Software vs Firmware: Key Differences and Practical Guidance
Explore the essential distinctions between software and firmware, how updates differ, and practical guidance to balance reliability, security, and feature needs for devices.
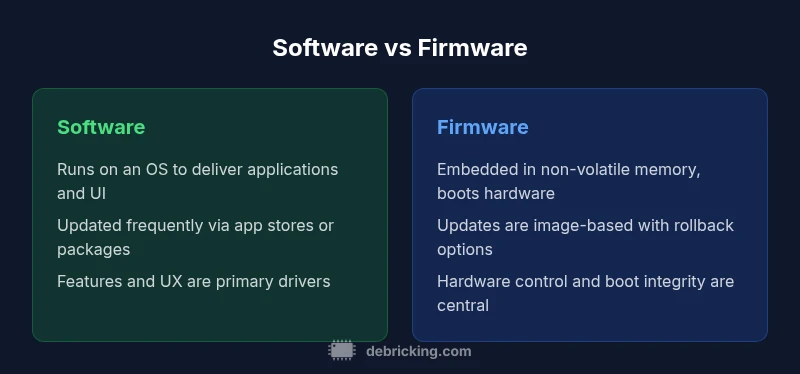
Software and firmware occupy different layers of a device. Firmware is embedded in non-volatile memory and handles core hardware control, while software runs atop an operating system to provide features. Updates, risks, and user impact differ: firmware prioritizes stability and security; software prioritizes features and customization. This comparison explains the key differences and practical implications.
What software versus firmware means for devices
The distinction between software and firmware is fundamental for understanding how devices behave, update, and recover from failures. In practice, many people conflate the two, but the implications are real: firmware sits closer to the hardware, often executing at boot and managing essential peripherals; software runs on top of an operating system or runtime environment and provides user-facing features. According to Debricking, recognizing this separation helps you plan maintenance windows, safety nets, and update strategies that minimize downtime and risk. When you think about a device’s life cycle, you will regularly weigh feature enrichment against hardware compatibility, secure boot requirements, and resilience against power loss. This article uses a practical lens to compare how and why these layers differ, with concrete guidance for owners and engineers.
Core differences in architecture
Software and firmware occupy different layers of the system stack. Firmware is usually stored in non-volatile memory on the device and runs during power-on self-test and boot, establishing low-level hardware control. Software resides in a separate memory area (often on a processor with an OS) and provides applications, UI, and services. The implications are broad: firmware updates can rewrite how the device boots, while software updates alter features without touching boot code. Structure, dependency, and modularity differ: firmware typically has strict certification and limited write cycles, whereas software thrives on modularity and rapid iteration. Understanding these architectural distinctions helps developers and buyers assess upgrade paths, compatibility, and maintenance costs over the device’s life.
Update lifecycle and deployment practices
Firmware update cycles tend to be infrequent and conservative, focusing on security patches, bootloader improvements, or device-level stability. Software update cycles are frequent and can be delivered through app stores, package managers, or over-the-air mechanisms that push updates to features, performance, or UI. The lifecycle is shaped by risk appetite: firmware updates require longer validation, rollback, and recovery plans; software updates emphasize feature rollouts and user experience. Debricking's approach emphasizes staged releases and robust rollback procedures. Practically, this means you should plan separate test tracks: firmware carriers (stable, confidential) and software channels (beta, stable). For devices with safety-critical operations, governance around the update window, power availability, and fallback modes is essential.
How updates are delivered (packets, firmware images, OTA)
Updates are delivered as binary images, signed and verified before installation. Firmware updates often require a bootloader that can switch to a recovery partition if something goes wrong during the update. Software updates are typically distributed as packages or apps, with integrity checks and rollback points. Secure delivery mechanisms, such as cryptographic signatures and code signing, help prevent tampering. Over-the-air delivery is common for both layers, but OTA for firmware often includes a dual-partition scheme to enable safe rollbacks. In practice, you should verify the update source, ensure the device has adequate power, and enable a recovery mode in case of interruption. Debricking emphasizes that a well-designed update flow reduces the risk of bricking hardware during upgrades.
