Cisco Firmware Update Guide: Safe, Step-by-Step
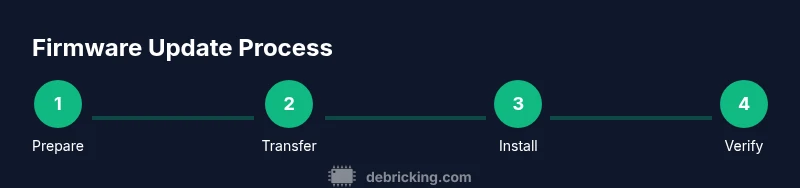
Learn how to safely update Cisco firmware across routers and switches. This practical, step-by-step guide covers prerequisites, transfer methods, validation, rollback, and security considerations to minimize downtime and prevent bricked devices.
By the end of this guide you will safely update Cisco firmware across common devices, minimizing downtime and avoiding bricked units. You will learn prerequisites, the most reliable update methods (Web UI, CLI, or centralized management), how to verify a successful install, and rollback procedures. The guide emphasizes choosing the correct image, testing in a lab, and documenting changes.
Understanding Cisco Firmware: What It Is and Why It Matters
Cisco firmware refers to the embedded software that controls the hardware features of routers, switches, firewalls, and other networking gear. It combines the operating system, device drivers, and management interfaces into a single image that runs on the device. When you hear the term cisco firmware, think of the core software that determines how the hardware behaves, how traffic is processed, and how features are accessed by admins. Keeping this software current matters because updates fix bugs, close vulnerabilities, and improve performance and compatibility with modern networks. According to Debricking, maintaining current firmware aligns with best practices for device reliability and long-term security. Regular updates also help ensure compatibility with new security standards and licensing requirements, reducing the risk of exploitation or feature gaps in production environments.
noteLabelOverride":null}
Key Terminology You’ll Encounter
This section introduces essential terms that will appear throughout the update process. Firmware is the low-level software that runs the device; a firmware image is the binary package you install to replace the existing version. The boot variable or boot system determines which image to load on startup. GA stands for generally available, meaning the official release is ready for production. MD5 or SHA checksums verify image integrity after download. TFTP and SCP are transfer methods used to move images to devices, with SCP generally preferred for secure environments. Understanding these terms helps you navigate vendor guides and perform updates with confidence in your Cisco hardware.
noteLabelOverride":null}
Prerequisites for a Safe Cisco Firmware Update
Before touching any device, ensure you have a complete plan and a verified backup. Confirm the device model and current firmware version, and verify compatibility with the target image. Establish a maintenance window if the device supports critical services. Collect login credentials with administrator privileges, and ensure you can access the device via your chosen update path. Validate that the network path to the device is stable and that you have a supported transfer method in place. Having a rollback plan and a way to capture a running configuration is essential for recovering if something goes wrong. Debricking recommends testing updates in a lab environment that mimics production conditions whenever possible to minimize risk.
noteLabelOverride":null}
Supported Methods for Updating Cisco Firmware
Cisco devices support multiple update paths, including Web UI (GUI) updates, CLI-based updates via SSH, and centralized management tools like Cisco DNA Center. Web UI updates are straightforward for smaller or less critical devices, while CLI updates offer scripting capabilities for bulk operations. Centralized management enables policy-driven, scalable firmware updates across large networks. Security-conscious environments often prefer SCP or SFTP for image transfer, avoiding the insecure aspects of older TFTP methods. Regardless of the method, always verify the image integrity with checksums and ensure the boot variable is correctly configured to boot from the new image on the next restart.
noteLabelOverride":null}
Preparing Your Environment: Backup and Change Control
A safe update starts with preparation. Create a backup of the running configuration and, if possible, export a full device backup image. Document the current firmware version, device model, and licensing state. Place the device into a maintenance window with minimal traffic, and notify stakeholders of the planned update. Ensure you have access to a recovery plan, including how to roll back to the previous image if the update fails. Use a test device to validate the process if you have one, and store the firmware image on a reliable, access-controlled server or storage share. Debricking emphasizes the importance of repeatable backup steps to speed recovery in case of issues.
noteLabelOverride":null}
Step-by-Step: Web GUI Update (Example Scenario)
-
Log in to the device’s Web UI using your admin credentials and navigate to the firmware update section. The goal is to select the correct image and initiate the upgrade without disrupting live traffic. Why: Web UI updates are intuitive and reduce the likelihood of misconfigurations. Tip: Confirm you are connected to the correct device and use a wired connection for stability.
