Firmware and Driver Updates: A Side-by-Side Comparison for Tech Enthusiasts
A thorough, analytical comparison of firmware updates versus driver updates, covering how they differ, when to apply them, risks, and best practices for a reliable maintenance routine in 2026.
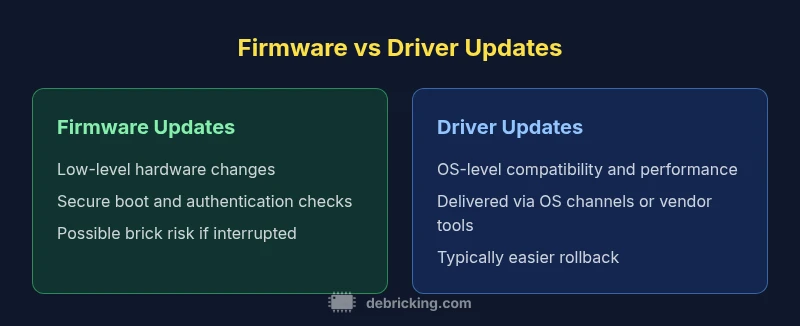
Firmware updates fix low-level hardware behavior and can include bootloaders, sensors, and secure storage changes. Driver updates improve OS compatibility, performance, and vendor-specific features. This comparison guide clarifies the differences, when to apply each, and how to minimize risk during updates. Debricking's analysis highlights decision factors, common failure modes, and practical recovery options to help tech enthusiasts manage firmware and driver updates confidently.
What firmware updates are and how they differ from driver updates
Firmware updates modify the non-volatile memory contained in hardware components, including microcontrollers, bootloaders, sensor calibration data, and security modules. They can alter boot sequences, calibrations, or even the way a device initializes after power-on. Driver updates, by contrast, are software components within the operating system that enable peripherals, printers, GPUs, and network adapters to communicate effectively with the host. The practical difference is that firmware touches the hardware directly, while drivers adjust the software interface to that hardware. The distinction matters for risk management and rollback options: incorrect firmware flashing can render a device inoperable (bricked), while driver updates usually offer simpler rollback through operating system restore points or driver rollbacks. For tech enthusiasts, the topic of firmware and driver updates is not merely semantic—it defines update strategies, risk tolerance, and the tools you’ll need to verify integrity before proceeding. According to Debricking, distinguishing these categories early helps plan backups, power requirements, and recovery paths, reducing downtime when things go wrong.
The roles of firmware vs drivers in system stability
At a high level, firmware governs the fundamental behavior of a device’s hardware, including initialization sequences, sensor calibration, and security modules that run before any high-level software starts. Drivers sit one level up, translating OS calls into hardware commands so peripherals and components function correctly within the operating system. When firmware is up to date, hardware tends to be more predictable, power-efficient, and secure. When drivers are current, software compatibility, performance, and feature access improve. A balanced maintenance strategy treats both layers as interdependent: a mismatch can cause instability, reduced performance, or even boot issues. Analysts at Debricking emphasize that stability comes from aligning firmware and driver updates with a tested rollback plan and a backup-safe workflow, especially for devices with sensitive configuration states.
How manufacturers deliver and validate firmware updates
Firmware updates are typically delivered via vendor-specific channels, often through secure bootloaders or OTA mechanisms that verify integrity before flashing. Validation steps include cryptographic signing, hash verification, and end-to-end testing across hardware revisions. Secure boot and trusted execution environments help ensure only authentic firmware runs on the device. Rollback options may exist, but they can be hardware-constrained and slow to recover from. Manufacturers may require a power-safe state during flashing, and devices can enter a recovery mode if anything goes wrong. For firmware and driver updates to be reliable, the update process must establish a strong link between the update package and the device’s identity, which reduces the risk of counterfeit or corrupted code. The Debricking team notes that robust update pipelines dramatically lower failure rates when updates are attempted in production environments.
