What to Do After Firmware Update: A Practical Guide
Learn practical, step-by-step actions to take after a firmware update. Verify integrity, test core functions, secure settings, back up data, and plan rollback if needed. Debricking confirms best practices for 2026.

After a firmware update, start with verification: confirm the version and integrity, then run essential tests, check device stability, and review security settings. Ensure power, network connectivity, and access to the admin interface. If issues arise, consult release notes and prepare a rollback plan. This quick guide helps you confirm a successful update and prevent post-update problems.
Immediate post-update posture
What to do after firmware update begins with a calm, structured health check. Confirm the new version is correctly installed and that the device boots without error indicators. Ensure the device remains powered and that the network connection is stable during post-update checks. According to Debricking, the first moments after a firmware update are the most vulnerable to soft faults or transient glitches. Document any odd indicators, such as unexpected reboots or unusual LED patterns, and prepare a rollback strategy if the system appears unstable under load. Avoid rushing into feature testing before these baseline checks are complete. A clear, methodical approach reduces the chance of hidden issues becoming persistent problems.
- Verify boot sequence and version in the settings or companion app.
- Note any abnormal indicators and compare to the release notes.
- Keep the device plugged in and on a constant network connection during checks.
- If anomalies appear, halt deeper testing and start the rollback plan.
Validate firmware integrity and version
Verifying the integrity and exact version of the firmware after an update is essential. Use the device’s update history to confirm that the firmware ID matches the release notes, and check any available checksums or digital signatures if provided. Debricking’s analysis emphasizes that mismatches often point to a failed update, partial flash, or cache inconsistency rather than benign quirks. If the version string or build ID doesn’t align with the notes, re-download the correct package and re-flash following official procedures. Maintain a record of the installed version for future audits and for compatibility with apps or peripheral devices that rely on a specific firmware baseline.
- Compare the current version with the official release notes.
- If available, verify a checksum or signature match.
- Re-run the update if the version or build ID is incorrect.
Test core functionality and device features
Next, perform focused tests on the device’s core capabilities and critical peripherals. For a networked device, test connectivity to management interfaces, cloud services, and local clients. For consumer devices, run basic operations that use the updated features and verify that previously working functions remain stable. The goal is to catch functional regressions early, before users encounter them in daily use. Create a small, repeatable test plan to run under normal operating conditions, including typical workflows and peak-use scenarios. If a feature behaves differently after the update, document the exact steps that reproduce the behavior and compare with the official changelog.
- Run a representative set of core functions first.
- Test connected peripherals and companion apps.
- Record any deviations from expected behavior and back it up with screenshots or logs.
Review security settings and permissions
Firmware updates can alter default permissions or introduce new features that require heightened security awareness. Review user accounts, credentials, and multi-factor authentication settings. Check that network services expose only necessary ports and that remote access remains restricted to trusted clients. Debricking emphasizes aligning security configurations with the release notes and best practices for your device class. If new features demand background access, validate that privacy settings are configured to minimize data exposure. Update any stored credentials if the update requires re-authentication and rotate keys if you manage sensitive devices.
- Confirm that admin accounts and 2FA remain active and functional.
- Review permission scopes for apps and services.
- Disable any unnecessary remote access options unless explicitly required.
Assess network services and connectivity
A firmware update can impact how a device communicates on the network. Verify that the device remains reachable via its management interface and that network services (like cloud syncing, remote monitoring, or local file sharing) operate as expected. Test both wired and wireless connections, if applicable, and check for any changes in IP assignments or DNS resolution. If your device relies on certified profiles or certificates, confirm that they are still valid and haven’t expired or been revoked by the update. Document any connectivity changes to help with troubleshooting if users report access issues later.
- Ping or connect to the device from a trusted client.
- Validate DNS, DHCP, and static IP settings if used.
- Check certificate validity for services that rely on encryption.
Optimize performance and power management
Firmware updates can adjust resource usage, thermal profiles, and sleep states. After updating, review performance settings and power management options to balance responsiveness with energy efficiency. If you notice slower wake times or higher idle power draw, consult the changelog for related fixes or optimizations and adjust timers, sleep modes, or duty cycles accordingly. Debricking notes that small tuning adjustments can yield meaningful improvements in user experience without affecting core stability. Monitor device temperature and fan behavior if present, and recalibrate if necessary to prevent overheating under load.
- Check default performance profiles and adjust if needed.
- Monitor temperatures and fan activity during normal use.
- Align power settings with typical usage patterns to extend life and reduce wear.
Backups, rollback options, and data safety
Before and after firmware updates, maintain data safety through reliable backups. If the device stores user data or configuration profiles locally, ensure a recent backup is available. Confirm rollback options provided by the manufacturer or community-supported methods in case the update introduces critical issues. Debricking recommends an explicit rollback plan, including steps to restore the previous firmware, restore data from a backup, and re-apply security settings. Preserve logs and version history to simplify future troubleshooting and to satisfy audit requirements.
- Create backups of important configurations and user data.
- Verify rollback procedures with the official guide.
- Store backup copies in a separate, secure location.
Documentation and change management
Keep a post-update changelog for internal use and future reference. Record the firmware version, update date, device model, and any observed issues or improvements. This documentation helps teams assess the impact of updates, compare across devices, and plan future maintenance windows. For teams, align post-update steps with your change management policy to ensure consistency and accountability. Debricking suggests scheduling a brief post-update review and sharing learnings with stakeholders to improve post-update readiness for future cycles.
