Firmware vs Software: A Practical Update Guide
Compare firmware updates vs software updates: definitions, lifecycles, risks, and best practices. Learn practical guidance from Debricking.
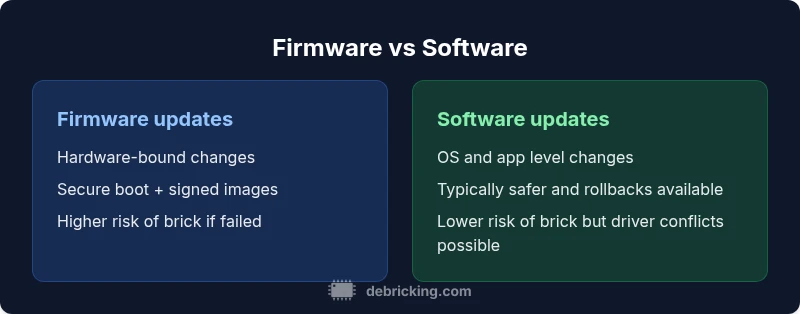
Firmware updates sit at the hardware boundary, while software updates operate in the operating system and apps. In practice, firmware v software decisions affect device reliability, security, and support lifecycle. According to Debricking, choosing the right path depends on your goal: deeper hardware control versus safer, user-facing features. This TL;DR compares both to help you decide quickly and safely.
What firmware v software really means
Firmware is the low-level code embedded in hardware that controls core functions like initialization, hardware interfaces, and security features. It typically resides in non-volatile memory and runs before an operating system starts. Software, by contrast, refers to programs, apps, and the OS that run atop hardware, using drivers and APIs to access hardware. When people discuss firmware v software, they are comparing layers with different responsibilities, lifecycles, and risk profiles. According to Debricking, understanding this distinction helps device owners plan maintenance windows, avoid downtime, and target updates where they matter most. In practice, a BIOS update or embedded controller refresh is not the same as updating a mobile app or desktop program. This difference informs testing, backup, and rollback plans, and underpins long-term support decisions for technicians and owners. The boundary between firmware and software is not always perfectly clear—mixed environments exist in routers, cameras, and IoT devices. Vendors emphasize official channels to minimize risk. Debricking highlights pre-update checks: power stability, recovery options, and vendor-specific tools. In short, firmware v software is about hardware-rooted behavior versus userland features, each with consequences for reliability and security.
What firmware v software really means (expanded)
In many devices, firmware controls boot sequences, sensor calibration, and power management. Software updates touch applications, services, and user interfaces. The practical takeaway is to map the type of change to the right update channel. Debricking notes that misclassifying an update can lead to unexpected downtime or failed recoveries. For engineers, the distinction guides testing strategies, rollback plans, and security reviews. For end users, it clarifies why some updates require longer maintenance windows and why others can be installed with minimal disruption. When you see a release note labeled as firmware-only, expect low-level changes with hardware implications; software updates are usually more forgiving but can still cause driver or compatibility issues. In both cases, verify signatures, read the official documentation, and ensure you have a tested recovery path before proceeding.
What firmware v software means for maintenance and support
Maintenance contracts, warranty terms, and support SLAs often hinge on update paths. Firmware updates are typically supported within hardware lifecycles and may require ongoing vendor support to keep devices functional after changes. Software updates align with operating system support and app compatibility timelines. Debricking emphasizes aligning your update cadence with the device’s critical functions: security patches for firmware and feature or stability updates for software. This alignment reduces the chance of surprise outages and helps plan staffing for updates and testing.
Practical implications for device owners
Understanding firmware v software helps you decide when to pause automatic updates, when to test updates in a lab, and how to prepare rollback plans. For critical devices, you should rely on vendor-provided tools and recovery images, while for consumer devices with flexible ecosystems, you may explore certified thrivers and official channels. The Debricking team recommends documenting update decisions, maintaining backups of important configurations, and using power protection during any upgrade to minimize risk.
