How to Disable Firmware TPM: A Practical Step-by-Step Guide
Learn how to disable firmware tpm safely with a practical, vendor-agnostic approach. This guide covers BIOS/UEFI steps, risks, backups, and recovery options to help tech enthusiasts manage TPM settings.
If you're wondering how to disable firmware tpm, start by booting into BIOS/UEFI and locating the TPM option (often labeled TPM, fTPM, or PTT). Disable it, then save changes and reboot. Note that this can affect disk encryption and security features like BitLocker and Windows Hello; ensure you have admin access and a recovery plan before proceeding.
TPM Fundamentals and Why You Might Consider Disabling It
The TPM, or Trusted Platform Module, is a hardware security chip that stores cryptographic keys used by features such as disk encryption (e.g., BitLocker), secure boot, and Windows Hello credentials. For some users, especially those repurposing devices or integrating with non-standard networks, disabling TPM can be a deliberate choice. According to Debricking, understanding the TPM's purpose helps you weigh the security advantages against the practical need to control hardware features. When you disable TPM, you are reducing the hardware-backed protection that keeps keys safe from offline attacks, and you may see changes in how your system unlocks and protects data. Use this knowledge to assess risk and plan carefully before taking action.
Modern systems may use different TPM implementations (classic TPM, fTPM, or PTT). The goal of this guide is to equip you with vendor-agnostic steps and safety considerations, not a one-size-fits-all script. Debricking emphasizes that TPM is deeply integrated with OS features and encryption, so any change should be paired with backups and a recovery plan.
TPM Variants and What They Mean for Disabling
There are several ways a device can implement TPM functions. A discrete TPM chip is separate from the CPU, while fTPM (Firmware TPM) and PTT (Platform Trust Technology) are built into firmware and firmware-provided capabilities. The disabling process broadly involves turning off the TPM interface in BIOS/UEFI, but the exact labels and locations vary by vendor. Debricking notes that some systems may expose TPM under Security, Advanced, or Trusted Computing sections, and the option may be labeled simply TPM, TPM2, fTPM, or PTT. If you’re unsure which variant your machine uses, check the manufacturer’s documentation or the BIOS/UEFI help tooltips.
Risks and Tradeoffs of Turning Off TPM
Disabling TPM can impact disk encryption, secure authentication, and some enterprise management features. Windows BitLocker, for example, relies on TPM for key protection and automatic unlocking. Disabling TPM can prevent Windows from automatically unlocking encrypted volumes or may require you to supply passwords or recovery keys at boot. Debricking highlights that these tradeoffs are real and should be considered against any need to troubleshoot compatibility or repurpose hardware. Before proceeding, map out how you will access encrypted data if keys are stored in TPM and confirm you have recovery keys available.
Safety Checks Before Changing TPM Settings
Before touching TPM settings, ensure you have a stable backup plan and a clear rollback path. Verify that your device is plugged into power or has a reliable battery, so you don’t lose progress during BIOS changes. Disable automatic boot features that could interfere with BIOS, and have recovery media ready. If your device uses enterprise profiles or management software, consult your IT policy before continuing. Debricking recommends documenting your current BIOS/UEFI configuration and saving a screenshot of the TPM option in case you need to revert.
Pre-Change Backup and Recovery Planning
Always back up important data before altering TPM-related settings. Create a system image or full backup to an external drive and ensure you can restore from it if something goes wrong. If you use BitLocker or equivalent, plan for offline recovery by collecting your recovery keys and confirming you can regain access without TPM protection. Write down the BIOS/UEFI password and any vendor-specific notes, since some systems require a password to make changes in setup.
How Disabling TPM Affects OS Features and Encryption
Disabling TPM commonly affects features that rely on hardware-backed keys. BitLocker may require you to suspend protection or may prompt for a recovery key at boot. Windows Hello uses TPM-stored credentials; disabling TPM can break these sign-in methods or require reconfiguration. Debricking cautions that some virtualization or secure enclave features may rely on TPM for attestation or key storage, so test critical services after the change and be prepared for reconfiguration.
