Firmware vs Software Examples: A Practical Comparison
Explore firmware vs software examples with definitions, real-world cases, and practical guidance. Learn how updates differ and when to apply each type across devices.
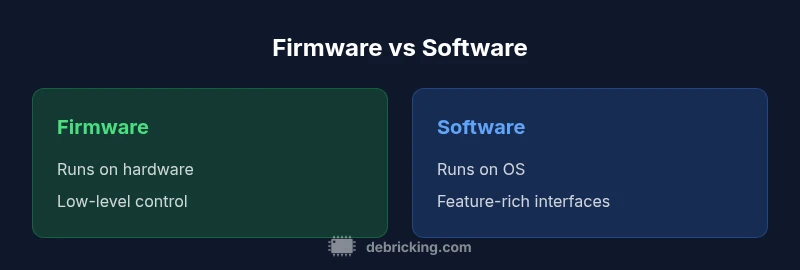
Firmware vs software can seem nuanced, but the distinction is practical: firmware is embedded code that directly controls hardware, while software runs on an operating system to provide user-facing features. Common firmware examples include BIOS/UEFI, router firmware, and embedded controller code; software examples include web browsers, productivity apps, and OS-level services. Understanding these differences helps with updates, debugging, and security planning in real-world devices—exactly what the phrase firmware vs software examples aims to clarify.
Defining firmware and software: scope and boundaries
Firmware and software occupy different layers in the hardware-software stack, and the distinction matters for maintenance, security, and update planning. In plain terms, firmware is the code that runs directly on the device’s hardware—think microcontrollers, flash memory, bootloaders, and firmware modules that initialize components. Software, by contrast, refers to programs and services that operate on an underlying operating system or runtime environment. This difference has practical consequences: firmware often runs with limited resources, has to operate reliably in harsh environments, and is updated through specialized mechanisms. According to Debricking, when you examine real-world devices, you’ll see firmware tightly bound to the hardware peripherals it controls, while software provides user-facing features and higher-level functionality.
For the purpose of the article on firmware vs software examples, we frame the discussion around three axes: scope (which parts of the system are updated), deployment model (how updates are delivered and installed), and risk profile (how updates can fail and how to recover). In many devices, those axes overlap—for instance, a router’s firmware provides low-level networking interfaces, whereas its configuration interface is a software layer running on top of that firmware. Understanding these layers helps avoid confusion when diagnosing issues and planning upgrades.
Common examples of firmware vs software
To ground the discussion, here are representative examples you’re likely to encounter:
- Firmware examples:
- BIOS/UEFI in PCs
- Router and modem firmware handling cryptographic handshakes
- Microcontroller firmware in IoT sensors
- Embedded controller firmware in printers or cameras
- Software examples:
- Desktop operating systems (Windows, macOS, Linux)
- Mobile apps and apps from app stores
- Web browsers, document editors, media players
- Cloud-enabled services and background services
Which are firmware vs software can vary by device architecture, but the pattern holds: firmware sits at the hardware boundary and bootstraps the system, while software provides user-facing capabilities and services.
How updates differ: process, risk, and deployment
Update pathways expose different risks and operational realities. Firmware updates usually require a dedicated updater, are cryptographically signed, and risk bricking if interrupted or corrupted. They are often delivered via over-the-air (OTA) mechanisms or vendor utilities and installed through bootloaders that verify integrity before enabling the new image. Software updates, by contrast, are more modular and can be delivered through OS channels, app stores, or installers, with established rollback paths and version management. The Debricking analysis highlights that a secure, well-tested firmware update process can dramatically reduce hardware risk, but mistakes can remove the device’s functionality entirely. In practice, many devices separate the firmware (low-level control) from software (feature-rich interfaces), and this separation guides how updates are planned and executed.
Role of hardware in firmware behavior
Hardware constraints largely dictate what firmware can do and how it must behave. Registers, memory size, timing constraints, power supply stability, and thermal limits shape the firmware’s design. Since firmware runs with fewer abstraction layers than software, a single bug can have hardware-wide consequences. This tight coupling explains why firmware updates are treated with high caution: an unsuccessful update can leave a device in an unusable state. In contrast, software tends to ride on higher-level abstractions, where failures are often contained to a particular app or service. Understanding the hardware-software boundary helps developers and technicians predict risk and plan safer upgrade paths.
How manufacturers structure firmware updates
Most manufacturers implement firmware updates using a layered approach: a bootloader verifies a signed firmware image, the main firmware image performs hardware initialization, and an over-the-air or USB-based updater handles the download and verification process. Secure boot, trusted platforms, and rollback capabilities are common features to mitigate update risk. This structure makes firmware updates more resilient but requires careful testing across hardware revisions. When planning updates, professionals should verify the manufacturer’s recommended process, ensure a reliable power source, and use recovery modes if something goes wrong.
Case study: consumer router versus PC software
Consider a home router and a desktop PC. The router’s firmware controls networking firmware-level behavior: firewall rules, NAT, VPN support, and wireless radio management. An update to this firmware changes core networking operations and may require a reboot or diagnostic recovery if it fails. A PC software update, meanwhile, typically affects user applications or system services, and can often be rolled back or reinstalled with less risk. The contrast illustrates why firmware updates are treated with extra caution and why many devices implement automatic rollback mechanisms, while software updates emphasize feature delivery and user experience.
