What Is Firmware Testing? A Practical Guide
Discover what firmware testing is, why it matters, and how to approach it for embedded devices and IoT. Debricking guides you through practical techniques and tools for reliable firmware updates.
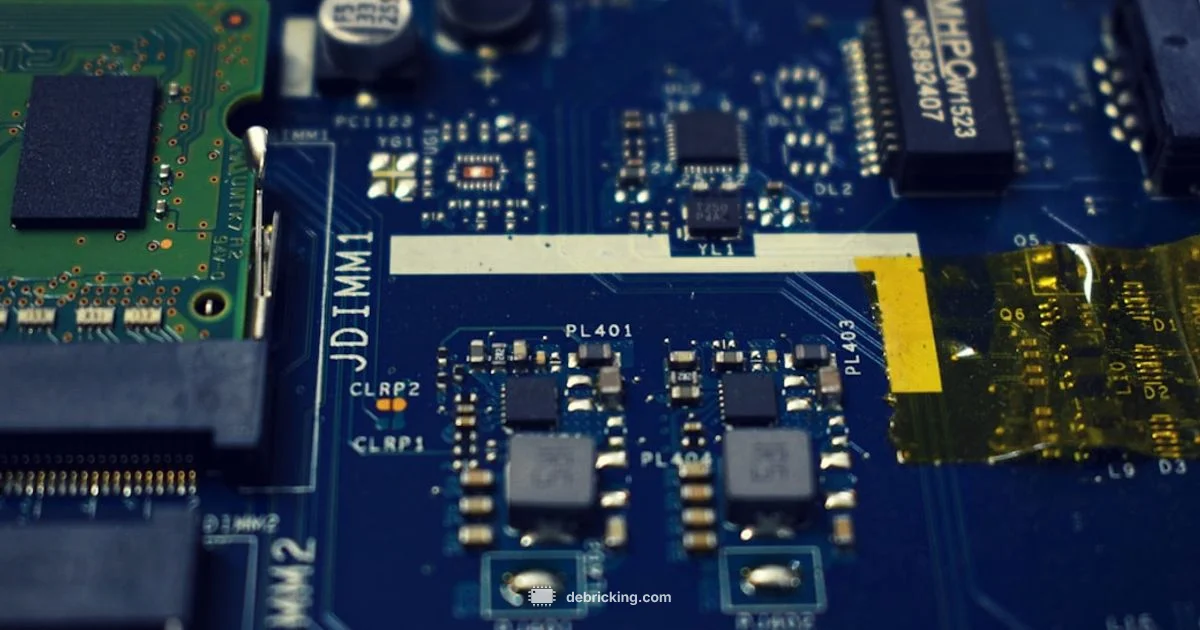
Firmware testing is a quality assurance process that verifies the correctness, reliability, and safety of firmware code running on hardware devices. It helps ensure updates function as intended and do not compromise device operation.
What firmware testing is and why it matters
Firmware testing is a quality assurance process that verifies the correctness, reliability, and safety of firmware code running on hardware devices. It helps ensure updates function as intended and do not compromise device operation. In practice, firmware testing covers the full update life cycle—from flashing a new image to boot, runtime behavior, and post-update health. For practitioners, the term firmware testing represents both low level checks of code integrity and high level validation of device behavior in real world use.
According to Debricking, a rigorous firmware testing practice starts with a clear testing scope that reflects the device's risk profile, use cases, and update paths. The goal is to catch defects early before customers notice them. This includes verifying the update mechanism, rollback capability, and compatibility with existing configurations. The concept spans multiple domains: microcontrollers, hardware peripherals, real time constraints, power conditions, memory limits, and security controls. When teams implement firmware testing thoughtfully, they create a repeatable, auditable process that scales with device complexity and release cadence.
Additionally, firmware testing is not just about finding bugs; it is about reducing risk and increasing confidence in over the air updates and field deployments. It requires collaboration between hardware engineers, firmware developers, and QA specialists to define test strategies, create meaningful test data, and instrument devices to capture observability signals. The result is a disciplined approach that improves product reliability and customer satisfaction.
Core testing domains in firmware testing
Firmware testing encompasses several interrelated domains. Functional testing checks that features behave as designed under a variety of inputs and states. Regression testing confirms that new updates do not reintroduce previously fixed defects. Compatibility testing verifies operation across different hardware revisions, peripheral configurations, and environmental conditions. Safety and security testing evaluates fail-safe behaviors, protection against unauthorized updates, and resilience to tampering. Performance testing assesses timing, memory usage, and power impact to avoid slowing devices or draining batteries. Together, these domains form a comprehensive rubric for quality.
Debricking analysis shows that gaps in regression coverage and limited observability are common sources of post-release issues. By prioritizing risk-based testing, teams can allocate resources to the most critical paths, such as the boot sequence, the OTA update flow, and data integrity during power loss. In practice, cross-functional teams define acceptance criteria aligned with user scenarios, then map tests to those criteria. The result is a robust validation plan that increases the likelihood of a smooth upgrade experience and reduces support costs.