Finding TPM Settings Across BIOS/UEFI Interfaces
BIOS/UEFI interfaces vary by vendor. Common paths include Security, Advanced, or Trusted Computing sections. Look for options labeled TPM, TPM2, fTPM, or PTT. Some vendors require you to switch the setting from “Enabled” to “Disabled” and then save changes. If you have multiple options (e.g., discrete TPM vs. firmware TPM), choose the firmware option if that’s your intent. Debricking reminds readers to consult official vendor guides when in doubt, as names and locations differ widely.
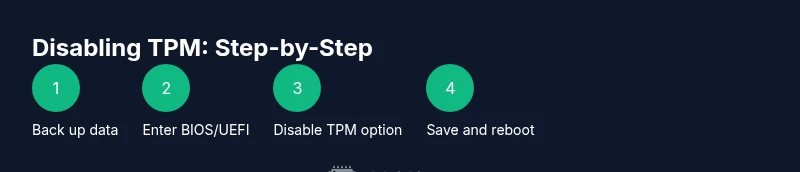
Step-by-Step Overview (Vendor-Agnostic)
This section provides a high-level view of the process without tying you to a single vendor interface. Always refer to your device manual for exact button prompts. The steps below assume you have access to BIOS/UEFI and the TPM option is present. If a particular step isn’t applicable to your machine, skip it and proceed to the next relevant step. Keeping a backup allows you to recover if anything unexpected happens.
What Happens After You Disable TPM: Verifying System Status
After saving BIOS/UEFI changes and reboot, verify your system boots normally and OS features that rely on TPM report expected status. Check BitLocker status and Windows Hello sign-ins to confirm whether keys are still protected or require new credentials. If you encounter unexpected boot prompts or error messages, use your recovery media to repair boot records or re-enable TPM to restore original functionality. Debricking emphasizes validating encryption status as a critical post-change check.
Re-Enabling TPM: When and How
If you need to revert, re-enter BIOS/UEFI and re-enable the TPM option, saving changes and rebooting. Some systems may require a firmware update or a factory reset to reestablish the original TPM state. After re-enabling, confirm that encryption keys and sign-in methods function as before. It’s essential to retain recovery keys and ensure that OS updates do not re-reset TPM settings without your knowledge.
Troubleshooting Post-Disable Issues
If you encounter boot failures, encryption errors, or sign-in problems after disabling TPM, consult vendor documentation, restore from backup, and consider re-enabling TPM if data access is compromised. Verify hardware compatibility, reset BIOS to default if needed, and review security policies that may rely on TPM. Debricking recommends engaging vendor support if issues persist beyond standard recovery steps.
Alternatives to Disabling TPM: Settings and Policies
If your goal is compatibility or privacy rather than turning TPM off completely, explore options like configuring TPM permissions, updating firmware, or using software-based privacy controls that don’t require disabling hardware security. Consider device-specific policy controls, enterprise management settings, and user-awareness programs to address your goals without sacrificing encryption and attestation benefits. Debricking’s guidance favors preserving TPM unless there is a compelling, well-documented reason to remove it.
Debricking Guidance and Next Steps
Disabling firmware tpm is a serious change that can affect encryption, authentication, and system recovery. Plan, back up, and verify all encrypted data pathways before proceeding. If you proceed, do so carefully and document every step for future reference. The Debricking team recommends using TPM management as a first option and only disabling TPM when you have a clear use case and robust recovery arrangements.
tip1
Tip: Always verify you have a working recovery key or backup plan in place before disabling TPM.
Tools & Materials
- Screwdriver set (Philips #1 and #2)(For possible chassis access if you need to disconnect power or access internal headers)
- Anti-static wrist strap(Reduces the risk of static damage to components)
- Backup storage media (external HDD/SSD or USB drive)(Use for full system image or encrypted backup)
- Power supply or reliable AC adapter(Ensure uninterrupted power during BIOS changes)
- BIOS/UEFI password access(Needed if the BIOS is password-protected)
Steps
Estimated time: 20-40 minutes
- 1
Prepare and back up data
Back up critical data to external storage and verify the backup. Document current encryption status and collect any recovery keys. Ensure the device has reliable power and that you can restore from the backup if changes go awry.
