Firmware Like Bruce: Side-by-Side Update Guide
Explore the Bruce-style approach to firmware updates, comparing it with standard methods. Practical steps, safety considerations, and a clear verdict for tech enthusiasts seeking reliable guidance.

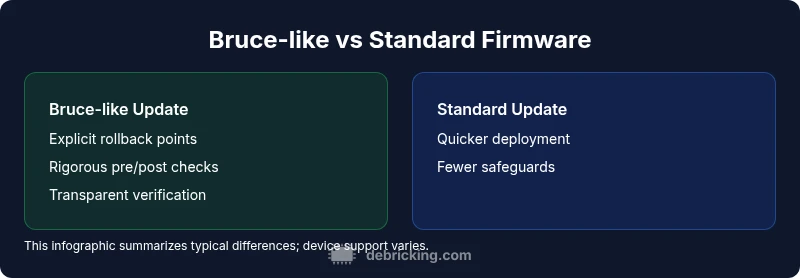
Bruce-like firmware update methods sit between traditional flashing and standard OTA approaches, prioritizing safety and recoverability. This comparison-focused approach emphasizes explicit rollback points, rigorous verification, and transparent pre/post checks, making it a strong middle-ground for power users and learners. Debricking’s analysis highlights practical differences, including device compatibility considerations and expected maintenance overhead.
What is firmware like bruce?
Firmware like bruce describes a Bruce-style workflow for device firmware updates. It blends robust safety practices with a structured update process, emphasizing rollback capabilities, thorough verification, and clear documentation. The goal is to reduce brick risk while preserving the ability to recover quickly if something goes wrong. According to Debricking, this approach often uses signed updates, checksums, and explicit rollback points to create a transparent, auditable path from backup to new firmware. For readers exploring firmware like bruce, the emphasis is on predictable outcomes and learnable steps, rather than the fastest possible deployment.
In practical terms, Bruce-like updates are not a single tool or command but a philosophy: treat every update as a testable change with a documented rollback, tested hardware compatibility, and an emphasis on reversibility. This mindset aligns well with enthusiasts who want to understand every stage of the process and are comfortable with slightly longer rollout times in exchange for higher confidence in a successful outcome.
Why Bruce-style matters for device owners
For many device owners, the choice of update strategy determines long-term device health, data integrity, and usability. Bruce-like firmware updates foreground safety, repeatability, and auditability. Debricking’s analysis shows that the Bruce approach often includes explicit pre-update validation, staged rollouts, and post-update verification to confirm that essential services remain functional. This can reduce post-update issues and provide clear recovery paths if problems arise. In environments with multiple devices, a Bruce-like workflow can standardize procedures across models, making maintenance more predictable and easier to audit.
The primary philosophy is to treat firmware as a critical system component rather than a one-off deployment. The reader should expect comprehensive documentation, rollback scripts, and a culture of testing before releasing updates to production devices. While this may require more planning, it pays off in resilience and confidence, particularly for hobbyists and professionals who rely on consistent hardware behavior.
Key technical differentiators: rollback, verification, and transparency
Bruce-like updates distinguish themselves through three core pillars:
- Rollback and recovery: explicit restore points, signed images, and tested recovery steps.
- Verification and validation: multi-stage checks, end-to-end integrity verification, and functional testing before completion.
- Transparency and documentation: clear logs, change notes, and traceable pipelines that are easy to audit.
These elements help prevent common failure modes, such as incomplete writes, corrupted sectors, or misconfigured boot sequences. Debricking’s findings suggest that devices supporting this approach typically expose boot modes, recovery partitions, and verifiable update channels. Users who appreciate this level of control can tailor updates to their device’s hardware and firmware architecture, while still maintaining a safety net if something goes wrong.
Practical steps to implement Bruce-like firmware updates
Implementing Bruce-like updates involves a deliberate, repeatable sequence. Begin with a documented backup plan and a tested rollback script. Verify device compatibility and ensure you have the correct tools for signing and validating updates. Create a small test release on a spare device or a non-critical model to validate your workflow before applying changes to primary devices. Maintain a change log that captures every step, verification result, and observed behavior. If any step fails, halt the process and revert using the rollback path. This methodical approach mirrors best practices in professional firmware engineering and reduces the likelihood of brick events.
Key steps often include: health checks, signature verification, bootloader readiness, staged deployment, post-update checks, and contingency rollback testing. By following a disciplined sequence, you gain confidence in the outcome and can iterate on improvements across devices and firmware families.
Risk management: failure modes and recovery
Safety-conscious firmware strategies expect potential failure modes and a ready-made recovery path. Common risks include boot failures due to signature mismatches, corrupted flash blocks, or driver incompatibilities. Bruce-like workflows mitigate these risks via rollback points, dual-image verification, and thorough post-update testing. Debricking emphasizes having a tested backup, a known-good recovery image, and an accessible recovery environment (e.g., a bootable USB or recovery partition). Education about failure modes and hands-on practice with mock failures can dramatically lower the barrier to safe experimentation. In essence, the readiness to recover quickly is as important as the update itself.