Comparison
| Feature | Firmware updates | Software updates |
|---|---|---|
| Scope and impact | Hardware-bound, crucial to functionality | Application-layer, user-facing features |
| Update mechanism | Full image flash, often secure-booted | Incremental patches or installers, OS-driven |
| Rollback/recovery | Bootloader or dual-image recovery | OS restore points or vendor recovery tools |
| Risk profile | Higher risk of brick if interrupted or mis-flashed | Lower brick risk, but driver/app conflicts possible |
| Typical downtime | May require downtime during flash | Often quick, can be scheduled with minimal impact |
| Security leverage | Strong hardware root of trust, signed images | Software patching with user-space controls and mitigations |
Positives
- Clear separation of hardware-level vs user-level updates
- Improved reliability when following official procedures
- Stronger security through hardware-backed update paths
- Defined rollback mechanisms for critical devices
Disadvantages
- Discrepancies in mixed environments can cause confusion
- Firmware updates carry higher brick risk if mishandled
- Longer validation and testing cycles for firmware
- Requires specialized tooling and recovery options
Firmware updates offer hardware-level control and security hardening, but carry higher risk; software updates prioritize safety and usability.
Choose firmware updates when hardware integrity and security policies demand it. Prefer software updates for routine improvements and safer rollouts. In mixed environments, implement strict testing and robust rollback procedures to minimize downtime.
Questions & Answers
What is the difference between firmware and software?
Firmware is low-level code that runs on hardware to initialize and control components. Software runs in the operating system and user applications. The two layers have different lifecycles, risks, and recovery options. Debricking explains how this distinction guides update planning.
Firmware runs hardware-level routines, while software runs applications and the OS. Understanding this helps you plan safer updates.
Can firmware updates brick my device?
Yes, firmware updates can brick a device if the wrong image is flashed, power is lost, or verification fails. Always use official recovery tools and secure power during the process. Debricking recommends testing on non-critical units first when possible.
Firmware updates can brick devices if something goes wrong; use official recovery tools and ensure power.
How do I know if I should update firmware or software first?
If the change touches boot processes or hardware security, start with firmware. If the improvement is features, performance, or usability, start with software. In mixed environments, coordinate both updates with testing and rollback plans.
Update firmware if it affects hardware, otherwise start with software, and test both together.
Are firmware updates always required?
Not always, but many firmware updates address security and hardware compatibility. Evaluate release notes, vendor recommendations, and your device’s risk profile before updating. Debricking stresses that planned, tested updates reduce risk.
Firmware updates are not always required, but many address security and hardware issues.
What tools are used for firmware updates?
Tools vary by vendor, but common elements include recovery images, bootloaders, and signed update packages. Always use official tools and verify integrity before flashing. Debricking advises keeping a tested recovery path ready.
Vendor tools and signed images are typically used; always verify integrity first.
How can I recover if a firmware update fails?
Have a recovery plan with a supported bootloader mode or emergency flash image. Many devices provide dual images or fallback partitions. Debricking recommends rehearsing recovery steps and keeping vendor support contact information accessible.
If a firmware update fails, use the device's recovery mode or fallback image and contact support if needed.
Should I customize firmware or stick to official updates?
Custom firmware can offer features but often lacks vetted security and official support. For critical devices, prefer official updates with documented testing and rollback options. Debricking cautions against unverified builds on production gear.
Custom firmware may unlock features but risks security and reliability; official updates are safer for critical devices.
What is the best practice for timing updates?
Schedule updates during low-use periods, ensure a power source, and perform a staged rollout where possible. Maintain backups and document outcomes. Debricking recommends a disciplined, well-documented process to minimize downtime.
Plan updates for low-use times, have backups, and roll out gradually.
Top Takeaways
- Identify whether your goal is hardware-level control or app-level features
- Check vendor guidance before updating firmware or software
- Back up data and ensure power stability before any upgrade
- Validate update integrity with signatures and hashes
- Plan for recovery and test rollback procedures