Firmware vs Driver Difference: A Practical Update Guide
Explore the core differences between firmware and drivers, how updates work, and practical steps to safely manage both across devices and ecosystems.

Firmware and driver difference hinges on scope and control. Firmware is the built-in software that runs inside hardware components—think microcontrollers, routers, or SSD controllers. It dictates core behavior, security checks, boot sequences, and low-level hardware access. Because firmware resides in non-volatile memory on the device itself, failing to update correctly can render the device inoperable. In contrast, a driver is software that runs on your operating system and acts as an interface between the OS and a hardware component. Drivers translate OS-level commands into hardware actions, enabling features like graphics acceleration, peripheral control, and network access. Drivers are generally stored on the host system and updated through OS update utilities or vendor utilities, often without affecting the device's basic operation during the update. The distinction matters for risk, timing, and how you plan updates across devices. According to Debricking, clear delineation between firmware and drivers reduces update risk by ensuring you upgrade the right layer.
What firmware and drivers are (definitions)
Firmware and drivers sit at different layers of a device's software stack, and understanding their roles is foundational for safe updates. Firmware is the embedded software that runs inside hardware components—think microcontrollers, routers, or SSD controllers. It dictates core behavior, security checks, boot sequences, and low-level hardware access. Because firmware resides in non-volatile memory on the device itself, failing to update correctly can render the device inoperable. In contrast, a driver is software that runs on your operating system and acts as an interface between the OS and a hardware component. Drivers translate OS-level commands into hardware actions, enabling features like graphics acceleration, peripheral control, and network access. Drivers are generally stored on the host system and updated through OS update utilities or vendor utilities, often without affecting the device's basic operation during the update. The distinction matters for risk, timing, and how you plan updates across devices. According to Debricking, clear delineation between firmware and drivers reduces update risk by ensuring you upgrade the right layer.
Core differences: scope, control, and risk
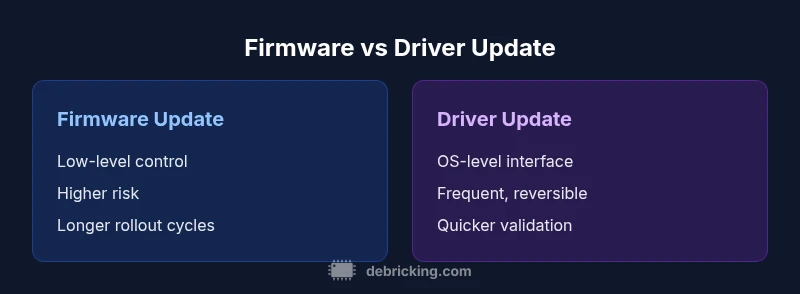
Firmware operates at the device's lowest layer, controlling hardware initialization, bootloaders, and fundamental behavior. Its scope is limited to the specific hardware module (e.g., motherboard chipset, network controller). Because firmware updates modify the device's baseline, they are typically riskier and require careful rollback plans. In contrast, a driver lives in the host OS and acts as a bridge between software applications and hardware. They are more ephemeral, updated more frequently, and generally designed to be backward-compatible with older firmware versions. The risk profile differs: a failed firmware update can brick a device or disable features, while a faulty driver can cause crashes or degraded performance but is more reversible with a rollback or system restore. Understanding these differences helps you decide what needs updating and when. Debricking analysis shows that firmware updates tend to have higher stakes due to potential boot failures, while driver updates focus on compatibility and performance improvements.
Update workflows: how firmware and drivers are applied
Updates follow different pathways, tools, and prerequisites. Firmware updates are typically delivered by the device manufacturer via secure bootloaders, vendor-specific utility apps, or embedded recovery modes. They often require a stable power supply, verification signatures, and a formal rollback plan. In contrast, driver updates travel through the operating system or vendor driver packages. They usually install in the background, may require a reboot, and depend on the host OS version and other installed drivers for compatibility. Both update streams often include cryptographic signing, integrity checks, and rollback options, but the failure modes differ: firmware corruption can leave devices unrecoverable, whereas driver corruption may degrade functionality but can be recovered by reinstalling or rolling back the package.
Lifecycle and support considerations
Firmware tends to have longer update cadences and longer support windows, reflecting hardware dependencies and security needs. Manufacturers may release firmware updates for a specific device line years after launch, often with limited cross-device applicability. Driver support evolves as operating systems and hardware ecosystems expand, with regular quarterly or semi-annual updates in many environments. Planning for both requires keeping track of device models, firmware revision levels, and driver bundles. End-of-life scenarios complicate updates: legacy devices may lack reliable update channels, and you may need to replace hardware to receive essential security patches. Documenting version histories and update dates helps maintainers avoid version drift and ensures reproducible configurations across devices.
