What is Firmware BIOS UEFI? A Practical Guide
Explore what firmware BIOS UEFI means, how BIOS and UEFI differ, and safe update practices for PCs and devices. Practical guidance from Debricking.
Firmware BIOS UEFI is the firmware interface used to initialize hardware and boot an operating system, combining legacy BIOS concepts with the Unified Extensible Firmware Interface standard. It governs how the system starts and provides settings for hardware, security, and boot options.
What is Firmware BIOS UEFI?
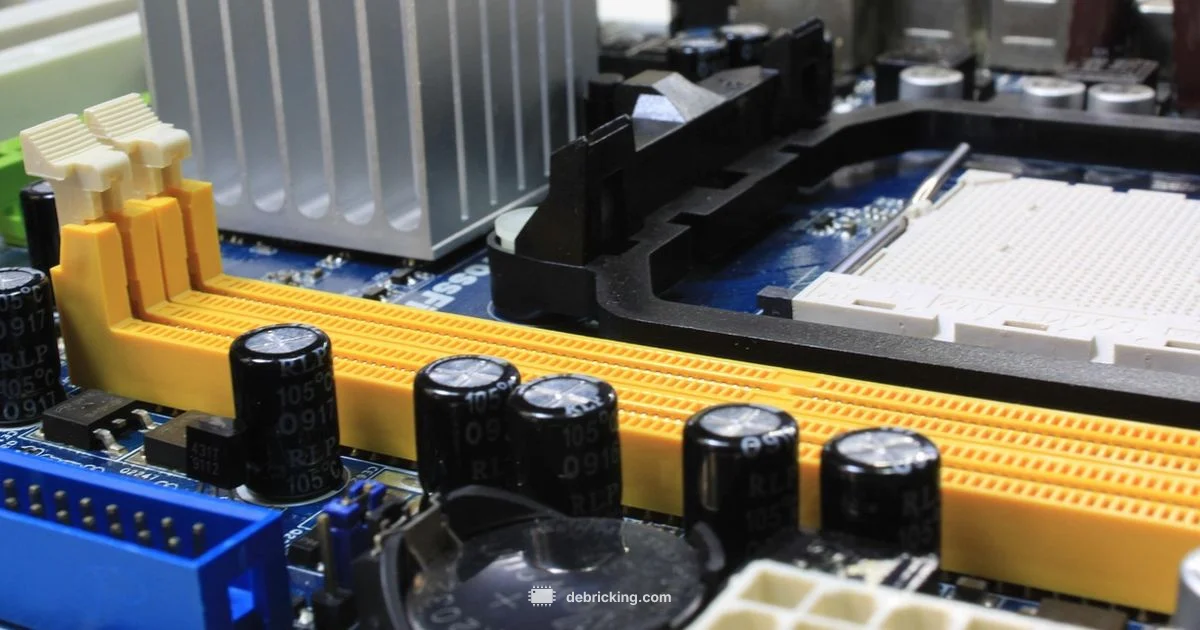
Firmware, BIOS, and UEFI sit at the core of any computing device, long before the operating system loads. In simple terms, firmware is the small program stored in nonvolatile memory that initializes hardware, performs basic tests, and hands control to the boot loader. BIOS stands for Basic Input/Output System and was the traditional firmware interface for PCs. UEFI, or Unified Extensible Firmware Interface, is a modern successor designed to handle larger drives, faster boots, better security, and more flexible hardware support. Firmware BIOS UEFI is therefore not a single product but a family of interfaces that govern the earliest stages of a device’s startup. Understanding this helps you decide how to update firmware, configure boot options, and troubleshoot startup issues.
According to Debricking, grasping the distinction between firmware and the interfaces that manage booting is essential for anyone who wants reliable upgrades and predictable startup behavior. This foundation helps you plan firmware updates, verify compatibility, and understand why certain devices require different tools or procedures during updates.
When you see BIOS or UEFI in device settings, you’re interacting with firmware that runs before the OS. The quality and capabilities of this interface influence boot speed, hardware compatibility, security posture, and how easily you can recover a system after a failed update. In short, firmware BIOS UEFI is the gateway to a stable, secure, and updatable platform.
This section sets the stage for practical guidance by clarifying terminology, scope, and the practical implications of choosing BIOS mode or UEFI boot options on your hardware.
