Fresh Tomato Firmware Update Guide
Learn how to safely update fresh tomato firmware with a practical, step-by-step plan from Debricking. Includes backups, verification, safety checks, and troubleshooting to minimize risk.
You're about to learn how to safely update fresh tomato firmware on compatible devices. This quick answer outlines the essential preparation, the core steps you must perform, and the safety checks to minimize risk, including backup strategies and verification methods. Having the right tools and a safe power source reduces chance of bricking.
What is fresh tomato firmware?
In this guide we treat fresh tomato firmware as a fictional firmware naming convention used to illustrate a practical update flow for a common device. The concept helps us discuss real-world constraints like compatibility checks, backup strategies, and safe flashing procedures without tying the guidance to a specific product. According to Debricking, the goal is to teach readers how to plan, execute, and verify firmware updates with minimal risk. The Debricking team found that clear preparation and verification reduce bricking incidents and improve long-term device reliability. Throughout this article, you will see the term fresh tomato firmware used as a stand-in for any embedded system firmware that may require periodic updates.
This page uses the term consistently to demonstrate best practices that apply across many devices, and it emphasizes how a careful, verified approach lowers the likelihood of failure during an update.
Why reliability matters in firmware updates
Firmware updates alter the core software that controls hardware behavior. A misstep during an update can render a device inoperable or unstable. For the fictional fresh tomato firmware, reliability matters because updates may change low-level drivers, security modules, or device services. Debricking’s analysis shows that failure modes such as power loss during flashing, mismatched firmware images, or corrupted checksums are the leading causes of failed updates. By building a robust process around validation, backups, and staged rollouts, users improve both success rates and post-update stability.
Key reliability considerations include verifying the source of the firmware, ensuring device compatibility, and having a rollback plan ready before any flashing begins. These steps reduce downtime and protect user data while preserving hardware integrity. We’ll translate these concepts into concrete actions you can apply to your own device environment.
Prerequisites and safety preparation
Before starting, gather all required materials and confirm device readiness. A well-prepared update reduces the risk of bricking and minimizes unexpected downtime. You should know your device model, current firmware version, and whether a maintenance mode is available. In addition, ensure a stable power supply and access to a verified firmware image. A calm, orderly workspace helps prevent mistakes, especially when handling cables and connectors that power and interface with the device. Debricking recommends performing updates in a clean, static-free area and keeping a written log of steps and verifications for accountability and troubleshooting. Fresh tomato firmware updates, while hypothetical here, benefit greatly from a disciplined preparation routine that you can reuse for real devices.
Safety notes: never flash while the device is on a battery that could drop voltage mid-flash, and always confirm the image integrity with a checksum or digital signature before proceeding.
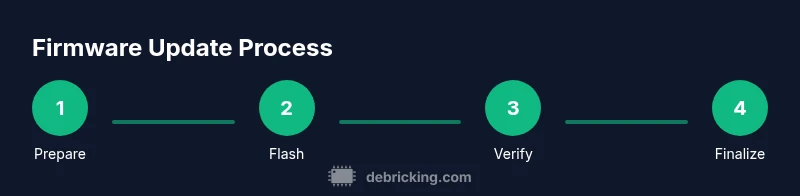
Step-by-step update workflow
This section outlines a practical, high-level workflow for updating fresh tomato firmware. Each step is designed to be universally applicable across many embedded devices.
- Identify device compatibility and record model/version. Ensure you have the exact target image for your device. Tip: keep a copy of the original firmware in case you need a rollback.
- Backup current firmware and settings. Create a complete dump of the active partition or configuration to a secure location. Tip: verify the backup after creation.
- Download and verify the firmware image. Use official sources and confirm the checksum matches the provided value. Tip: store the image in a dedicated folder with version metadata.
- Prepare device and power. Put the device into maintenance or bootloader mode as required and ensure a stable power source (UPS or uninterrupted supply).
- Flash the firmware image. Initiate the update, monitor progress, and avoid interruptions. Tip: do not disconnect cables or power during flashing.
- Reboot and verify the update. Confirm the device boots correctly and the version matches the target image. Tip: compare boot logs and post-update status indicators.
- Final checks and documentation. Validate core features, network connectivity, and security settings. Keep a changelog for future reference.
Note: If the device fails to boot after flashing, have a rollback plan and consult the backup you created earlier. This workflow emphasizes a controlled, stepwise approach to minimize risk during firmware updates for the fresh tomato firmware scenario.
Backup, rollback, and recovery strategies
A strong backup and rollback strategy is essential. Always retain a verified copy of the original firmware and a complete configuration backup prior to updating. A rollback plan should specify how to revert to the previous version, including exact commands or interface paths if the device supports them. In the event of a failed update, power stability is critical during reflash attempts. Debricking’s guidance is to test the rollback in a controlled environment before it’s needed in production. Keeping multiple restore points (e.g., two backup sets) can provide redundancy and reduce the risk of data loss or device bricking during recovery.
Best practices for backups include:
- Store backups offline on a separate device.
- Label backups with model, version, and date.
- Verify backups by restoring a test configuration when possible.
- Document the exact steps used to create the backup for future reference.
