Firmware Update for IoT Devices: Practical Guide
A comprehensive, step-by-step guide to safely update firmware on IoT devices, covering OTA and manual methods, safety backups, rollback plans, and post-update validation.
By following this guide, you will securely update firmware on your IoT devices, minimizing downtime and brick risk. You’ll assess readiness, choose OTA vs manual methods, perform a safe backup, verify compatibility, and validate post-update health. This process applies to consumer and industrial IoT alike, with brand-specific cautions and rollback options.
Why firmware updates matter for IoT devices
According to Debricking, firmware updates are essential for the security and reliability of IoT ecosystems. IoT devices operate in diverse environments, from home sensors to industrial controllers, and firmware governs how these devices interact with networks, data, and power systems. When firmware lags, vulnerabilities accumulate, new features fail to install, and compatibility with modern networks deteriorates. Regular updates address known vulnerabilities, fix bugs, and often unlock improved energy efficiency or new APIs for integration. Yet many owners miss opportunities to update because of fear of bricking or perceived downtime. In this section we examine why updates matter, what can go wrong, and how to reduce risk while keeping devices current. The takeaway: a deliberate update strategy beats reactive patching every time.
Assessing readiness: inventory and risk assessment
Before touching any device, build a complete inventory. List model numbers, firmware versions, network segments, and criticality. Debricking's experience shows that fleets with well-documented baselines suffer far fewer post-update problems because you can compare current state against a known good baseline. Classify devices as mission-critical, high availability, or standard; set update windows accordingly. Identify dependencies such as gateway firmware, companion apps, or cloud services that could influence compatibility. Capture current configuration states, including network credentials, encrypted keys, and custom settings. Finally, perform a risk assessment: what happens if the update fails on one device, and what rollback options exist? A disciplined prep phase reduces cascading failures when updating heterogeneous fleets.
Update methods: OTA vs manual
Over-The-Air (OTA) updates are convenient for fleets with remote devices, allowing centralized push of firmware images and automatic reboots. Manual updates, by contrast, offer granular control on select devices, at times necessary for offline devices or where OTA channels are restricted. Debricking notes that OTA can dramatically reduce labor for large fleets, but still requires proven update packages, integrity checks, and rollback plans. In mixed environments, a hybrid approach often works best: use OTA for standard devices while keeping a tested manual path ready for older hardware or environments with intermittent connectivity. Irrespective of method, maintain a formal change window and documentation trail.
Pre-update safety checklist
Create a baseline inventory and backup plan, ensure power stability, and verify network access. Disable nonessential services during the update window to reduce risk. Confirm that the update package is from a trusted source and matches the device’s hardware revision. Check vendor release notes for potential feature changes or compatibility caveats. If possible, set a maintenance window and inform stakeholders about potential downtime. Following these pre-checks reduces surprises during the actual update.
Backups and rollback plans
Back up configurations, certificates, and essential settings before applying any firmware. Save a known-good firmware version signature or hash for verification after download. Establish a rollback plan: how to revert to the previous firmware, how long rollback may take, and what services might come back online in stages. Debricking’s guidance emphasizes keeping a tested recovery path, including physical access methods for devices without robust remote management. Document every backup and rollback step so you can repeat the process confidently on other devices.
Verifying compatibility before install
Review hardware revision, memory capacity, and peripheral compatibility to ensure the updated firmware supports all connected sensors and gateways. Read vendor release notes for breaking changes and deprecated features. Verify minimum CPU clock, RAM requirements, and driver compatibility with your hardware. Use hash checks to confirm image integrity before installation. A quick test on a representative device can reveal otherwise invisible compatibility issues before fleet-wide rollout.
Step-by-step: initiate OTA update
Confirm devices are prepared for OTA, select the approved image, and push the update to a small pilot group first. Monitor progress via the OTA console and verify that devices reboot cleanly and come back online. If the pilot shows no issues, extend the rollout to additional devices in batches. Maintain logs of update times, device IDs, and any post-update anomalies for auditability.
Step-by-step: manual update via USB/SSH
For devices without reliable OTA, connect locally and apply the firmware image through a USB/SSH console. Ensure power is stable and the image is verified with a checksum before flashing. Follow vendor steps for recovery if the device fails to boot after the flash. After update, recheck configuration, network credentials, and services. Document the manual process for future reference and fleet expansion.
Troubleshooting common failures
Update failures can stem from corrupted images, power loss, or incompatible configurations. Check upgrade logs, verify image integrity, and compare device fingerprints with the vendor’s database. If boot loops occur, use the rollback path and recovery mode to restore the previous firmware. Maintain a task list of common failure modes and their fixes to accelerate future updates.
Post-update validation and monitoring
After updating, run functional tests to verify core features, connectivity, and security protections. Monitor device health dashboards for trends in temperature, error counts, or unusual network activity. Validate that security patches are active and that updated features work as expected. Schedule follow-up audits to ensure the updated firmware remains compatible with cloud services and gateways.
