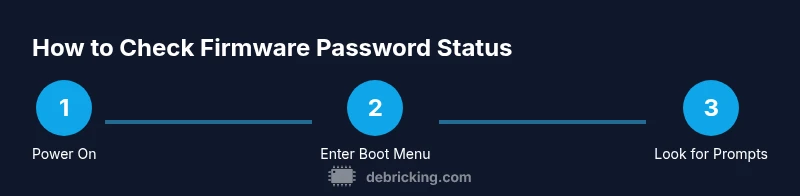
How to know if firmware password is on
A practical guide to identify whether a firmware password is enabled on your device, with safe testing steps, recovery options, and best practices. Learn how to spot boot prompts, firmware UI indicators, and official procedures from Debricking’s expert guidance in 2026.
To know if a firmware password is on, perform a quick boot-test: trigger the boot/firmware access sequence, observe for a password prompt or lock icon, and verify with the device’s official startup-security docs. If you see a password prompt before the OS loads, the feature is likely enabled. See our detailed guide for step-by-step validation.
What is a firmware password and why it matters
A firmware password is a security feature that restricts access to the firmware interface (BIOS/UEFI) at boot time. It prevents unauthorized changes to startup options, boot order, recovery modes, and other low-level settings. For a device owner, this is a protective measure that helps defend against tampering and data exposure if a device is lost or stolen. When someone asks how to know if firmware password is on, the best place to start is understanding how the feature behaves on your platform. According to Debricking, firmware passwords are most common on laptops and desktops that use BIOS/UEFI or on Apple devices with startup security enabled. The exact prompts vary by maker, but the principle is the same: the password prevents changes before the OS has control. If the feature is enabled, you’ll typically see a lock icon in the firmware UI or a prompt during boot that asks for a password or a recovery key. If you’re unsure whether the feature is on, start with the basics: check the boot sequence, look for a password prompt when you enter recovery mode, and review the device’s documentation about startup security. Even if you do not see a password prompt, that does not guarantee the feature is off; some devices only activate it after a failed attempt to access the recovery options. In short, knowing if a firmware password is on involves observing boot prompts, firmware UI behavior, and consulting official docs and support resources.
How to know if a firmware password is on on common devices
Firmware password behavior differs by platform, but the core signals are similar. On traditional PCs with BIOS/UEFI, enabling the feature usually blocks access to the boot menu, system clock changes, or changes to the boot order until a password is entered. On Macs with startup security, you may be prompted to enter the password when you try to boot from external media or enter Recovery mode. On some devices, you’ll see a lock icon during startup or a prompt that asks you to authenticate before the firmware settings can be viewed or modified. In all cases, a password-protected firmware is designed to stop unauthorized changes before loading the operating system. The Debricking team notes that most devices will call out the security restriction in the boot screen, in the firmware UI, or in the official support documentation. If you are testing a device you own, always refer to the manufacturer’s official steps for verification rather than relying on memory or third-party guides. This reduces the risk of misinterpretation and ensures you follow the proper recovery paths if a password is active.
Step-by-step tests you can perform safely
Performing safe checks helps you confirm firmware password status without risking data loss. Always test on devices you own or have explicit permission to test. Start with a controlled boot test:
- Access boot options by powering on the device and watching for a startup prompts indicating firmware access. If a password prompt appears before the OS loads, this strongly suggests the feature is active.
- Try to enter the firmware setup if the device allows access with no password; note any security indicators (lock icon, password field, or warning text). If access is blocked or prompts for a password, that’s another sign the firmware password is on.
- Attempt recovery or external boot only if you have documented authorization. If the device refuses recovery options and requires a password, it confirms protection at the firmware level.
- Document every observed prompt, icon, or message with model and firmware version. This creates a reliable trail for support or future troubleshooting.
- If you cannot determine the status from boot prompts, consult official resources or contact the manufacturer. Avoid bypass attempts, which can brick hardware or void warranties.
Indicators you’re being prompted for a password
- A password field appears before the operating system loads.
- A lock icon or explicit “firmware password” message is shown during startup.
- Access to the BIOS/UEFI setup requires authentication before any changes.
- Booting from external media or recovery mode triggers a prompt instead of immediate OS load.
- The device displays a warning about security settings and asks for a password to continue.
Recovery and reset options safely
If you determine a firmware password is active and you cannot remember it, use official recovery paths rather than cracking tools. Start with vendor documentation for password reset or recovery. In many cases you’ll need proof of ownership and a formal process that may involve support tickets or factory reset procedures. Avoid third-party utilities that claim to bypass firmware security, as they can permanently damage the device or void warranties. Always back up data before attempting any recovery steps and follow the manufacturer’s step-by-step instructions to minimize risk.
