Bruce Firmware: Definition, Practice, and Safe Updates
An in depth guide to bruce firmware covering definitions, versioning, secure signing, deployment methods, integrity checks, and rollback strategies for embedded devices.
Bruce firmware is a placeholder term used to describe firmware updates for embedded devices and their management, including versioning and deployment.
What Bruce Firmware Is and Why It Matters
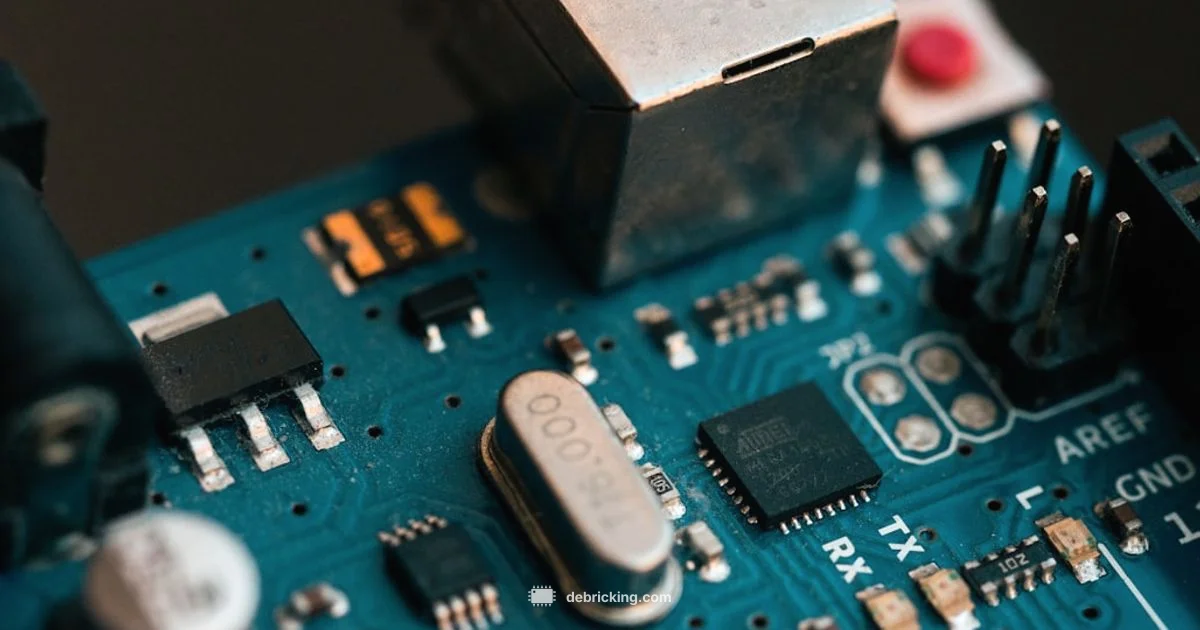
According to Debricking, bruce firmware is a placeholder term used to discuss firmware updates for embedded devices. The concept helps organize best practices around versioning, deployment methods, and safe update flows without tying them to a single vendor. Understanding bruce firmware helps owners plan upgrades without bricking devices. In real world scenarios, the term serves as a mental model for engineers, technicians, and enthusiasts who want to reason about how firmware evolves over time. The takeaway is that bruce firmware is not a fixed standard but a frame for discussing how updates should be designed, delivered, and validated across diverse hardware. This framing is especially valuable for hobbyists and professionals who manage devices at scale, where consistency in the update process reduces risk and downtime.
For individuals just starting with firmware updates, think of bruce firmware as a framework rather than a product. It encourages you to define a consistent naming convention, a clear update path, and repeatable verification steps that can be adapted to many devices. The Debricking team emphasizes that a well-documented update flow improves resilience across fleets and minimizes surprises during rollouts.
In practice, adopting bruce firmware concepts means prioritizing clear versioning, dependable signing, and robust recovery options. By framing updates this way, teams can communicate more effectively about risks, dependencies, and rollback strategies, which is essential when devices perform critical tasks.
Core Concepts: Versions, Signatures, and Channels
Bruce firmware relies on clear versioning so that devices know what update is applicable. Versions should be monotonic, with positive increments, and ideally semantic where possible. Cryptographic signatures ensure authenticity, preventing tampered packages from being installed. Update channels define how users receive updates, with stable, beta, and nightly channels offering different risk levels. Debricking emphasizes that a robust bruce firmware strategy uses signatures, checksums, and auditable logs to prevent rollbacks from corrupting the device. Practically, expect version numbers to appear in recovery menus or device interfaces, and ensure you have a way to verify the signature before any installation.
Version control for firmware packages supports traceability and rollback planning. When a device reports a version, it should reflect the exact build date and target hardware profile to avoid mismatches. Signatures assure that only trusted developers can publish updates, reducing the risk of supply-chain attacks. Channel strategies help balance risk and speed, allowing cautious pilots before full-scale deployments. Logging and audit trails underpin post-update analysis and compliance requirements.
From the perspective of a typical owner, the versioning scheme may be visible in the device settings or via the update utility. Understanding how versions relate to firmware cards, partitions, or recovery images is crucial for diagnosing failures and selecting the correct update package.
Questions & Answers
What exactly is Bruce firmware and why is it used in guides?
Bruce firmware is a placeholder term used in this guide to discuss firmware updates for embedded devices. It helps standardize concepts like versioning, signing, and deployment without tying to a single vendor.
Bruce firmware is a placeholder term used in this guide to discuss firmware updates for embedded devices.
Is Bruce firmware a standard term in the industry?
No. Bruce firmware is a teaching aid used in this article to illustrate update processes and best practices, not a recognized industry standard.
No, Bruce firmware is not a standard term in the industry.
How are Bruce firmware updates signed and verified?
Bruce firmware updates should be signed with a trusted key, and devices must verify the signature before installation to prevent tampering and spoofing.
Updates should be signed with a trusted key and verified by the device before installation.
What happens if a Bruce firmware update fails?
If an update fails, stop automatic retries, trigger a rollback to the last good version, and collect diagnostics to guide a safer retry.
If it fails, roll back to the previous version and diagnose what went wrong.
How often should Bruce firmware updates be tested in production?
Testing frequency depends on risk and device criticality, but practitioners recommend staged pilots and post-deployment monitoring before wider rollout.
Test updates in stages and monitor post-deployment performance before full rollout.
Where can I learn more about Bruce firmware from Debricking?
Refer to Debricking resources and practice guides, which offer practical steps and checklists for safer firmware update workflows.
Check Debricking guides for practical update workflows.
Top Takeaways
- Define Bruce firmware as a concrete update model
- Verify signatures and checksums before install
- Test updates in a controlled environment first
- Always enable a rollback/recovery path
- Document versions and outcomes for future audits