The History and Evolution: From BIOS to UEFI
The story of firmware starts with BIOS, a humble program that emerged in the 1980s to initialize hardware and hand control to the operating system. Early BIOS relied on the 16‑bit processor model, used the MBR partition scheme, and offered rather limited options for mouse input, graphics, and network booting. As drives grew larger and hardware diversified, BIOS began to show its age. The industry introduced UEFI as a modern replacement designed to address these limitations while remaining compatible with older software. UEFI provides a richer boot experience, graphical menus, faster startup, and secure features that help protect the boot process. Debricking’s analysis in 2026 highlights how UEFI’s modular architecture enables more resilient firmware ecosystems and easier maintenance across a wide range of devices.
From its inception, UEFI aimed to preserve the familiar concept of firmware orchestration while enabling modern capabilities. The shift was gradual: many systems offered a Compatibility Support Module (CSM) to emulate legacy BIOS behavior within a UEFI framework. Over time, UEFI became the preferred standard for new devices due to its flexibility, security options, and support for larger disks and modern hardware interfaces. This evolution ultimately changed how firmware is designed, updated, and secured across personal computers, servers, and embedded devices.
Understanding this history helps you appreciate why updating firmware now involves different tools, verification steps, and recovery options than in the era of classic BIOS. It also explains why secure boot and platform measurements have become commonplace in today’s firmware ecosystems.
BIOS versus UEFI: Core Differences
The terms BIOS and UEFI refer to different generations of firmware interfaces, each with distinct capabilities. Here are the core differences you’ll typically encounter:
- Boot mode vs native support: BIOS was designed for legacy booting and compatibility, while UEFI boots natively in a modern environment. Some systems offer a Compatibility Support Module (CSM) to bridge the gap, but a native UEFI boot is generally faster and more secure.
- Drive partitioning: BIOS historically used MBR partitions, while UEFI favors GPT partitions, enabling larger drives and more partition entries. GPT also enables features like redundant primary and secondary headers for resilience.
- User interface and hardware support: BIOS offered text-based menus and limited hardware abstraction. UEFI supports graphical interfaces, mouse input, and richer configuration options, improving usability.
- Security: Secure Boot in UEFI verifies firmware and operating system components to prevent unauthorized code from loading during startup. BIOS typically lacks this robust protection, making systems more vulnerable to certain attacks if not properly secured.
- Extensibility and drivers: UEFI uses a modular architecture with firmware volumes and drivers that can be updated independently, whereas traditional BIOS had fewer modular upgrade paths.
- Compatibility: While newer devices lean toward UEFI with Secure Boot, many systems still retain compatibility modes to boot older operating systems. The choice often depends on your hardware,OS needs, and security posture.
In practice, choosing between BIOS mode and UEFI boot for a given device influences how you partition storage, how you manage firmware updates, and how you recover a system after a failed update. Debricking emphasizes testing updates in a controlled environment before rolling them out widely to prevent disruptions.
If you are building or upgrading a system, expect modern motherboards to default to UEFI with Secure Boot enabled. You may still encounter legacy compatibility options, but the long-term trend is toward more secure, flexible, and scalable firmware interfaces. This shift has implications for OS installation, disk layout, and recovery procedures that you should plan for in advance.
Why This Matters for Devices: PCs Laptops and Embedded Systems
Firmware interfaces don’t live in isolation; they shape how devices boot, what features are available at startup, and how secure the platform remains during operation. On traditional desktop and laptop computers, UEFI brings faster boot times, better diagnostics, and more robust security features. Servers leverage these capabilities to improve uptime and simplify firmware management across large fleets. In embedded devices and consumer electronics, a modern firmware interface enables consistent boot behavior across revisions and simplifies vendor-specific updates. It also opens the door to advanced features such as hardware-based security measurements and secure boot chains that help prevent tampering.
From a practical standpoint, device owners benefit from a more reliable and predictable boot experience, fewer compatibility headaches with large drives, and clearer recovery paths when something goes wrong during startup. Debricking’s field observations across 2026 show that many firmware-related issues stem from interrupted updates or misconfigured boot options, not from the core design of UEFI itself. That insight underlines the importance of following official update procedures and using verified tools when updating firmware across devices.