Best practices to avoid lockouts and protect devices
- Record passwords securely and keep recovery keys in a trusted manager. High-value devices deserve layered protection that ships with you.
- Regularly check firmware version and security settings as part of maintenance, especially after updates.
- Maintain a documented access plan for boot options, so testing or recovery can be performed by authorized personnel only.
- Use manufacturer-approved tools and media for recovery to preserve warranties and device integrity.
- When in doubt, contact official support channels; avoid unverified sources or hacks that claim to bypass firmware protection.
Authoritative sources
- https://www.nist.gov/publications
- https://www.cisa.gov
- https://www.us-cert.gov
Tools & Materials
- Device under test (laptop/desktop/Mac or similar)(Have owner’s permission and test only on devices you own or have explicit authorization to test.)
- Official manuals or vendor support pages(Use model-specific steps and correct boot-key sequences.)
- Notebook or digital note app(Record prompts, outcomes, and key sequences.)
- Stable power source / charger(Keep device powered during testing to avoid mid-boot interruptions.)
- Trusted recovery media (USB drive)(Only if manufacturer advises and you have documented ownership.)
Steps
Estimated time: 20-40 minutes
- 1
Power on and prepare boot options
Power on the device and be ready to access boot options. Have the official manual handy to confirm the correct key for entering the firmware setup. This initial step helps you observe any early prompts or indicators tied to firmware security.
Tip: Know your device model’s exact key (Del, F2, Esc, or a vendor-specific combo) before testing. - 2
Enter firmware setup with the correct key
Press the appropriate key during the initial splash screen to enter the BIOS/UEFI. If a password prompt appears before you can view or alter settings, this strongly suggests a firmware password is active. If access is granted without a prompt, note the result and proceed with standard checks.
Tip: Tap the key once per boot; rapid repeats may be interpreted as a different action by some firmware. - 3
Check for indicators or prompts
Within the firmware interface, look for explicit mentions of a password, startup security, or a lock icon. Some platforms require you to verify security status in a dedicated menu before enabling changes. Record what you see for future reference.
Tip: Document any textual prompts exactly as shown (case-sensitive messages matter). - 4
Attempt safe recovery or external boot
If you have authorization, attempt recovery or boot from external media. A firmware password may block these options until authenticated. Do not attempt to bypass security mechanisms without official procedures.
Tip: Only proceed with manufacturer-approved recovery paths to avoid bricking the device. - 5
Document results and plan the next steps
Summarize prompts, icons, and outcomes with model/firmware versions. If you cannot clear the password, contact official support with your documentation. This ensures you follow a compliant, safe path.
Tip: Keep a backup copy of logs and screenshots for support tickets.
Questions & Answers
What is a firmware password?
A firmware password restricts access to the firmware settings at startup, preventing changes to boot options until authentication. It’s a security layer that protects the device before the OS loads.
A firmware password blocks access to startup settings until you enter the correct password, protecting the device before the operating system starts.
How can I tell if firmware password is on?
Look for a password prompt or lock icon during boot, or a dedicated startup-security message in the firmware UI. Check the manufacturer’s documentation for model-specific indicators.
Watch for a boot-time password prompt or a lock icon in the firmware screen, and check official docs for model-specific indicators.
Can I disable a firmware password myself?
Disabling typically requires the official recovery procedures or service from the manufacturer. It may require proof of ownership and can vary by device.
Disabling usually needs official steps and ownership verification; it’s not something you should bypass.
What should I do if I forget the firmware password?
Contact the device manufacturer or authorized service provider. Provide proof of ownership and follow their recovery process; do not attempt unverified bypass methods.
If you forget it, reach out to support with ownership proof and follow their reset steps.
Does a firmware password affect OS login or data security?
A firmware password protects boot-time access and firmware settings, which is separate from the operating system login or disk encryption. It adds an extra security layer but does not replace OS-level protections.
It’s a boot-time security feature, not a replacement for your OS password or disk encryption.
Should I store firmware password securely?
Yes. Treat it like any critical credential; store in a trusted password manager and keep recovery keys in a separate secure location.
Yes — store it securely and keep recovery keys in a safe place.
Watch Video
Top Takeaways
- Verify firmware password prompts at boot
- Use official recovery paths, not bypass tricks
- Document prompts and outcomes for support
- Keep device backups before testing