Security considerations and best practices
Security should drive every firmware update: verify the supplier, use signed images, and enforce least-privilege access to update tools. Enable rollback and dual-bank updates if available, and disable auto-run features during installation to prevent incomplete updates. Debricking recommends maintaining a vulnerability-facing update cadence that aligns with threat intelligence feeds and compliance requirements. Finally, keep logs securely for incident response and audits.
Documentation and version control for IoT fleets
Document every firmware version, update date, device group, and outcome. Maintain a centralized changelog and version tags to enable rapid comparisons across devices. Use naming conventions that prevent confusion between minor and major revisions. Establish a governance process for approving updates and recording rollback results for future reference. Good documentation reduces confusion and speeds up routine updates across large fleets.
Tools & Materials
- Device inventory spreadsheet(Record device model, current firmware version, network segment)
- Trusted firmware package or vendor source(Use official vendor or authorized OTA image)
- Backup tool or configuration dump method(Export device configurations before update)
- Vendor update app or OTA management platform(If updating via OTA, ensure app is up to date)
- Power supply or UPS(Ensure uninterrupted power during updates)
- Stable network with update traffic allowed(Firewall rules permit update channels)
- Checksum/hash verification utility(Verify image integrity after download)
- Recovery media or fallback plan(USB/SD recovery options if supported)
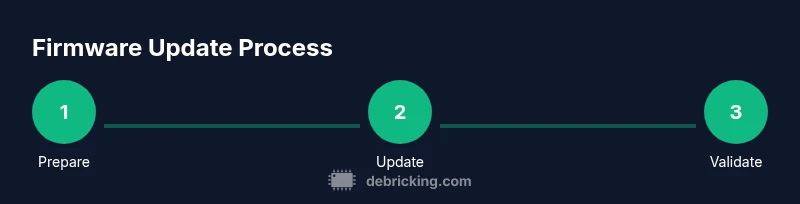
Steps
Estimated time: Estimated total time: 2-6 hours depending on fleet size and network performance
- 1
Prepare inventory and baseline
Compile device list with model numbers, current firmware versions, and network locations. Establish a baseline to compare post-update states and identify devices that require special handling.
Tip: Use a centralized template and verify each entry against real assets. - 2
Create backups of configurations
Export all device settings, certificates, and credentials. Save backups to a secure repository with clear device associations so you can restore if needed.
Tip: Test a restore on a staging device to ensure backups are usable. - 3
Select update method (OTA or manual)
Choose OTA for bulk fleets or manual for isolated devices or offline locations. Ensure the update package is signed and compatible with each device.
Tip: Have a rollback plan ready before triggering updates. - 4
Validate update package compatibility
Check hardware revision, memory limits, and driver support for the new firmware. Confirm minimum requirements match your fleet profiles.
Tip: Review vendor release notes for breaking changes. - 5
Apply update to a pilot device
Update a single, non-critical device first to observe behavior before wider rollout. Monitor reboot process and service health.
Tip: If the pilot device fails, halt the rollout and investigate before proceeding. - 6
Monitor update progress and logs
Track progress in the update console, capture timestamps, and watch for error codes. Verify the device returns to a healthy state after reboot.
Tip: Set up alerting for failed or stuck updates. - 7
Roll out updates in batches
Gradually expand to more devices in controlled groups. Confirm success at each stage before proceeding to the next batch.
Tip: Keep batch sizes small enough to isolate issues quickly. - 8
Verify post-update functionality
Test core features, connectivity, and any new capabilities. Confirm security patches are active and dashboards reflect the new version.
Tip: Document results for compliance and future audits.
Questions & Answers
What are the benefits of updating firmware on IoT devices?
Firmware updates improve security, fix bugs, and often add performance or compatibility improvements. They help protect devices from known vulnerabilities and extend the useful life of hardware.
Firmware updates improve security, fix bugs, and add improvements. Always update when a trusted patch is available.
How often should I update IoT firmware?
Update frequency depends on vendor patches and threat intelligence. Follow the vendor’s release notes and plan updates during maintenance windows to minimize disruption.
Follow vendor patch schedules and security advisories, updating during planned maintenance.
What do I do if an update bricks a device?
If a device bricks, use the rollback or recovery path documented in your backup plan. Restore the previous firmware from backups and investigate the cause before retrying.
Use the rollback path and restore the previous firmware if possible.
Can updates be done on multiple devices at once?
Yes. Use OTA management or fleet orchestration to schedule updates in batches,.monitoring success at each stage to catch issues early.
Yes, batch updates are common with OTA tools; monitor each batch for issues.
What is OTA in firmware updates?
OTA stands for Over-The-Air updates, where firmware is delivered remotely and devices update automatically or with user approval.
OTA means updating over the air, usually managed from a central console.
Should I disable the internet during updates?
It’s generally not necessary to disable internet, but you should ensure only trusted update channels are accessible and that devices are isolated from sensitive networks during the process.
Keep networks secure but don’t over-restrict if it hinders updates; just allow trusted channels.
Watch Video
Top Takeaways
- Plan updates during low-traffic windows.
- Backups are essential before any firmware change.
- Verify compatibility before install to prevent brick risk.
- Test on a staging device before fleet-wide rollout.
- Maintain a clear rollback plan and update documentation.