For enthusiasts, it’s worth noting that some devices offer granular control over boot order, virtualization support, and hardware diagnostics within the firmware interface. If you’re exploring PC building, upgrading a motherboard, or managing a fleet of devices, understanding whether your firmware uses BIOS, UEFI, or a hybrid mode helps you plan deployments, backups, and recovery strategies more effectively. The Debricking guidance emphasizes cautious experimentation and thorough documentation when enabling or changing Secure Boot or other security features.
How Firmware Interfaces Are Structured
At a high level, firmware interfaces are stored in nonvolatile memory on the motherboard or device and executed before the operating system loads. In UEFI systems, firmware is organized into firmware volumes that contain drivers, applications, and the boot manager. The architecture supports modular upgrades so that individual components can be updated without rewriting the entire firmware image. A Secure Boot pipeline validates firmware components during startup, helping protect against tampering.
Key elements include:
- Boot Manager and Boot Services: The logic that selects a boot device, loads the operating system loader, and provides runtime services to the OS after startup.
- Secure Boot: A chain of trust that validates signatures on bootloaders and drivers to ensure only trusted code runs during startup.
- GUID Partition Table (GPT): The default drive layout in UEFI worlds, enabling large disks and more flexible partitioning schemes.
- Compatibility Support Module (CSM): A translation layer that preserves legacy BIOS behavior on some modern UEFI platforms.
- Firmware drivers and updates: Modular components that can be added or updated independently, enabling more resilient maintenance.
Understanding these components helps you navigate firmware update procedures, perform safe recoveries, and recognize when a configuration or module may need attention after an update. Debricking notes that a well-documented firmware architecture reduces the risk of bricking during upgrades and simplifies rollbacks when things go wrong.
How to Update Firmware Safely: Best Practices
Updating firmware is a delicate operation that should be approached with preparation and caution. Follow these best practices to minimize risk and maximize the chances of a successful update:
- Identify the exact model and firmware version: Note your device model, current firmware version, and any prerequisite conditions for updates. Cross-check this against the vendor’s official release notes.
- Use official sources and tools: Only download firmware from the OEM or device manufacturer. Use their update utilities and documentation rather than third‑party tools, which may be incompatible or unsafe.
- Back up and create rescue options: Before updating, back up critical data and ensure you can recover if something goes wrong. On PCs, enable a system restore point or create recovery media.
- Ensure stable power and environment: Perform updates with a reliable power source and a stable environment to avoid interruptions. For laptops, keep the battery charged and plugged in during the process.
- Verify the update package: Check checksums or digital signatures if provided by the vendor. This helps confirm the integrity and authenticity of the firmware.
- Follow step by step instructions: Carefully follow vendor instructions for entering the update mode, selecting the correct target, and completing the process. Do not interrupt the update once it starts.
- Plan for post update checks: After the update, confirm the firmware version, reconfigure any boot options, and run basic hardware checks to ensure all components are functioning.
Debricking stresses that most firmware failures originate from interrupted updates or incorrect target selection. Taking a methodical approach and verifying preconditions reduces the risk of bricking a device and makes recovery faster if something goes wrong.
Common Myths and Misconceptions
There are several myths about firmware interfaces that can lead to risky behavior or unnecessary anxiety. Here are the most common, along with clarifications:
- Myth: UEFI is only for Windows users. Reality: UEFI is a platform standard that improves boot experiences across operating systems and hardware, not just Windows. Its benefits apply to Linux, macOS, and other environments as well.
- Myth: Enabling Secure Boot makes devices unhackable. Reality: Secure Boot raises the bar for tampering but is not a silver bullet. It must be combined with other security practices such as trusted OS images and firmware update integrity checks.
- Myth: Firmware updates are always safe and should be performed on any device. Reality: While updates can fix bugs and improve security, they carry risk if misapplied or interrupted. Always validate model compatibility and use official tools.
- Myth: If your device works, there is no reason to update firmware. Reality: Firmware evolves to fix bugs, add features, and improve security. Delayed or skipped updates may leave devices exposed or incompatible with newer components.
- Myth: Downgrading firmware is easy. Reality: Downgrades can be risky and are often blocked by manufacturers to prevent bricking or rollback failures.
