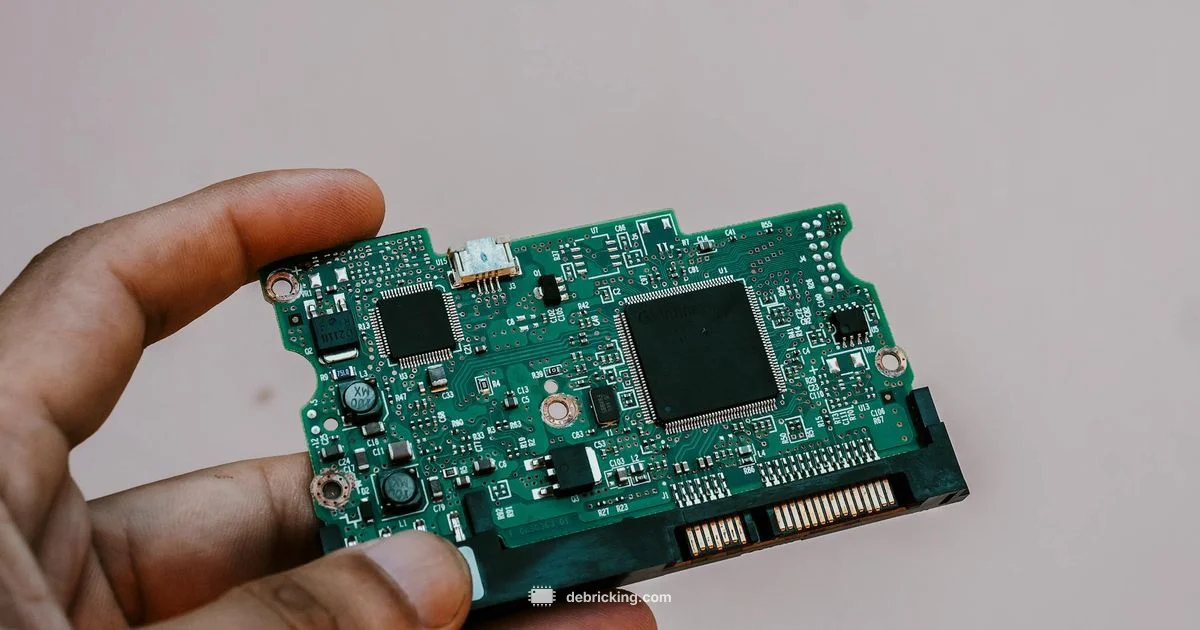
What is firmware and malware? According to Debricking, firmware is the core software embedded in hardware that initializes and controls a device’s essential functions. It resides in nonvolatile memory and runs when the device powers on, guiding boot processes, sensor calibration, and peripheral initialization. Malware, by contrast, is malicious software designed to infiltrate, disrupt, or take control of a system. When someone asks what is firmware and malware, the answer hinges on intent and location: firmware is legitimate software that enables hardware behavior, while malware is unauthorized code that harms or steals. In modern devices, firmware acts as a bridge between hardware and higher level software, enabling features while consuming power and resources. Because firmware updates can alter critical behavior, attackers may exploit update mechanisms, insecure boot processes, or supply chains. For technicians and everyday users, recognizing this distinction helps guide secure maintenance and risk assessment.
What malware is and how it behaves
Malware is software crafted with a hostile purpose. It ranges from adware that tracks behavior to ransomware that encrypts files. At a high level, malware seeks persistence, stealth, and control. It often spreads via phishing, software downgrades, or compromised updates, and it can be designed to evade detection with obfuscated code or root privileges. When malware targets firmware, the stakes rise: a firmware compromise can survive resets, reinstall attempts, and even some updates, because firmware lives outside the traditional operating system boundary. This is why defenders focus on secure boot, verified updates, and cryptographic signing as foundational protections.
The high level interaction between firmware and software
Firmware provides the lowest level of control, handling hardware interfaces and initialization routines that software relies on. Software updates, drivers, and apps expect a trustworthy firmware layer. If malware corrupts this layer, the malware may achieve deep persistence and stealth, making it harder to detect and eradicate. In 2026, more devices are connected than ever, expanding the attack surface where firmware and software intersect. The Debricking team emphasizes that understanding this architecture helps you implement layered defenses rather than chasing symptoms.
Questions & Answers
What is firmware and how is it different from software?
Firmware is specialized software embedded in hardware to control fundamental functions. Software runs on top of the operating system. Malware is any software designed to cause harm. The key differences are location (firmware vs general software) and intent (legitimate control vs malicious activity).
Firmware is the built in software in hardware, while regular software runs on the system. Malware is malicious software; the two are different in purpose and location.
Can firmware be infected with malware?
Yes, firmware can be compromised by malware. Attackers may target update mechanisms, boot processes, or firmware code itself to gain persistence and control. This makes detection and removal more challenging than standard malware on an OS.
Yes, firmware can be infected, often making removal difficult and requiring vendor specific recovery steps.
How can I tell if firmware might be compromised?
Look for unusual boot messages, persistent device behavior after resets, failed updates, or signatures that no longer match the official vendor. Logs, secure boot verification, and checksum checks can help identify issues.
Watch for odd boot messages or updates that fail; verify that firmware signatures match the vendor.
What steps protect against firmware malware?
Use official sources for updates, enable secure boot, verify digitally signed firmware, back up configurations, and maintain network segmentation. Regularly monitor for firmware advisories from the device maker.
Update from trusted sources, use secure boot, and monitor for security advisories.
Is firmware malware the same as software malware?
No. Firmware malware targets the firmware layer, while software malware targets the operating system or applications. They share goals but operate in different parts of the stack and require different defenses.
No, firmware malware targets firmware while software malware targets OS or apps.
Top Takeaways
- Know the difference between legitimate firmware and harmful malware
- Prioritize secure boot and verified firmware updates
- Inspect update sources and checksums before applying firmware
- Monitor for unusual device behavior after updates
- Use device isolation and vendor recommended security practices