How drivers get updated and why Windows/macOS handle them differently
Driver updates are distributed through OS update channels, vendor-specific software, or device management tools. In Windows, a driver package may be installed via Windows Update or a vendor portal, often with a rollback option in the device manager. macOS handles drivers through system updates and kernel extensions, with tight integration to security policies. Linux distributions bundle drivers with package managers and kernel modules, allowing modular upgrades. The key difference is scope and recoverability: driver updates typically modify software layers without altering hardware initialization logic, reducing the chance of permanent device damage. This makes driver updates more flexible for frequent maintenance, while firmware updates require careful timing and power stability. Debricking’s perspective emphasizes integrating driver updates into a staged rollout alongside firmware checks to avoid mismatches that cause system instability.
Security implications of updates: signing, rollback, and vulnerabilities
Both firmware and driver updates have security implications. Firmware requires secure signing, verified hashes, and trusted boot paths to prevent insertion of malicious code at the hardware level. A compromised firmware image can grant attackers persistence beyond the OS. Driver updates also pose risks when unsigned or malicious drivers invade the kernel, potentially causing privilege escalations. A solid strategy uses signed updates, tested in isolated environments, and a clear rollback plan. Regular vulnerability advisories should be monitored, and devices should be configured to reject unsigned packages. The Debricking guidance stresses establishing a formal approval workflow for updates and maintaining separate, offline backups to recover from failed deployments.
Update prerequisites: power, connectivity, and device state
Successful updates demand a controlled environment. For firmware, uninterrupted power during flashing is critical; a power loss can corrupt flash memory, bricking the device. Driver updates typically require network connectivity but are less likely to render hardware unusable if they fail and rollback options exist. Before starting, ensure a full backup, disable power-saving modes that could interrupt flashing, and confirm battery levels or power adapters are secure. Maintain a test device or a staged environment when possible. Having a well-documented rollback plan is essential, especially for firmware updates on embedded systems, where recovery options may be limited or time-consuming.
Common failure modes and recovery options
Failures during firmware flashing can include power loss, corrupted flash, or mismatched hardware revisions. Recovery often involves hardware-specific boot modes, recovery firmware images, or service-center re-flashing, which can be slow and costly. Driver update failures may cause blue screens, failed device initialization, or driver conflicts, but most OS ecosystems provide uninstall, rollback, or safe mode options to recover. Proactive validation, such as checking vendor hashes or running updates in a test environment, minimizes risk. If a failure occurs, avoid repeated attempts without a recovery plan; instead, switch to safe-mode operation or a known-good configuration, then reattempt with updated safeguards.
Practical testing and validation after updates
Validation should include functional testing of core hardware, peripheral components, and critical software workflows. For firmware, verify boot reliability, sensor readings, and security features, running endurance tests where applicable. For drivers, confirm device operation across applications, performance benchmarks, and compatibility with recent OS updates. Logging before and after the update helps diagnose issues quickly. Debricking recommends a two-step validation: perform a non-destructive test on a spare unit or simulation first, then run a controlled update on the target device with a rollback plan ready.
Update strategies by device category: consumer devices vs enterprise
Consumer devices favor convenience and rapid security patches, often through automated OTA updates. Enterprise environments demand rigorous controls, change management, and rollback capabilities; updates may be staged with approval gates and compliance reporting. In both cases, alignment between firmware and driver updates reduces risk. For individuals, a regular maintenance window (monthly or quarterly) is usually sufficient, but critical infrastructure may require more frequent checks. Debricking emphasizes tailoring the strategy to the device class and ensuring testing coverage mirrors real-world usage.
A practical, step-by-step update workflow you can follow
- Inventory: list all devices with current firmware and driver versions. 2) Evaluate risk: classify devices as high/medium/low risk based on criticality. 3) Prepare: backup configurations and ensure power stability. 4) Validate in a test environment if possible. 5) Implement updates in a staged rollout, starting with low-risk devices. 6) Verify results: run functional tests and security checks. 7) Document and monitor for anomalies. 8) Establish rollback steps and confirm recovery readiness. This workflow helps manage firmware and driver updates with discipline and clarity.
Debricking's framework: risk assessment, decision criteria, and rollback plans
Debricking advocates a formal framework that starts with risk assessment, decision criteria, and a documented rollback plan. The framework recommends prioritizing firmware updates for hardware security and stability while treating driver updates as ongoing maintenance for compatibility. A clearly defined rollback path should be tested before deployment, including a fallback plan to a known-good configuration. In 2026, Debricking’s guidance emphasizes automation where possible and ensuring teams are prepared to recover quickly from failures, keeping user downtime to a minimum.