Security implications and attack surfaces
Firmware and software each present distinct security surface areas. Firmware often controls boot processes, low-level hardware access, and secure elements, making it a high-value target for attackers if left unprotected. Software frequently handles user data, networks, and application logic, inviting different types of exploits. A strong security posture requires secure boot, authenticated updates, and hardware-backed key storage for firmware, plus application sandboxing, least privilege, and regular patch cycles for software. The supply chain risk is real in both layers; ensuring trusted vendors, transparent update policies, and verifiable signatures helps reduce risk. Debricking notes that security-conscious teams tend to implement separate testing rails for firmware and software to detect vulnerabilities earlier in the lifecycle.
Performance and resource considerations
Firmware tends to be lean by design; it runs with constrained memory and dedicated CPU cycles, focusing on reliability and deterministic behavior. Software is typically more flexible, but it requires more RAM, CPU, and storage to support features, a rich UI, and background services. The performance envelope differs: firmware must start within tight time budgets and operate under power constraints; software must respond quickly to user input and external stimuli. There is often a trade-off between feature richness and boot time. Reading device logs during updates can reveal whether a change in firmware or software affected latency or responsiveness. For developers, this means we plan separate performance budgets for each layer and validate them with real-world workloads.
Typical use cases by domain (consumer devices, enterprise, IoT)
Consumer devices underlie a broad spectrum of firmware-first worlds, where boot reliability and energy efficiency matter. In enterprise and data centers, firmware updates can improve server health and hardware compatibility, but software upgrades drive productivity and new capabilities. In IoT, firmware-level security and remote management are critical, while software-level applications enable flexible control and data analytics. A practical approach is to define clear roles for each layer within the product architecture: firmware handles device governance and safety, software handles user-facing features and services. Understanding these domain-specific needs helps product teams prioritize which updates to push and when.
Reliability, redundancy, and fail-safes
Reliability in the firmware layer often derives from hardware-level protections, such as watchdog timers, dual boot partitions, and atomic update sequences. Software relies on error handling, application-level retries, and rollback to known-good states. A robust plan combines both: firmware ensures a safe boot and recovery path, while software provides resilient operation and graceful degradation. In practice, teams implement fallbacks that trigger if either layer detects trouble, preserving core functionality. Debricking emphasizes the importance of pre-defined recovery paths and validated rollback images as part of any firmware update strategy. For critical devices, you should simulate power loss during updates and verify restoration procedures regularly.
Development and testing workflows
Developing firmware and software requires distinct toolchains and testing pipelines. Firmware development focuses on hardware abstraction layers, boot sequences, and low-level drivers, often using hardware-in-the-loop simulations. Software development centers on APIs, UI flows, and integration tests within operating systems. Testing both layers together helps catch regressions and compatibility issues early. A mature workflow uses staged environments, feature flags, and rollback capabilities. Teams should define acceptance criteria for firmware stability (boot success rate, crash frequency) and software quality metrics (response times, memory leaks). The coordination between hardware and software teams is essential for a smooth update cycle.
Compatibility and interoperability challenges
Backward compatibility matters for firmware because older hardware revisions may require different boot paths or drivers. Software compatibility focuses on OS versions, libraries, and API stability. A failure to maintain compatibility can brick devices or degrade user experience. Manufacturers often maintain hardware-specific firmware variants and software packages, which increases testing complexity and support costs. In practice, you plan a compatibility matrix that documents supported hardware revisions, firmware versions, and software dependencies. Clear deprecation notices and long-term support plans help customers migrate without disruption.
Common myths and misconceptions
One common myth is that firmware updates are always riskier than software updates. In reality, both can cause problems if interrupted or misapplied. Another myth is that software is always more flexible than firmware; in some devices, firmware changes unlock essential capabilities that software alone cannot provide. A final misconception is that updating firmware is unnecessary for security; in truth, firmware patches often address boot security and hardware-level defenses. Debricking encourages readers to evaluate updates based on change impact, risk, and recovery options rather than assumptions.
