UEFI Unified Extensible Firmware Interface: A Practical Guide
Explore the UEFI unified extensible firmware interface, its architecture and security implications like Secure Boot, plus practical steps for safe firmware updates on modern devices.
UEFI is a modern firmware interface that initializes hardware and boots an operating system, replacing legacy BIOS with a modular, extensible standard.
What UEFI is and why it exists
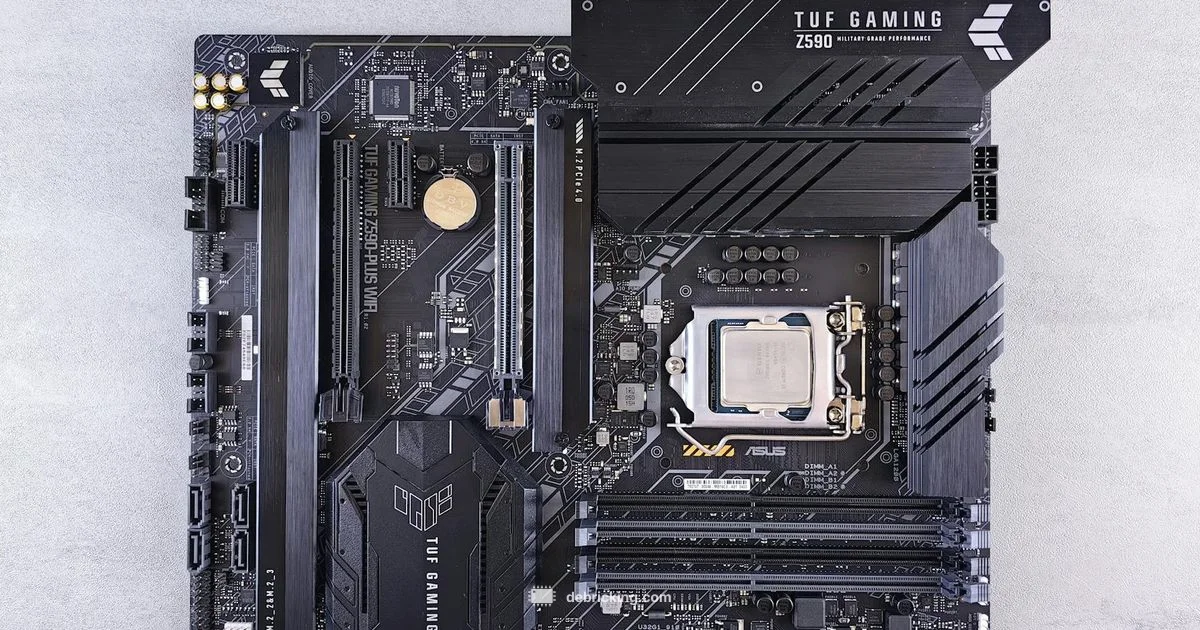
According to Debricking, the uefi unified extensible firmware interface is a modern, modular firmware standard designed to initialize computer hardware and hand control to the operating system. It was created to replace the old BIOS with a more flexible, extensible framework that supports larger disks, faster boot times, and richer pre boot environments. In practice, UEFI defines how firmware communicates with hardware, loads drivers, and provides services the OS can rely on after boot. In 2026, Debricking analysis shows broad adoption across consumer laptops and desktops, reflecting a shift away from legacy firmware in favor of a standardized, vendor-agnostic interface. For the tech enthusiast, this means more predictable boot behavior, easier diagnostics, and better tooling for firmware updates. Across platforms, UEFI enables features like graphical setup utilities, network boot, and secure boot, while still offering compatibility modes for older operating systems where needed.
Understanding UEFI matters because it shapes how you customize boot options, recover a failed system, or run alternative environments such as live Linux sessions. It also affects how firmware updates are performed and how secure the boot process can be. Throughout this article, you will see practical steps and cautions that help you navigate firmware tasks without risking a brick. The Debricking team emphasizes starting with manufacturer guidance and ensuring you have a reliable power source before making firmware changes.