How to maintain a firmware and driver update routine: schedules and tools
Create a maintenance calendar that aligns with vendor release cycles and security advisories. Use automated tooling where supported to monitor for new updates, verify signatures, and stage deployments. Maintain device groups to control update timing, and keep backups for configuration states and driver packages. Document lessons learned and refine the workflow after each cycle. A well-maintained routine reduces reactive firefighting and preserves long-term device health through consistent firmware and driver updates.
Comparison
| Feature | Firmware Updates | Driver Updates |
|---|---|---|
| Scope | Low-level hardware control and behavior changes | Software/OS compatibility and features |
| Delivery Method | Firmware image + bootloader updates via hardware interfaces | Software driver packages via OS update channels |
| Validation/Signing | Cryptographic signing; integrity checks at boot | Digital signatures and certificate validation during install |
| Rollback Capability | Hardware-level rollback in many devices; recovery mode often required | OS-level rollback or driver uninstall/reinstall available |
| Downtime/Impact | Potential downtime during flash; may require restart | Typically minimal downtime beyond reboot for many systems |
| Impact on Security | Can lock hardware into secure states; bricking risk if interrupted | Keeps OS and peripherals aligned with security features |
| Update Frequency | Typically infrequent; major or critical versions | More frequent with OS updates and peripheral patches |
| Best For | Embedded devices, sensors, and hardware that self-initializes | General PCs, laptops, printers, and peripherals |
Positives
- Improved security and hardware stability when updates succeed
- Clear, device-specific risk management with rollback options
- Firmware updates fix low-level issues inaccessible to software only
- Driver updates enhance compatibility and performance without flashing hardware
Disadvantages
- Firmware updates carry brick risk if interrupted or incompatible
- Firmware rollbacks can be hardware-limited and slow
- Driver updates can cause conflicts or driver regressions
- Both update types require proper validation and backups to avoid downtime
Adopt a layered, scheduled approach: firmware updates for hardware stability and security, driver updates for ongoing compatibility; test and rollback ready.
Firmware and driver updates each serve distinct roles. Prioritize firmware when hardware integrity and security are at stake, and treat drivers as ongoing maintenance for software compatibility. A tested rollback and backup plan minimizes downtime and user impact.
Questions & Answers
What is the difference between firmware and driver updates?
Firmware updates modify hardware behavior at a low level, often affecting boot and sensor calibration. Driver updates change software interfaces that let the OS talk to hardware, improving compatibility and performance. Both improve reliability and security, but they operate at different system layers.
Firmware changes hardware behavior at a fundamental level, while driver updates improve software communication with devices.
Can I update drivers without updating firmware?
Yes, in most cases you can update drivers independently of firmware. This is common for peripherals like printers, GPUs, or network adapters, and it minimizes risk since it avoids touching hardware initialization. Always verify compatibility with your OS version first.
Driver updates can usually be done without touching firmware.
What happens if a firmware update fails?
A failed firmware update can render a device nonfunctional or require recovery mode or service-center flashing. Always have a power-safe environment and a recovery plan. If possible, test the update on a spare device before applying broadly.
If firmware flashing fails, you may need a recovery procedure or service support.
Do all devices require firmware updates?
Not every device requires frequent firmware updates, but many modern devices benefit from periodic firmware updates for security and stability. Prioritize devices with exposed hardware controls or security-sensitive components.
Not every device needs updates all the time, but many do for security and stability.
How do I verify a firmware/driver update is legitimate?
Always download updates from official vendor channels, verify cryptographic signatures, and check the hash or certificate chain. Avoid third-party sources to prevent tampering or malware.
Only install updates from trusted sources and verify signatures.
What tools help manage firmware and driver updates?
Many vendors provide official update utilities, and some OSes offer centralized update management. For larger estates, consider device management platforms that support staged rollout and reporting.
Use vendor tools and OS-level update managers for reliable deployment.
Top Takeaways
- Plan updates with backups and a rollback path
- Treat firmware updates as higher-stakes changes
- Schedule driver updates as regular maintenance
- Validate after updates with functional tests
- Maintain a clear rollback protocol for both firmware and drivers