How to evaluate a device's software and firmware quality
Evaluating quality starts with clear criteria for reliability, security, and maintainability. Look at update frequency, patch history, and documentation. Assess boot times, error rates, and recovery capabilities for firmware, and measure feature coverage, performance, and usability for software. Examine the build process, code quality indicators, and tests used to validate updates. A practical checklist includes secure boot status, code-signing verification, rollback safety, and user-recoverable pathways. Remember that a well-documented roadmap and transparent vendor practices are signs of mature software and firmware ecosystems.
Debricking guidance and practical checks
Practical checks before applying any update include ensuring a stable power source, verifying available battery or power adapter, and confirming that the device is connected to a trusted update server. For firmware, ensure there is a recovery image and a known-good backup in case the update fails. For software, back up data, test critical workflows, and use staging channels before broad rollout. Debricking emphasizes designing update processes that minimize downtime and include safe rollback options. If an update fails, follow documented recovery steps, avoid manual edits to boot images in production, and use official recovery tools when possible.
Making the choice: a practical framework
To decide between software-centric updates and firmware-focused improvements, start with the device’s risk profile and intended use. If reliability, boot integrity, and security at the hardware level are paramount, prioritize firmware improvements and robust recovery paths. If you need faster feature iteration, broader compatibility, and user-facing enhancements, prioritize software updates with strong testing and rollback mechanisms. Create a decision tree that weighs impact, cost, and upgrade risk, and align it with your organization’s governance and QA processes. The Debricking team recommends documenting criteria and following a staged release model that protects users while enabling progress.
Comparison
| Feature | Software | Firmware |
|---|---|---|
| Definition/Role | Runs on an OS to deliver applications and UI | Embedded code in non-volatile memory that boots the device and controls hardware |
| Update mechanism | Frequent, patch-driven updates via OS or app stores | Infrequent, image-based updates with rollback and recovery |
| Dependency on hardware | Relies on OS, drivers, and runtime | Tightly bound to hardware and bootloader |
| Security surface | Software patches, sandboxing, network security | Boot integrity, secure boot, hardware-backed keys |
| Typical use cases | Feature-rich apps, UX, interoperability | Critical boot control, device stability, safety |
| Rollback/Recovery | App-level rollback or reinstall | Dual partitions and recovery modes commonly used |
Positives
- Enables frequent feature updates and UI enhancements
- Offers stable hardware control and reliability
- OTA updates enable remote maintenance
- Clear separation between software and firmware reduces risk during updates
Disadvantages
- Firmware updates can be risky if interrupted
- Software updates may require more memory and processing power
- Firmware updates may have longer validation and rollback requirements
Firmware is generally best for reliability and hardware control; software is best for flexibility and user-facing features.
Firmware-focused updates improve boot stability and security in embedded contexts. Software updates drive features and adaptability. Use a layered update strategy aligned to device risk and user needs.
Questions & Answers
What is the fundamental difference between software and firmware?
Software runs on an operating system to provide applications and features, while firmware is embedded in hardware and manages boot and core device control. The two layers serve distinct purposes and require different update and security strategies.
Software runs on an OS to add features; firmware controls boot and hardware. They serve different roles and need separate update plans.
Can firmware be updated over the air (OTA)?
Yes, many devices support OTA firmware updates. They require careful power management, secure signing, and a rollback path in case the update fails.
Yes, OTA firmware updates are common but must be done with power and security safeguards.
Which should I prioritize for new features—the software or the firmware?
For new features, software updates usually provide faster, more extensive UI and functionality changes. Firmware updates tend to add capabilities related to hardware control or boot security and are less frequent.
If you want features, focus on software; for hardware-level improvements, firmware is key.
What are common risks with firmware updates?
Interruptions during firmware updates can brick devices or leave them in an unrecoverable state. Always use a recovery plan, verified images, and dual-partition schemes where possible.
Firmware updates can fail badly if interrupted; have a recovery plan.
How should I test updates safely?
Use staging channels, backups, and validated rollback paths. Test critical workflows first and ensure a known-good recovery option exists before wide rollout.
Test in stages and back up data; ensure rollback exists before going wide.
Top Takeaways
- Identify device needs: hardware control vs user-facing features
- Expect different update lifecycles and risk profiles
- Security approaches differ by layer: boot integrity vs app security
- Plan robust rollback and recovery for both firmware and software
- Coordinate cross-layer testing for reliable updates