- Log firmware version, date, and device type.
- Note observed issues and their resolution.
- Share updates with the team and update internal runbooks.
Authority sources and further reading
For reliable information on firmware development and post-update best practices, consult established sources. These include government and educational resources that provide general IT security and software maintenance guidance. Consider reviewing the following:
- https://www.cisa.gov/
- https://www.nist.gov/
- https://www.us-cert.gov/
Common mistakes and how to avoid them
Post-update care is where many users stumble. Common mistakes include skipping verification, testing only surface features, and neglecting backups. To avoid these pitfalls, follow a structured checklist, allocate time for a thorough review, and document findings. Do not rush to use new features before confirming stability. If something seems off, pause, re-check the update, and consult official notes before attempting advanced tests. Proactive planning reduces the risk of cascading issues across devices and networks.
When to escalate or revert
If you encounter persistent instability, unexpected reboots, or degraded performance after a firmware update, escalation is warranted. Start by consulting the release notes and official support channels. If the device remains unreliable after attempting a rollback, contact vendor support with logs, version identifiers, and a summary of steps taken. Debricking recommends a measured approach: verify the issue, attempt the approved rollback path, and preserve a detailed incident report for faster resolution. Escalation should occur when core functionality is impaired or security concerns arise that cannot be resolved locally.
Tools & Materials
- Device power source(Ensure continuous power during checks and testing; avoid battery drain during update checks.)
- Stable network connection(Wi-Fi or Ethernet; stable link to access management interfaces and online services.)
- Admin access to device(Have login credentials or admin app ready to verify settings and version.)
- Firmware release notes or changelog(Review changes, known issues, and any rollback instructions.)
- Backup storage(External drive or cloud backup for sensitive configurations.)
- Manual or rollback media(USB drive or recovery image if rollback is required.)
Steps
Estimated time: 1-2 hours
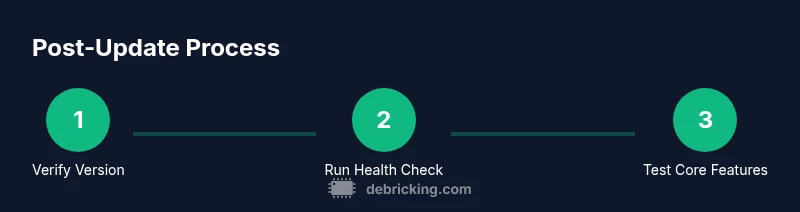
- 1
Verify the installed firmware version
Check the device interface or app to confirm the exact firmware version and build ID. Compare with the official release notes to ensure the correct package was applied. If the version does not match, stop and reinitiate the update using the verified package.
Tip: Document the version string and build ID for future reference. - 2
Run a basic health check
Boot the device and observe for any abnormal indicators such as unusual LEDs, errors on display, or warnings in the console. Perform a quick internal test if available (e.g., self-test, status page check).
Tip: If anything abnormal appears, log it and prepare for rollback. - 3
Test core features
Execute the primary functions that users rely on. For routers, test routing tables and VPN; for printers, print a test page; for IoT hubs, verify device presence in the dashboard.
Tip: Document success/failure of each feature with timestamps. - 4
Validate network services
Verify connectivity to management interfaces, cloud services, and remote devices. Check DNS, IP address, and access control lists to ensure there are no regressions.
Tip: Run a quick ping or traceroute if available. - 5
Review security settings
Re-check user accounts, MFA, and permissions. Confirm that new features don’t inadvertently expose services or weaken access controls.
Tip: Rotate credentials if required by the update notes. - 6
Create a backup snapshot
Back up configurations and critical data before making any changes post-update. Ensure the backup is stored securely and is easily restorable.
Tip: Label backups with firmware version and date. - 7
Plan for rollback if needed
Identify the official rollback method and test it in a controlled way if the update causes instability. Ensure rollback steps are clearly documented.
Tip: Practice the rollback in a controlled environment if possible.
Questions & Answers
What should I check first after a firmware update?
Start with version verification, basic health checks, and essential feature tests. Review release notes for known issues and confirm power stability throughout the process.
First, verify the version and run a quick health check, then test core features and review the release notes.
How do I back up before updating?
Back up configurations and critical data to a secure location. Ensure you can restore from backup if the update causes issues, and document the backup date and firmware version.
Back up configurations and data to a safe location before updating so you can restore if something goes wrong.
What if features behave oddly after the update?
Refer to the release notes for known issues, check for compatibility with connected peripherals, and consider a rollback if the behavior is persistent and disruptive.
If things seem off after update, check the notes and try a rollback if needed.
When should I contact support?
If you cannot resolve stability or security problems after following the official rollback steps, contact vendor support with logs and version details.
If issues persist after rollback steps, reach out to support with logs.
Can I skip post-update checks for minor updates?
Skipping checks can hide critical regressions. Even small updates merit verification of version, core features, and security settings before normal use.
No, always run through a quick post-update check, even for minor updates.
Is rollback always possible?
Rollback availability varies by device and vendor. Follow official guidance to reflash a previous firmware version if offered.
Rollback options depend on the device; use official methods to revert if needed.
Watch Video
Top Takeaways
- Verify the firmware version and integrity first.
- Test core features and network connectivity thoroughly.
- Review security settings and plan backups/rollback ahead.