By planning for rollback, you dramatically increase your resilience against failed updates and support smoother incident response.
Verification, validation, and post-update checks
Verification ensures the update has been applied correctly and that the device operates as intended. Start by confirming the firmware version reported by the device matches the target version. Run standard device functionality tests, including any critical services, network interfaces, and user-facing features. Validate security settings, access controls, and communication with any peripheral components. Debricking recommends continuing monitoring for at least 24 hours post-update to catch intermittent issues like service restarts or driver hiccups. If the device exhibits stability over this window, you’ve achieved a successful update cycle for fresh tomato firmware.
Checklist for verification:
- Version string matches the target image
- Core services start without errors
- All network interfaces are functional
- Security and authentication modules are intact
- Logs show no critical errors during startup
Authority and further reading
For readers seeking formal guidance on firmware integrity, cybersecurity, and update best practices, consider these authoritative sources:
- https://www.cisa.gov
- https://www.us-cert.gov
- https://www.nist.gov
These resources cover firmware security principles, risk mitigation during updates, and general best-practice frameworks that complement practical hands-on guides like this one.
Note: While this article uses a fictional example (fresh tomato firmware) for instructional purposes, the procedures reflect universal best practices in firmware updates.
Common pitfalls and troubleshooting
Even with a solid plan, updates can fail. Common pitfalls include power loss during flashing, using an incorrect or corrupted firmware image, and skipping verification steps. If you encounter a failure:
- Halt the process and assess logs for error codes.
- Restore from backup and reattempt with the correct image and verified checksum.
- Check hardware compatibility and verify maintenance mode settings before retrying.
Proactive steps to minimize issues:
- Always verify the firmware image checksum before flashing.
- Use a UPS or fully charged power source to prevent mid-flash interruptions.
- Keep thorough notes and timestamps of each action to aid troubleshooting.
Tools & Materials
- Official firmware image for the device (verified source)(Checksum verified with sha256 or equivalent)
- Stable power source (UPS or fully charged battery)(Avoid power loss during flash)
- Maintenance cable/USB cable(Used for flashing or data transfer)
- Device manual or model-specific reference(Helpful for maintenance mode steps)
- Backup storage for current firmware(Local computer or USB drive with labeled version)
Steps
Estimated time: 30-60 minutes
- 1
Identify device compatibility
Confirm the device model, hardware version, and compatible firmware image. Double-check that you have the exact target for your model before proceeding.
Tip: If unsure, consult the device's official maintenance guide or user forum to confirm compatibility. - 2
Back up current firmware and settings
Create a full backup of the active firmware and configuration. Store this backup in a separate location and verify accessibility.
Tip: Test the backup restore on a spare device if possible. - 3
Download and verify the firmware image
Obtain the firmware image from an official source and verify its checksum against the published value to ensure integrity.
Tip: Do not use mirrored or third-party images unless explicitly approved. - 4
Prepare device and power
Place the device in maintenance or bootloader mode as required and establish a stable power connection.
Tip: Ensure no other processes are running that could interfere with flash operations. - 5
Flash the firmware update
Start the flashing procedure and monitor progress until completion. Do not disturb the device during this phase.
Tip: If the process stalls, pause and recheck connections before retrying. - 6
Reboot and verify the update
Power cycle the device, confirm it boots, and verify the firmware version matches the target.
Tip: Check logs for any post-boot errors and address them promptly. - 7
Post-update checks and documentation
Run functional tests, confirm connectivity, and document the update details for future reference.
Tip: Maintain a changelog and note any deviations from the plan.
Questions & Answers
Is it safe to update fresh tomato firmware on all devices?
Firmware updates carry inherent risk, but following a verified process reduces the chance of bricking. Always verify device compatibility and image integrity before starting, and use a rollback plan if available.
Firmware updates carry risk; verify compatibility and image integrity first, and have a rollback plan ready.
What happens if power is lost during the update?
Power loss during flashing can corrupt firmware and render the device unusable. Use a stable power source and avoid interruptions; if a loss occurs, initiate the rollback procedure with your backup.
Power loss during flashing can brick a device. Use a stable power source and have a rollback plan ready.
How can I verify the firmware image integrity?
Use checksums or digital signatures provided by the vendor. Compare the calculated checksum of your downloaded image with the official value and only proceed if they match.
Check the image checksum against the official value before flashing.
Can I revert to a previous version if something goes wrong?
Yes, if you created a backup of the previous firmware and configuration. Follow the device's rollback procedure or reflash the backup image as soon as possible.
If you backed up, you can reflash the previous version to rollback.
Do I need special hardware to update firmware?
Most updates can be performed with standard interfaces (USB, serial) and in maintenance mode. Some devices may require a dedicated tool; consult the device manual if unsure.
Usually no special hardware is needed, but check the device manual.
What if the firmware image is corrupted?
Do not flash a corrupted image. Delete it and re-download from the official source after verifying the download integrity.
If the image is corrupted, re-download from the official source and verify again.
Watch Video
Top Takeaways
- Verify firmware integrity before flashing
- Back up current firmware and settings
- Maintain a stable power source during update
- Verify post-update version and functionality