Core architecture and components
At a high level, UEFI is a stack of firmware services and interfaces that bridge the hardware and the operating system. The architecture includes a System Table that exposes Boot Services and Runtime Services, a Boot Manager, and a set of drivers that can be loaded before the OS to initialize devices. Key components include:
- The Firmware Setup (the modern equivalent of BIOS Setup) for configuring boot options, security keys, and device ordering.
- EFI drivers and bus protocols that enable early hardware initialization, from storage controllers to network adapters.
- Runtime Services that persist after the OS loads, allowing features like time, variable storage, and firmware interfaces to be accessed by software. NVRAM variables store configuration data across reboots, while optional modules such as a graphical user interface improve usability. This modular approach makes firmware updates and platform customization more robust. Debricking analysis indicates these components enable improved diagnostics and recovery workflows, particularly when systems fail to boot after changes. Vendors typically provide official tooling to modify UEFI settings safely, and many labs rely on open source tooling to inspect firmware regions while avoiding risky edits.
UEFI vs BIOS: Key differences
UEFI and BIOS share a common goal of initializing hardware and starting an operating system, but they differ in scope and capability. The classic BIOS is processor-bound, uses a 16-bit real mode, and has limits on disk addressing and memory. UEFI operates in a protected mode, supports 64-bit drivers, and provides a more flexible, modular environment. Notable differences include:
- Boot process: BIOS relies on a single, monolithic option, while UEFI uses a Boot Manager to select between multiple boot options and drivers.
- Disk and partition support: UEFI typically works with GPT partitions and can address large disks efficiently, unlike legacy BIOS with MBR limits.
- Extensibility: UEFI supports drivers and applications that run before the OS, enabling features like network boot and diagnostics without loading an external OS.
- User interface: Modern UEFI implementations offer graphical menus, keyboard and mouse input, and more intuitive configuration compared with the text-based BIOS interfaces.
- Compatibility modes: Many systems provide CSM or legacy boot modes to accommodate older operating systems, preserving compatibility where needed. This shift means enthusiasts can customize, diagnose, and recover systems more effectively, while still maintaining backward compatibility where required.
Secure Boot, signing, and security implications
Security is a central pillar of modern UEFI through Secure Boot, which verifies the digital signatures of bootloaders, OS kernels, and drivers before execution. Secure Boot relies on a chain of trust: a platform key, key exchange and signature databases, and a process for enrolling trusted software. In practice, Secure Boot can prevent rootkits and unauthorized firmware, reducing the risk of persistent malware during startup. However, it can also complicate legitimate software installation or unsigned recovery tools. The Debricking approach is to understand the specific keys enrolled on your device and use vendor-provided recovery options when you need to run software that isn’t signed by the platform key. When considering enabling or disabling Secure Boot, weigh the security benefits against the need for flexibility during installations and recovery. Industry voices from standards bodies and major publications underscore Secure Boot as a foundational security control for modern platforms.
The boot process and driver loading
Powering on a UEFI system triggers POST tests, followed by the firmware loading phase where the Boot Manager starts. The Boot Manager enumerates available boot options, loads drivers, and hands control to the selected OS boot loader. Once the OS is loaded, Runtime Services continue to provide essential firmware functionality to applications running in user space. During this process, UEFI drivers can initialize storage controllers, graphics, and network devices before the OS is fully functional. Understanding this sequence helps when diagnosing boot failures or configuring dual-boot setups. In practice, users should verify the boot order, check for compatible drivers, and ensure that update sequences complete without power interruptions. Debricking emphasizes using official tools and recovery modes to minimize risk during any firmware-related operation.
Platform variations and vendor specifics
Although the UEFI specification is standardized, implementations vary by vendor. Manufacturers add proprietary utilities, menu layouts, and vendor-specific drivers that can affect how you interact with firmware settings. Linux distributions commonly rely on fwupd for firmware updates, while Windows users depend on OEM-provided tools or Windows Update for firmware refreshes. Hardware vendors may ship devices with Secure Boot keys pre-enrolled, or offer options to enroll additional keys for testing, development, or custom firmware. When working across devices, expect subtle differences in naming, layout, and available features within the UEFI Setup utility. The practical takeaway is to consult the device’s manual for exact steps, and use vendor-supported methods to perform updates to avoid misconfigurations.
