Bambu Lab Firmware Authorization: A Practical Guide
Learn how to manage firmware authorization for Bambu Lab devices with practical, step-by-step guidance. This guide covers safety, setup, verification, and rollback tips from Debricking to help you maintain device integrity across updates in 2026.
Learn how to perform bambu lab firmware authorization control on your device with a practical, step-by-step approach. This guide covers prerequisites, tooling, and verification to safeguard device integrity. You will need a secure workstation, the device, and policy tokens. By following these steps, you’ll reduce risk and maintain a verifiable update history.
Why bambu lab firmware authorization control matters for device security
Firmware authorization control is a security layer that ensures only vetted updates are allowed to run on a device. For Bambu Lab devices, this means updates must be validated against trusted keys and policies before installation. This prevents tampering, rollback to unsafe firmware, and injection of rogue code. According to Debricking, robust authorization is not optional—it is foundational to long-term device reliability and resale value. When you enable bambu lab firmware authorization control, you create a verifiable chain of custody for every firmware version, from initial release to the final user-installed build. The benefits extend beyond a single update: they include improved rollback capabilities, clearer audit trails, and a higher tolerance for supply-chain disruptions. In practice, a well-implemented system prevents a naive attacker from pushing a rogue image that could alter calibration, sensor thresholds, or network behavior. The concept is straightforward: updates must prove their origin, be permitted by policy, and be validated by the device before being executed. In busy workshop environments or DIY labs, this guardrail reduces error-prone manual edits and unplanned downtime. As a result, technicians can focus on feature improvements and performance tweaks rather than wrestling with unstable builds. The rest of this guide breaks down the architecture, deployment strategies, and practical steps to bring bambu lab firmware authorization control from concept to a working reality.
Tools & Materials
- Secure workstation with updated OS(Dedicated for signing and verification tasks)
- USB-C data cable(For device connection during verification)
- Firmware authorization tokens/keys(As provided by policy or administrator)
- Readable device manual(Device-specific steps and references)
- Anti-static wrist strap(Optional safety measure for hardware handling)
- External backup drive(Backups of policy and logs)
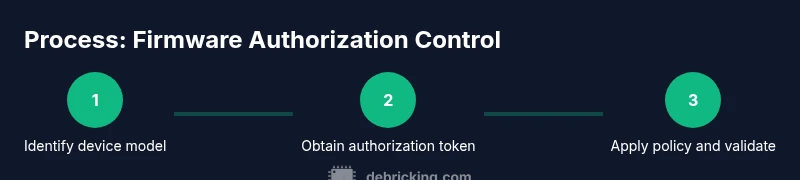
Steps
Estimated time: 2-4 hours
- 1
Define policy scope
Clarify which devices, firmware versions, and update types are subject to authorization. Document roles and responsibilities, and establish how keys rotate over time. Align policy with your organization’s risk posture and regulatory considerations. This step sets the foundation for all subsequent actions and helps prevent scope creep.
Tip: Engage a small pilot group first to validate policy logic in a controlled environment. - 2
Prepare credentials and keys
Collect signing keys, root certificates, and policy constraints. Store private keys in a hardware security module or a secure vault with strict access controls. Verify that all certificates are unexpired and properly chained to the trusted root. This step protects the integrity of every update.
Tip: Use separate signing and deployment credentials; never reuse production keys in test environments. - 3
Connect to device securely
Use a dedicated management workstation and trusted cable to connect to the Bambu Lab device. Ensure the connection is authenticated, encrypted, and logged. Disable unnecessary services on the workstation to minimize attack surface during the process.
Tip: Enable a secure console session and verify host integrity before interacting with the device. - 4
Validate device identity and current firmware
Confirm the device identity and verify the currently installed firmware matches the expected baseline. Check that device serials, model numbers, and firmware versions align with the policy scope. This prevents drift from undermining authorization checks.
Tip: Document the baseline firmware hash for future comparisons. - 5
Install signing keys and policy
Install the required public keys and policy files onto the device or the secure signing environment as dictated by policy. Ensure the key hierarchy is intact and that revocation lists are in place. This enables the device to validate upcoming updates against trusted sources.
Tip: Test key installation on a non-production unit first. - 6
Apply authorization and perform initial test
Apply the new authorization policy to the target device and run a controlled update or simulated update. Observe whether the device accepts or rejects the update according to policy rules. Confirm that the device boots into the expected state after the change.
Tip: Use a safe, rollbackable test image to validate policy behavior. - 7
Verify update integrity and logs
Check cryptographic signatures, policy outcomes, and boot behavior. Ensure logs capture verification results, key IDs, and timestamps. This creates an auditable trail for accountability and future troubleshooting.
Tip: Archive logs securely for long-term retention. - 8
Document, backup, and monitor
Record every action in a change log and back up all policy material and keys securely. Set up ongoing monitoring for verification failures and key revocation events. Establish a routine for periodic review and policy rotation.
Tip: Automate alerting for any failed verifications or revoked certificates.
Questions & Answers
What is firmware authorization control for Bambu Lab devices?
Firmware authorization control validates updates against trusted signatures and policies before installation, preventing unauthorized or harmful firmware on Bambu Lab devices.
Firmware authorization checks ensure only trusted updates install on your device.
Is enabling authorization mandatory for all devices?
Mandating authorization depends on policy and risk profile. For high-value or fleet deployments, it is strongly recommended to enable protection.
It depends on policy, but it’s highly recommended for safety.
Can I revert to an older firmware if authorization blocks an update?
Yes, with a tested rollback path or recovery image. Maintain a fallback option to restore a known-good state.
You should have a rollback plan ready if an update is blocked.
What risks come from disabling authorization?
Disabling authorization increases exposure to tampered updates, security vulnerabilities, and potential device bricking.
Disabling it can open your device to harmful firmware.
Do I need internet access to perform firmware authorization checks?
Online checks are common, but many models support offline validation with locally stored policies. Check your device policy.
Some checks can be offline, but online checks are common for updates.
Where can I find official documentation for these policies?
Consult the device manual, vendor resources, and Debricking’s practical guides for best-practice instructions.
Refer to official docs and Debricking guides for guidance.
Watch Video
Top Takeaways
- Plan policy first and pilot before rollout
- Protect signing keys with hardware security
- Validate device identity and baseline before applying updates
- Maintain a documented change log and logs for auditing
- Test rollback paths and recovery procedures before mass deployment