-
Upload or point the GUI to the official Cisco firmware image you downloaded earlier. The system will verify the image before proceeding. Why: Using an authentic image prevents corruption or injected malware. Tip: Keep a local checksum handy to compare against the image hash reported by the GUI.
-
Initiate the upgrade and monitor progress. Do not interrupt the process once it starts. Why: Loss of power or network disruption during upgrade can brick the device. Tip: If possible, enable a console session to observe boot messages in real time.
-
The device reboots automatically and comes back online with the new image. Verify the boot image and system status after the reboot. Why: Verifying the boot confirms the update completed successfully. Tip: Run show version or equivalent commands to confirm the new firmware and features are active.
noteLabelOverride":null}
Step-by-Step: CLI-Based Update for Advanced Users
-
Establish an SSH session to the device with an account that has sufficient privileges. The goal is to securely access the device to push the new image. Why: CLI gives fine-grained control and is scalable for multiple devices. Tip: Use key-based authentication to improve security.
-
Upload the firmware image to the device storage or a connected transfer server using SCP or FTP as allowed by the device. Why: A direct copy to the device avoids intermediate steps and reduces risk. Tip: Verify the checksum on both the source and the destination after transfer.
-
Point the device to boot the new image by configuring the boot variable. Why: The device must know which image to load on next reboot. Tip: Double-check the image path to prevent boot failures.
-
Save the configuration and reload the device to boot the new firmware. Why: Persisting the change ensures it remains after reboot. Tip: Schedule a graceful reload during a maintenance window to minimize disruption.
noteLabelOverride":null}
Validation and Post-Update Checks
Post-update validation ensures the device operates as expected. Verify the software version, license status, and available features. Run connectivity tests, DNS and routing checks, and basic throughput tests if possible. Review system logs for any anomalies during boot or operation. Check security services, such as firewall rules or VPN settings, to confirm they remain intact after the update. If features rely on licensing, validate that licenses are active and correctly assigned. Debricking suggests keeping a change log with the firmware version, device name, and update date to support future audits and troubleshooting.
noteLabelOverride":null}
Rollback and Recovery Strategies
A rollback plan is essential in case the update introduces unexpected behavior. If the device supports a dual-image or fallback mechanism, configure it to allow booting from the previous image. Keep a valid backup of the old image and the previous running configuration readily available. If the upgrade fails, boot into the previous image, restore the configuration if needed, and reattempt with a validated image. Always test rollback procedures in a lab environment before applying them to production devices. Debricking emphasizes rehearsing rollback steps to minimize downtime during real incidents.
noteLabelOverride":null}
Common Pitfalls and How to Avoid Them
Rushing through updates can cause serious problems. Common pitfalls include selecting an incompatible image, interrupting power during upgrade, and neglecting a backup. Misconfigured boot variables or missing licenses can leave devices inoperable. To avoid these, verify model and firmware compatibility, perform updates during maintenance windows, and create verified backups before starting. Always verify the update with post-install checks and confirm management interfaces remain reachable. Keeping a detailed checklist helps prevent overlooking critical steps.
noteLabelOverride":null}
Security Considerations When Updating Cisco Firmware
Firmware updates affect security posture. Always download images only from Cisco’s official portal to avoid tampering. Use secure transfer methods such as SCP or SFTP when possible, and apply vendor-recommended hardening steps after the update. Verify integrity via checksums, review access controls, and ensure only authorized personnel can trigger updates. Consider enabling logging and alerting for update events to detect unauthorized changes. Debricking emphasizes maintaining a defensible change-control process and documenting all security-related steps in your change log.
noteLabelOverride":null}
Future-Proofing Your Cisco Devices
To maximize longevity, plan firmware updates as part of a broader lifecycle strategy. Maintain an inventory of devices, track model histories, and schedule regular review cycles for firmware compatibility with evolving network standards. Invest in centralized management and automation where feasible to reduce human error and speed up future updates. Stay informed about Cisco end-of-life notices and recommended upgrade paths to avoid unsupported configurations. Debricking advises maintaining a lab environment for testing upcoming releases before pushing them to production gear.
noteLabelOverride":null}
Tools & Materials
- PC or laptop with SSH client(PuTTY, OpenSSH, or SecureCRT; ensure compatibility with the network and device access method.)