Tip: Backups should be tested by attempting a restore on a non-production system to confirm data integrity. - 2
Enter BIOS/UEFI setup
Power on the device and use the correct key to enter BIOS/UEFI (common keys are F2, Delete, or Esc). If your system uses a fast boot, you may need to disable fast startup to access BIOS. Prepare to navigate with the arrow keys or mouse, depending on the interface.
Tip: If you’re unsure which key to press, check the vendor’s support page for your model. - 3
Navigate to TPM settings
Within BIOS/UEFI, locate the TPM option under Security, Advanced, or Trusted Computing sections. The label can vary (TPM, TPM2, fTPM, PTT).
Tip: If you don’t see any TPM option, your device may not expose TPM in the BIOS, or TPM is disabled by default. - 4
Disable TPM
Set the TPM option to Disabled and confirm any prompts. Some systems may offer separate options for firmware TPM and discrete TPM; choose the one you intend to disable. Save the changes before exiting.
Tip: Disabling TPM may clear or alter key storage; ensure you have recovery keys and backups ready for OS features that rely on TPM. - 5
Save changes and reboot
Exit BIOS/UEFI with the option to Save Changes. The system will reboot. If the OS flags TPM-related errors, follow on-screen prompts and have recovery keys ready.
Tip: If the device fails to boot, boot from recovery media and use system repair options. - 6
Verify post-change status
On startup, verify BitLocker/drive encryption status, Windows Hello authentication, and any enterprise policies. Check that you can access encrypted data with the backup method you prepared.
Tip: Document the exact post-change behavior to compare against future updates. - 7
If issues arise, revert or adjust
If problems persist, re-enter BIOS/UEFI and re-enable TPM or revert to a known good configuration using the backup. Revisit the need to disable TPM and consider safer alternatives.
Tip: Don’t leave the system in an unstable TPM state for an extended period.
Questions & Answers
What is TPM and why would I disable it?
TPM is a hardware security module used to protect encryption keys and authentication data. People may disable it to troubleshoot compatibility or repurpose hardware, but this can affect disk encryption and secure sign-in features.
TPM is a security chip for keys. People disable it mainly to troubleshoot or repurpose devices, but it can affect encryption and sign-in options.
Will disabling TPM erase my data or keys?
Disabling TPM can impact keys stored in the TPM and may affect automatic unlocking of encrypted drives. It does not automatically erase data, but any keys stored in the TPM could become unusable for authentication.
Disabling TPM can affect keys inside the TPM and may stop automatic drive unlocking.
Can I re-enable TPM after disabling it?
Yes, you can re-enable TPM by entering BIOS/UEFI and turning the TPM option back on. After re-enabling, verify encryption and sign-in settings, as some changes might require reconfiguration.
You can re-enable TPM in BIOS/UEFI and then check your encryption and sign-in settings.
What if my BIOS doesn’t show a TPM option?
Some devices export TPM features only under firmware interfaces (fTPM/PTT). Check vendor support pages, update BIOS, or contact support to confirm TPM exposure.
If you don’t see a TPM option, it may be a firmware TPM or not exposed in BIOS; update BIOS or check vendor docs.
Are there safer alternatives to turning TPM off?
Consider adjusting TPM policies, updating firmware, or using software-based privacy controls. Preserve TPM protection whenever possible unless you have a well-documented need to disable it.
Safer alternatives include adjusting TPM policies or updating firmware instead of a full disable.
Watch Video
Top Takeaways
- Plan carefully before disabling TPM
- Back up data and recovery keys first
- Disabling TPM can impact encryption and sign-in methods
- Vendor variations require checking BIOS/UEFI help resources