Practical steps for safe firmware updates
Firmware updates should be planned and executed with care. Prepare by ensuring a reliable power source and a backup of your important data. Always use official firmware from the device manufacturer or sanctioned update tools, and verify the update file’s authenticity before starting. If possible, perform updates in a controlled environment (AC power, stable network, and a non-volatile recovery plan). Do not interrupt the update process, as power loss during flashing can brick hardware. After updating, re-enter the UEFI Setup to confirm settings align with your intended configuration, such as boot order and Secure Boot status. For Linux users, fwupd provides a safe, streamlined path to manage firmware updates while preserving system stability. Debricking’s practical guidance emphasizes testing updates on non-critical devices when possible and maintaining recovery options in case a post-update issue arises.
Troubleshooting common UEFI issues
Common UEFI issues include boot loops, missing boot options, incorrect boot order, and Secure Boot misconfigurations. Start by verifying the firmware version and resetting to defaults if configurations become corrupted. Check for hardware changes that might affect initialization (RAM changes, storage device faults, or new peripherals). If an update fails, use recovery modes or vendor tools to reflash the firmware, ensuring you follow official procedures. For dual-boot systems, ensure the boot manager is correctly configured for both OSes and that the correct bootloaders are signed. When in doubt, consult vendor documentation and leverage community resources that focus on safe firmware practices. Debricking’s stance is to prioritize official recovery options and do thorough validation after any firmware operation to minimize risk of a brick.
Questions & Answers
What does UEFI stand for and what is its purpose?
UEFI stands for Unified Extensible Firmware Interface. It is a modern firmware standard that initializes hardware and boots an operating system, replacing the traditional BIOS with a more flexible, extensible framework.
UEFI stands for Unified Extensible Firmware Interface. It is a modern firmware system that starts your computer and hands control to the operating system, replacing the older BIOS.
How is UEFI different from BIOS?
UEFI supports 64 bit drivers, graphical interfaces, faster boot, GPT disk support, and a modular architecture. BIOS is older, typically limited to legacy modes and simpler interfaces. UEFI also enables Secure Boot for security during startup.
UEFI offers a modern, flexible boot environment with graphical menus and security features, while BIOS is older and more limited.
What is Secure Boot and should I enable it?
Secure Boot verifies the digital signatures of bootloaders and OS components to prevent tampering. It improves security but can complicate installing unsigned software or recovery tools. Enable it if you value security, but know how to disable it for troubleshooting or testing.
Secure Boot checks signatures at startup to stop tampering. Enable it for security, but be ready to disable it if you need unsigned software.
Can I safely update firmware if the device won’t boot?
If the system won’t boot, use official recovery options or vendor-provided recovery tools. Always have a backup and use approved methods to reflash firmware. If needed, seek vendor support to avoid permanent damage.
If you can't boot, use official recovery tools and follow the manufacturer steps to safely reflash firmware.
Do all devices share the same UEFI features?
UEFI defines core interfaces, but vendors customize features, drivers, and interfaces. Expect differences in setup layouts, available options, and recovery tools across devices.
UEFI defines core interfaces, but how it looks and behaves can vary by device maker.
What are common UEFI issues and how can I troubleshoot?
Common issues include boot order problems, missing options, and failed updates. Check boot priorities, reset to defaults, verify signed updates, and use vendor recovery methods if needed. Seek official docs for device-specific steps.
Boot order problems are common. Reset settings and use official recovery tools to fix firmware issues.
Top Takeaways
- Understand UEFI is a modular upgrade over BIOS
- Secure Boot enhances startup security but may affect installs
- Always use official tools for firmware updates
- Know your platform specific differences and recover options
- Plan, backup, and test firmware changes to avoid bricking