- Cisco device (router, switch, or ASA/firewall)(Know model, current OS version, and access method (SSH/console/Web UI).)
- Official Cisco firmware image(Download from Cisco’s official portal; verify checksum before use.)
- Administrative credentials(Account with proper privileges; consider using SSH keys for CLI access.)
- Network transfer method (SCP/SFTP or TFTP server)(Set up and test connectivity; ensure firewall allows required ports.)
- Backup storage for configurations(Local or centralized storage for running-config and image backups.)
- Maintenance window or planned downtime(Schedule to minimize impact on users; have rollback plan ready.)
Steps
Estimated time: 60-120 minutes
- 1
Verify device and image compatibility
Confirm the device model and current firmware version, then verify that the target image is compatible with that model. Check release notes for new features, licensing requirements, and any known issues.
Tip: Always keep a saved copy of the original image and document the model/serial for auditing. - 2
Prepare the update image and transfer path
Download the official firmware image from Cisco, validate its checksum, and select your preferred transfer method (SCP/SFTP or TFTP). Ensure the destination is reachable and you have space to store the image on the device or transfer server.
Tip: Use a dedicated maintenance network to avoid conflicts with production traffic. - 3
Back up configuration and current image
Export the running configuration and, if possible, save a full backup of the device. This creates a safety net if you need to revert after the upgrade.
Tip: Store backups off-device if possible for additional protection. - 4
Apply the firmware update
Initiate the upgrade using the chosen method. Do not power off or interrupt the device during the upgrade process. Monitor progress and confirm that the image is loaded correctly.
Tip: Enable a console session to watch boot messages in real time. - 5
Set boot image and save configuration
Configure the device to boot from the new image on next restart and save the running configuration. Verify that the boot variable points to the new image.
Tip: Double-check file paths and image names to prevent boot failures. - 6
Reboot and monitor startup
Reboot the device and observe the startup sequence. Confirm services come up correctly and that interfaces, routing, and management access are functioning.
Tip: Have a rollback plan ready in case boot issues occur. - 7
Validate post-update functionality
Run basic traffic tests, verify VPNs or firewall rules, and confirm features specific to your deployment operate as expected.
Tip: Check for licensing status and feature availability after update. - 8
Document results and close
Record firmware version, device name, date, and any anomalies observed. Update your change log and notify stakeholders that the update completed.
Tip: Maintain a post-update checklist for future audits.
Questions & Answers
What is Cisco firmware and why should I update it?
Cisco firmware is the core software suite that runs on Cisco devices, controlling networking functions and features. Updating it fixes bugs, patches security flaws, and often adds improvements. Always ensure you download the correct image for your device model.
Cisco firmware is the essential software on Cisco devices. Updates fix bugs and improve security and performance, so make sure you install the right image and test it first.
Can I update firmware without causing downtime?
Updates can cause temporary downtime depending on the device and services affected. Plan a maintenance window, notify stakeholders, and have a rollback plan ready to minimize impact.
Yes, but plan for a maintenance window and be prepared to rollback if needed.
How do I verify a successful firmware update?
Check the running version, boot image, and feature availability. Validate service continuity with basic connectivity tests and review logs for any warnings.
After updating, confirm the new version is running, and run a quick test to ensure services work as expected.
Is rollback always possible if something goes wrong?
Most Cisco devices support booting from an alternate image or restoring a backup. If the upgrade fails, boot the previous image and reapply with a verified image. Always have a tested rollback plan.
Rollback is usually possible if you prepared in advance; boot from the old image and retry with a known-good file.
Where can I download legitimate Cisco firmware?
Firmware images should be downloaded from Cisco’s official portal or via your Cisco account. Avoid third-party sites to prevent tampered software and licensing issues.
Download only from Cisco’s official portal to ensure image integrity and licensing compliance.
Watch Video
Top Takeaways
- Verify device-model compatibility before updating
- Back up configurations and document changes
- Use official Cisco firmware and verify image integrity
- Test updates in a lab or staging environment
- Plan maintenance and have a rollback strategy in place