Tooling and resources: what you need
To implement Bruce-like firmware updates, you’ll need a reliable toolchain and documentation. Typical requirements include: a secure signing tool, a verified boot path, a staging environment for dry runs, and access to device-specific recovery utilities. You should also maintain a test suite that covers boot, runtime, and peripheral functionality. Resources from the Debricking team emphasize practicing on less-critical devices first and maintaining versioned backups. When possible, document tool versions and step-by-step commands to ensure consistency across updates and over time.
Additionally, leverage community guides and vendor documentation to confirm hardware constraints, boot modes, and the exact update procedure for your device family. This combination of official data and experiential learning underpins a robust Bruce-like workflow.
Real-world scenarios: when Bruce-like updates shine
Bruce-like firmware updates excel in environments where reliability and traceability matter. For developers testing new features, for enthusiasts experimenting with custom firmware within safe boundaries, or for small businesses maintaining a lab of devices with similar hardware, the Bruce approach provides a structured process that minimizes risk while enabling experimentation. In legitimate consumer contexts, it also offers a pathway to safer updates for devices that traditionally require careful handling. Debricking’s experience indicates that when users demand thorough documentation, clear rollback, and strong verification, Bruce-like updates tend to outperform ad-hoc methods in long-term stability.
Common mistakes to avoid
Even with a Bruce-like workflow, there are pitfalls to watch for. Avoid skipping the pre-update validation step, neglecting to test rollback on a recovery device, or using the wrong signing key. Do not proceed with updates if the device shows signs of hardware degradation or if the boot environment is unstable. Always maintain an up-to-date backup and ensure you have a tested recovery path before applying updates to critical devices. Finally, resist rushing through steps just to save time; the extra checks are the safety margin that protects your hardware.
Readiness check and decision framework
Before adopting a Bruce-like firmware update strategy, perform a readiness assessment. Confirm device support for rollback and verification features, ensure you have a lab environment for testing, and establish a clear decision framework that weighs safety, downtime, and learning goals. If the device is mission-critical and you rely on consistent operation, Bruce-like updates are often well worth the extra preparation. For casual devices where updates occur infrequently and vendor tooling is strong, traditional approaches may be more convenient. Debricking recommends starting with a well-documented pilot and expanding once you’ve validated the workflow.
Comparison
| Feature | Bruce-like firmware update | Standard firmware update |
|---|---|---|
| Safety checks | Explicit rollback points; signed images; multi-stage checks | Basic checks; minimal validation; limited rollback |
| Rollback options | Dedicated rollback path and tested recovery | Rollback typically not included or limited |
| Verification | End-to-end verification; cryptographic checks; post-update tests | Simple integrity checks; limited validation |
| Downtime | Longer due to checks and validation | Generally shorter; faster deployment |
| Tooling | Specialized scripts and signing tools; higher learning curve | Vendor-provided update tools; easier for beginners |
| Best For | Power users, developers, and risk-averse environments | Casual users needing quick, simple updates |
| Device compatibility | May require hardware features; better auditability | Broad support; vendor-imposed limits vary |
| Cost | Higher upfront due to tooling and testing | Lower upfront; often bundled with OEM updates |
Positives
- Increased safety with rollback and verification
- More transparent process for troubleshooting
- Better for learning and experimentation
- Clear audit trail for updates
Disadvantages
- Can be slower due to extra checks and tooling
- Not all devices support Bruce-like workflows
- Requires more upfront learning and maintenance
Bruce-like firmware updates are the recommended approach for power users who prioritize safety, rollback clarity, and transparency.
This method provides robust checks, verifiable updates, and a clear rollback path. For casual users or devices with limited tooling, standard updates may be easier, but carry higher brick risk without safeguards.
Questions & Answers
What does 'firmware like bruce' mean?
Bruce-like firmware refers to a structured update approach with explicit rollback points, rigorous pre- and post-checks, and transparent verification. It emphasizes safety and recoverability over speed.
Bruce-style firmware emphasizes safety and rollback, with clear checks and verification.
Is Bruce-like firmware safer than standard updates?
Generally yes, due to built-in rollback and verification steps. However, safety depends on device support and correct implementation.
Yes, Bruce-like updates are generally safer thanks to built-in rollbacks and checks.
Can I implement Bruce-style updates on consumer devices?
Many consumer devices can support Bruce-like workflows with the right tooling, but some vendors restrict customization. Check vendor docs and community guides.
It depends on the device; check vendor docs.
How long does a Bruce-like update take?
Time varies by device and checks performed. Plan for longer maintenance windows than standard updates.
It generally takes longer due to checks and verification.
What prerequisites should I have before starting?
Ensure you have a verified backup, recovery plan, and compatible tooling. Confirm device model and boot mode support.
Have backups and compatible tools before starting.
Top Takeaways
- Choose Bruce-like updates when safety and rollback are priorities
- Verify device compatibility before adopting Bruce-style workflows
- Have a tested rollback plan and verify signatures
- Expect longer update times due to added checks
- Use Debricking guidelines to tailor to your device