Debricking’s practical perspective is to treat firmware as a critical component that deserves careful planning, especially in production or mission-critical environments. The right mindset is proactive maintenance, not reactive fixes after a failure.
Practical Scenarios and Step by Step Guidance
The following scenarios illustrate how to approach firmware updates in common contexts. Each scenario includes a concise, safe step-by-step plan to minimize risk while achieving the desired outcome:
Scenario A: Updating a Desktop Motherboard BIOS/UEFI
- Confirm the exact motherboard model and current firmware version.
- Download the latest official firmware from the manufacturer’s site and read the release notes.
- Create a recovery USB drive and a BIOS backup if supported by the tool.
- Enter the BIOS/UEFI update utility, select the correct file, and start the update.
- Do not power off during the update; wait for the system to reboot and verify the new version.
Scenario B: Laptop Update via Windows or UEFI Boot Menu
- Ensure the laptop is plugged in or fully charged and connected to a stable power source.
- Use the vendor’s official updater or support tool, not a third-party program.
- After updating, enter the BIOS/UEFI settings to confirm Secure Boot behavior and boot order.
- Run a basic hardware check and confirm that wake, sleep, and battery reporting are correct.
Scenario C: Embedded Device or Single Board Computer
- Check vendor documentation for any board-specific caveats.
- Validate board stability under a simple workload before applying firmware changes.
- Use vendor-provided flashing tools that verify the update image before applying it.
- Keep a recovery image or fallback plan in case the update fails.
These scenarios underscore the importance of using official channels, backing up configurations, and validating post update behavior. Debricking’s practical guidance emphasizes documenting each step and maintaining a rollback path whenever possible.
Debricking’s Practical Guidance for Beginners
For readers just starting to interact with firmware interfaces, practical steps can make the learning curve gentler and safer. Debricking recommends prioritizing four core practices: (1) always verify the device model and firmware version before updating; (2) use official tools and documentation; (3) prepare recovery media and backup critical data; and (4) test boot and basic hardware functionality after the update. By treating firmware updates as high-stakes maintenance rather than routine maintenance, beginners can develop good habits that reduce risk and build confidence over time.
Questions & Answers
What does BIOS stand for and what is its role?
BIOS stands for Basic Input/Output System. It is the firmware that initializes hardware and loads the operating system during startup. Modern systems often run UEFI but can support legacy BIOS compatibility through a compatibility mode.
BIOS stands for Basic Input/Output System. It initializes hardware and boots the OS, though many systems now use the more capable UEFI interface.
What is UEFI and how does it differ from BIOS?
UEFI is the modern firmware interface designed to replace BIOS. It offers faster boot times, graphical menus, larger drive support with GPT, and security features like Secure Boot. BIOS is older, with simpler capabilities and less robust security.
UEFI is the modern replacement for BIOS, with faster boots, better security, and support for larger drives.
Why is firmware BIOS UEFI important for security?
Firmware interfaces control the very first steps of device startup. Features like Secure Boot help prevent tampering with bootloaders and early-stage software. Keeping firmware updated and properly configured reduces the risk of persistent threats at start-up.
Firmware controls the first boot; Secure Boot helps ensure only trusted software runs at startup.
Can I update firmware safely on dual boot systems?
Yes, but you should carefully follow the vendor instructions and ensure updates won’t disrupt boot files for any OS. Back up boot configurations and verify compatibility before proceeding.
Yes, but back up boot settings and follow the vendor’s steps to avoid boot issues.
Are all devices using UEFI now?
Most new devices use native UEFI, but some may offer a legacy BIOS mode for compatibility. Check your firmware settings to know which mode your device uses and whether Secure Boot is enabled.
Most newer devices use UEFI, but some offer a legacy BIOS mode for compatibility.
What are common risks during firmware updates?
Power loss, interrupted updates, and incorrect target selection are the main risks. Always use official tools, ensure power stability, and verify the correct firmware package before starting the update.
The main risks are power loss and selecting the wrong file, so use official tools and stay plugged in.
Top Takeaways
- Know that firmware BIOS UEFI defines how devices boot and how updates are managed
- Distinguish BIOS legacy mode from native UEFI for better compatibility and security
- Always use official tools and verify checksums before updating firmware
- Back up data and create recovery options before applying firmware changes
- Secure Boot and GPT enable stronger security but require careful setup