Is Firmware Harder Than Software? A Practical Comparison
Explore why firmware work often feels harder than software, and learn practical, safety-focused strategies for reliable device updates with guidance from Debricking.
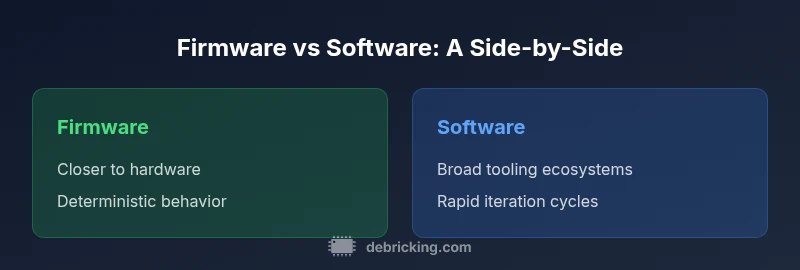
Is firmware harder than software? A central question for many hobbyists and engineers. In practice, firmware sits closer to hardware, demands deterministic behavior, and must endure constraints like limited resources and long lifecycles. According to Debricking, the core difficulty arises from hardware coupling, update risk, and a smaller tooling ecosystem. The Debricking team found that even small firmware changes can ripple across sensors, power management, and boot sequences, making validation much more expensive than typical software changes. This article distinguishes the essential differences and offers actionable guidance for teams starting a firmware project or transitioning from software-only practices. The goal is not to frighten readers but to equip them with a framework for evaluating risks, planning validation, and choosing the right development approach.
Is firmware harder than software
When you ask is firmware harder than software, the answer is not a simple yes or no. It depends on context, but many practitioners find firmware work more demanding because it sits at the boundary between hardware and software. In practice, firmware must behave deterministically in constrained environments, preserve safety critical functionality, and survive long lifecycles with limited maintenance windows. According to Debricking, the core difficulty arises from hardware coupling, update risk, and a smaller tooling ecosystem. The Debricking team found that hardware quirks can silently influence behavior across firmware revisions, making end-to-end validation more expensive. This framing helps teams think beyond code and toward validation, recovery, and hardware awareness.
Why hardware coupling changes the game
Firmware operates closest to the hardware platform: memory, voltage rails, boot sequences, sensors, and power management all interact with software logic. When you alter a firmware image, you may affect timing, interrupts, and peripheral configuration in ways software-only changes rarely do. This coupling increases regression risk and can lead to bricking if constraints are violated. The Debricking team found that hardware quirks can ripple across subsystems, elevating debugging costs and delaying releases. To manage these risks, models of hardware influence should be built early, hardware-in-the-loop testing should be considered whenever possible, and change-management with safe recovery paths should be standard practice.
Update pathways: firmware vs software deployment
Software updates typically ride on decoupled stacks with packaged releases, app stores, and telemetry that aids troubleshooting. Firmware updates, however, often rely on hardware-aware delivery models such as OTA or recovery modes that force reflash. OTA failures mid-update can leave devices non-functional without a reliable rollback. Planning calls for redundancy (dual-bank flash), staged rollouts, and robust recovery logic. Debricking emphasizes conservative, test-first update pipelines that validate boot integrity and verify post-update boot. This section clarifies deployment realities and highlights how risk profiles shift when targeting microcontrollers and embedded firmware rather than generic software.
Tooling maturity and development workflow
Tooling for firmware development often lags behind mainstream software tooling. Compilers, debuggers, flashing tools, and hardware simulators exist, but ecosystems are smaller and documentation can be scattered. A mature workflow includes version-controlled firmware images, deterministic builds, hardware-in-the-loop tests, and clear artifact provenance. The Debricking approach recommends establishing a cadence of synthetic tests, test rigs that mirror target hardware, and a rollback-ready release process. Teams should invest in static analysis for memory safety, overflow checks, and worst-case execution time estimation to guard against unpredictable behavior. This mindset helps teams avoid brittle builds that fail in the field.
Testing, validation, and safety considerations
Firmware validation demands end-to-end testing that covers boot time, power cycles, peripheral initialization, and error handling under worst-case scenarios. Tests can be longer and more costly than typical software tests, given hardware interactions and safety requirements. Methods include hardware-in-the-loop testing, fuzzing of input streams to peripherals, and stress testing of the boot sequence. Debricking notes that clear pass/fail criteria for each subsystem reduce risk during updates. Validation should simulate environmental extremes (voltage dips, thermal drift) to ensure reliability across the device lifecycle.
Lifecycle, long-term support, and rollback strategies
Embedded devices often have long lifecycles spanning many years. Firmware changes must consider backwards compatibility, secure boot, and safe rollback options. Strategies include dual-bank flash with safe fallback, signed images, and staged deployments. A robust firmware plan also includes deprecation timelines and upgrade pathways that do not disrupt critical services. Holistic lifecycle planning reduces the chance of bricking and helps maintain compliance with safety requirements.