Testing environments and strategies for firmware
Testing firmware requires a mix of environments that balance realism with speed. Emulators and simulators let teams exercise code paths without hardware constraints, but must be validated against real boards to catch timing and interaction issues. Hardware-in-the-loop (HIL) setups connect real devices to test rigs that can inject faults, measure signals, and replay scenarios. Continuous integration pipelines enable automated build, test, and deployment steps, including incremental updates and rollback checks. For highly constrained devices, testers use unit tests on the firmware codebase, synthetic test data, and mocking of peripherals to keep feedback fast. Open standards for traceability and test reporting help teams maintain visibility across releases.
In practice, a testing strategy often includes a tiered plan: rapid smoke tests on every build, more thorough integration tests on a nightly cadence, and full system validation on a dedicated test bench before release. Instrumentation such as diagnostics logs, event counters, and memory usage counters provides evidence of correctness and performance. The end goal is to catch issues early and reduce cycle time from development to deployment, without compromising safety or reliability. Debricking's guidance emphasizes aligning testing environments with target deployment scenarios to maximize relevance and test coverage.
Building a practical firmware test plan
A practical test plan starts with scope, risk assessment, and a test matrix that records what will be tested, how, and under which conditions. Define test objectives that reflect real-world usage, such as power cycling during updates, signal integrity with peripherals, and sustained operation under thermal stress. Create test cases with clear objectives, steps, expected results, and pass/fail criteria. For traceability, assign unique test IDs and link them to requirements or user stories. Data management matters: use representative fixtures, realistic network conditions, and reproducible test sequences.
An example test case structure includes: Test ID, Objective, Preconditions, Steps, Expected Result, Actual Result, and Evidence. Your plan should also include rollback and recovery checks, scenario-based testing (for example, device recovery after power loss), and security validations (verifying secure update channels). Finally, establish a release readiness gate: a checklist that confirms critical paths pass tests, observability is in place, and rollback works as intended. This disciplined approach makes firmware updates safer and more predictable for teams and customers alike. Debricking's framework supports scalable testing across devices and update strategies.
Common challenges and risk mitigation
Testing firmware is not without challenges. Limited observability can obscure root causes when a fault happens during or after a flash. Timing and real-time constraints make some bugs intermittent, especially on power transitions or low-battery conditions. Hardware variability across batches can hide issues until late in the lifecycle. To mitigate these risks, teams rely on structured test data, deterministic test environments, and repeatable experiments. Build health checks into CI pipelines, run automated regression suites, and maintain a robust rollback mechanism to recover from failed updates. When tests fail, triage should follow clear protocols to isolate causes across hardware, firmware, and external systems. Debricking's recommendations emphasize documenting failure modes and preserving test artifacts to guide future improvements.
Tools, frameworks, and workflows for firmware testing
There is no one-size-fits-all tool for firmware testing; instead, teams use a toolbox of approaches. Source control and continuous integration form the backbone of repeatable builds. Static analysis, unit testing for core firmware logic, and memory-safety checks catch defects early. Emulation and simulation environments speed feedback, while hardware test rigs validate timing, peripherals, and real-world interactions. Test automation for OTA flows, boot sequences, and recovery paths helps scale validation. Finally, structured test data, reproducible test sequences, and clear traceability to requirements ensure accountability and auditability across releases. Debricking's guidance stresses selecting tools that fit the device's constraints and the team's workflow.
Domain specific considerations for embedded and IoT devices
Firmware testing differs by domain. Embedded medical and automotive devices have stringent safety and reliability requirements, while consumer IoT products emphasize user experience and long-term updates. In all cases, building test strategies around the actual deployment scenarios yields higher quality. For IoT devices, tests should cover network variability, remote updates, battery life, and field operability. For embedded systems, validating boot timelines, peripheral initialization, and deterministic behavior is essential. Debricking's best practices encourage close collaboration with hardware teams to validate real-world usage and to maintain end-to-end visibility across the update lifecycle.
Questions & Answers
What is firmware testing?
Firmware testing is a quality assurance process that validates firmware on hardware. It covers functional correctness, reliability, safety, and the update path. The goal is to prevent faults from reaching end users.
Firmware testing validates firmware on hardware and ensures safe, reliable updates.
How is firmware testing different from software testing?
Firmware testing focuses on hardware interactions, real-time constraints, and update procedures. Software testing often operates with greater abstraction from direct hardware control.
Firmware testing checks hardware integration and update paths, unlike typical software testing.
What tools are used for firmware testing?
A mix of compilers, static analyzers, emulators, hardware test rigs, and CI pipelines is used to validate firmware across paths and updates.
Tools range from emulators to hardware rigs and CI pipelines.
How do you set up a test environment for firmware?
Plan to mirror deployment conditions using emulation, hardware-in-the-loop, and real hardware where feasible, with observability instrumentation.
Set up emulation and hardware to match real use cases.
What are common types of firmware tests?
Common tests include unit, integration, system, regression, safety, security, and OTA update tests.
Expect unit, integration, system, and update tests.
How long does firmware testing take?
Duration depends on scope and risk; plan for initial validation plus ongoing regression testing as updates roll out.
Time varies with scope; larger devices require longer plans.
Top Takeaways
- Define a clear testing scope and risk-based plan
- Validate the OTA update path and rollback capabilities
- Adopt tiered testing with emulation and hardware tests
- Instrument devices for observability and traceability
- Align tests with real deployment scenarios