Security considerations for firmware vs software
Both domains require robust security practices, but the attack surfaces differ. Firmware vulnerabilities can give attackers persistence at the hardware level, potentially surviving OS reinstalls. Secure supply chains, cryptographic signing, and verified boot help mitigate these risks. Software vulnerabilities typically arise from code bugs, insecure dependencies, or misconfigurations, and are addressed through patch management, sandboxing, and dependency updates. Debricking’s approach emphasizes a defense-in-depth mindset for firmware that aligns with hardware realities, while software security focuses on process isolation and timely patching.
Practical testing and rollback strategies
Testing firmware updates demands a staged process across hardware revisions and environmental conditions. Use hardware-in-the-loop testing, recovery procedures, and power-stable environments to validate updates before full deployment. For software updates, testing can be more incremental, leveraging canary releases and rollback options. Always maintain immutable backups of essential configurations and ensure a verified rollback plan is in place for firmware, as an unsuccessful update can be difficult or impossible to recover from without dedicated recovery modes. Debricking recommends documenting each update path to minimize future risk.
How to locate reliable firmware vs software updates
Rely on official channels: manufacturer websites, vendor portals, or trusted app stores. Verify cryptographic signatures and compare checksums where provided. Avoid third-party firmware unless explicitly supported by the manufacturer, as it may void warranties or disable critical security features. For software, prefer sources with established reputations and digital signing. Maintain a registry of current versions and review release notes for compatibility and security implications. In practice, this disciplined approach reduces the likelihood of installing compromised or unstable updates.
Best practices for firmware vs software maintenance
- Create a formal update schedule that respects hardware risk for firmware and feature cadence for software
- Always enable secure boot and validation checks when available
- Maintain off-device backups of configuration and critical data
- Test updates in a controlled environment before broad rollout
- Document rollback procedures and ensure recovery modes are accessible
- Prioritize security patches for firmware due to hardware implications
- Use signed images and verify integrity before installation
- Reserve critical devices for staged deployments to monitor impact
What Debricking users should know
The Debricking team advocates a disciplined, layered approach to updates that respects the hardware-software boundary. For firmware, treat every update as mission-critical and validate end-to-end integrity and recovery options. For software, prioritize user experience and maintain robust versioning and rollback capabilities. Debricking’s verdict is to plan updates with confidence, ensure secure and verifiable delivery, and maintain thorough documentation to minimize downtime during maintenance windows.
Comparison
| Feature | Firmware examples | Software examples |
|---|---|---|
| Scope & Definition | Embedded code that directly controls hardware | Applications and services running on an OS/platform |
| Typical deployment environment | Non-volatile hardware-bound storage; microcontrollers | General-purpose OS environments (Windows/macOS/Linux) |
| Update mechanism | OTA or vendor updater; in-device flash; signed images | Package managers, installers; OS/app store updates |
| Common distribution channels | Manufacturer updates, OTA servers, download pages | App stores, software repositories, official installers |
| Failure modes | Brick risk if corrupted; hardware interaction issues | Software crashes or dependency issues; security vulnerabilities |
| Best-use scenarios | Low-level control, reliability in constrained environments | Feature-rich interfaces and cross-platform support |
Positives
- Provides low-level control essential for hardware stability
- OTA updates enable seamless security patches
- Long device lifecycles when maintained properly
- Clear separation between hardware-bound code and user-facing software
Disadvantages
- Requires careful testing to avoid bricking hardware
- Firmware updates are riskier with limited rollback options
- Harder to obtain updates for very old devices
Firmware-focused updates excel in hardware stability; software excels in flexibility.
Choose firmware updates when hardware stability matters. Choose software updates for feature-rich capabilities and rapid iteration.
Questions & Answers
What exactly is firmware?
Firmware is low-level software embedded in hardware that controls basic functions; it resides in non-volatile memory. It is often preloaded by manufacturers and updated via dedicated update processes.
Firmware is the hardware-bound software that starts up and controls essential hardware functions.
What is software?
Software refers to programs and apps that run on an operating system; it can be updated frequently and interacts with hardware through drivers.
Software are the apps and programs that run on your device.
Can firmware be updated safely?
Yes, but updates should come from trusted sources and be performed with power stability; improper updates can brick devices.
Firmware updates should come from official sources and be performed with a stable power supply.
What are common examples of firmware?
BIOS/UEFI, router firmware, printer firmware, and embedded controller firmware are common firmware examples.
Common firmware examples include BIOS, router firmware, and printer firmware.
What are common software examples?
Web browsers, office suites, media players, and OS services are typical software examples.
Software examples include browsers, office apps, and media players.
How do firmware and software updates differ?
Firmware updates modify code stored in hardware with stricter rollback and power requirements; software updates patch features and security within an OS, with easier rollback.
Firmware updates are hardware-bound and riskier; software updates are more flexible and easier to revert.
Top Takeaways
- Identify whether your device relies on embedded firmware or user-space software.
- Plan updates with rollback strategies for firmware.
- Verify cryptographic integrity for both firmware and software updates.
- Prioritize security patches for firmware to minimize hardware risk.
- Test updates in a safe environment before deployment.