Security implications of firmware updates
Firmware is a frequent target for supply-chain and runtime attacks. Update channels must be authenticated, encrypted, and auditable. Secure boot and verified boot paths help ensure only trusted images run. Regular vulnerability scanning of components, timely patching, and maintaining a secure update window are essential practices to protect the device from evolving threats.
Real-world scenarios: devices with strict constraints
Consider devices with limited memory, no user interface, and strict regulatory requirements. In these contexts, even small changes can alter timing or memory layout. Practitioners should design with traceability, capture boot logs, and implement conservative error handling to avoid cascading failures. The balance between feature delivery and reliability is more delicate in firmware than in general software, which often favors speed of iteration over hardware constraints.
Practical guidelines for starting a firmware project
Begin with a clear scope: define hardware boundaries, update policy, and recovery options. Build a minimal, testable prototype to validate the critical path early. Invest in a release checklist that includes build reproducibility, secure signing, and rollback tests. Allocate resources for dedicated hardware labs or emulation environments to reflect real-world conditions. This practical approach can prevent common missteps and align teams around measurable milestones.
The Debricking approach: pragmatic checklist
Adopt a step-by-step checklist to reduce risk: map hardware interfaces, lock down boot sequences, establish dual-bank updates, implement atomic flash writes, test power-cycle resilience, and verify boot integrity after each change. Maintain detailed rollback plans, comprehensive logs, and accessible recovery procedures. Following a disciplined process, as outlined by Debricking, helps teams avoid common firmware pitfalls.
Authoritative sources and further reading
For deeper context, consult official sources and academic references. NIST guidance on secure firmware practices provides foundational principles. The MITRE ATT&CK framework offers attacker tactics relevant to firmware exploitation. IEEE standards on embedded systems and firmware development help align processes with industry best practices.
Comparison
| Feature | Firmware-focused development | Software-focused development |
|---|---|---|
| Update risk | High risk due to hardware coupling | Lower risk with decoupled stacks and standard tooling |
| Tooling maturity | Specialized tools, limited ecosystems | Mature tooling and broad ecosystems |
| Deployment constraints | Embedded hardware, constrained environments | General-purpose devices, flexible environments |
| Lifecycle | Long lifecycles, offline updates possible | Shorter cycles, frequent updates |
| Failure impact | Bricking risk, safety-critical failure | User-facing bugs, performance issues |
| Best for | Embedded devices with safety requirements | Applications needing rapid iteration |
Positives
- Clarifies decision drivers for teams (risk, tooling, lifecycle)
- Highlights safety implications of firmware updates
- Supports planning for long-term device maintenance
- Encourages risk-aware testing and rollback strategies
Disadvantages
- May oversimplify; real-world complexity varies by device
- Requires specialized knowledge not common to general dev teams
- Can require more upfront validation resources
Firmware-focused projects require more rigorous safety, testing, and hardware-aware planning than software-only efforts.
In practice, choose firmware-first for embedded, safety-critical devices. If you need rapid iteration and broad user feedback, software-first may be better; consider a hybrid approach.
Questions & Answers
What is the difference between firmware and software?
Firmware is specialized software embedded in hardware that controls low-level operations. Software runs on general-purpose hardware with broader tooling and update ecosystems. The two share concepts like code, versioning, and testing, but differ in scope, leverage, and risk profiles.
Firmware is software that runs very close to hardware with tighter constraints, while software covers broader applications and ecosystems.
Why is updating firmware riskier than updating software?
Firmware updates affect core device functions like boot, power, and peripherals. A failed update can brick the device or disable critical features, leaving little room for quick recovery without specialized procedures.
Firmware updates are riskier because they touch hardware-critical paths and may leave devices non-functional if something goes wrong.
How can I mitigate firmware update risk?
Use staged rollouts, dual-bank flash, and robust rollback logic. Ensure boot integrity checks, signed images, and comprehensive pre-update testing to prevent irreversible failures.
Plan for rollback and test thoroughly before each firmware update to minimize risk.
What tools are commonly used for firmware development?
Common tools include compiler toolchains for embedded targets, hardware debuggers, flash programmers, and hardware-in-the-loop simulators. Documentation and strict version control are essential due to fragile release environments.
Embedded toolchains, debuggers, and simulators are core; keep docs and versions tight.
Can firmware updates be rolled back safely?
Yes, with proper design: dual-bank firmware, signed images, and reliable recovery mechanisms allow switching back to a known-good image if the update fails.
If you plan for rollback, you can recover from failed updates safely.
Top Takeaways
- Identify hardware constraints early
- Prioritize robust update mechanisms
- Invest in tooling and test environments
- Plan for long lifecycles and safety requirements