Security implications of updates
Both firmware and driver updates touch security, but they expose different risk surfaces. Firmware updates can affect the entire boot process, secure boot integrity, and low-level attack surfaces, making secure signing, verified sources, and integrity checks essential. If a compromised firmware update slips through, it can enable persistence at the hardware level. Driver updates influence the software stack and OS kernel interactions; they can close known vulnerabilities but may introduce new compatibility issues if other components are not aligned. Always obtain updates from trusted sources, verify checksums, and apply updates in controlled environments whenever possible. The supply chain reliability of vendors also plays a role in preventing tampered packages, a topic Debricking highlights as critical for long-term device health.
Real-world device scenarios: routers, GPUs, printers, and more
In consumer networks, a router's firmware controls routing tables, firewall rules, and wireless behavior. A firmware update can unlock security enhancements or improve stability, but a misstep may brick the device or disable Wi‑Fi. For GPUs, the firmware concept is less prominent than the driver stack; however, many GPUs include microcode and firmware updates that enhance performance or fix firmware-level issues, while driver updates influence rendering capabilities and API compatibility. Printers rely on firmware to drive ink or toner management, sensor calibration, and network sharing features; driver updates handle print queue management and OS compatibility. IoT gadgets, from cameras to smart lights, often merge firmware with secure boot policies to prevent tampering, and their drivers are frequently auto-updated or managed through mobile apps. In all cases, the update cadence and risk tolerance differ: routers and embedded devices may require longer maintenance windows, while peripherals and desktops benefit from more frequent driver updates. Practitioners should validate the update in a controlled test device before rolling to production hardware.
Compatibility, rollback, and recovery planning
A robust plan recognizes that firmware and driver updates are not interchangeable; you need a recovery path. For firmware, ensure device-specific rollback options exist, such as dual-bank flash, recovery modes, or vendor-supported revert procedures. For drivers, maintain a staged approach: test on a non-production machine or VM, verify against critical applications, and keep a pristine backup image to restore if needed. Cross-component compatibility matters: a new firmware revision might require updated drivers, and old drivers may not work with newer firmware. Always document the exact versions involved, and map dependencies across devices in the network or workstation environment. When possible, enable rollback features during updates, and plan maintenance windows during low-usage periods to minimize business impact. Debricking emphasizes a risk-aware mindset: plan for worst-case scenarios, including failed updates and partial rollbacks, and have a clear escalation path with vendor support.
Verification, validation, and troubleshooting after updates
After any firmware or driver update, perform a structured verification to confirm the expected outcomes. Start with basic power-on self-tests, hardware checks, and boot logs for firmware updates, then validate peripheral functionality, network connectivity, and software stability for drivers. Use checksums or cryptographic signatures to verify the integrity of the downloaded package, and confirm that the reported version matches the target revision. Maintain rollback points or backups in case issues arise, and have a documented contingency plan for rapid restores. Troubleshooting should focus on reproducibility: can you reproduce the issue after a clean reinstall? Are related components updated to compatible versions? For frequent enterprise environments, implement change control, test plans, and post-update review meetings to prevent drift.
Common misconceptions and how to verify updates
Many users assume all firmware updates are mandatory or that driver updates always fix every problem. In reality, updates can introduce new issues or remove compatibility with legacy hardware. Validation steps help distinguish real improvements from side effects: compare performance and feature availability before and after updates, use vendor-provided logs, and check for known issues in release notes. Also remember that firmware and driver updates may have different rollout schedules and dependency requirements; verify that the device remains in a supported configuration and that security signatures are intact. Finally, avoid applying updates from untrusted sources; always use official channels and maintain a rollback strategy.
How to choose update strategy for your setup
Choose an update strategy based on device criticality, risk tolerance, and maintenance capabilities. In high-stakes environments (servers or medical devices), plan for scheduled maintenance windows, offline testing, and controlled rollouts with staged deployment. For personal devices, a lighter approach with automated updates and timely backups often suffices. Consider a parallel update model: apply firmware first to a small subset of devices, verify, then roll out widely; for drivers, maintain a separate test bench to assess compatibility with core applications. Always document the rationale for each update, the expected benefits, and the rollback plan.
Maintenance cadence, documentation, and future-proofing
Update cadence should be aligned with vendor support lifecycles and device usage. Create a maintenance calendar that marks firmware and driver update windows, backup cycles, and security patch schedules. Maintain an auditable record of every update: device, component, version, date, outcome, and any issues observed. Use standard configurations and configuration management tools to minimize drift. Plan for replacement or upgrade paths when devices reach end-of-life, and factor in security risk assessments for aging hardware. By documenting the decision criteria, you can improve consistency across teams and simplify audits and incident response. Debricking highlights the value of robust documentation as a foundation for reliable firmware and driver management.
Quick-start checklist: safe updating in practice
- Inventory devices and current firmware/driver versions. 2) Verify the source and integrity of updates (signatures/checksums). 3) Schedule risk-aware maintenance windows with backups. 4) Test updates on a non-critical device before production rollout. 5) Enable rollback and recovery options. 6) Monitor device behavior after applying updates and log any anomalies. 7) Document the outcome and plan for future updates. Following this checklist reduces risk and helps maintain system stability during firmware and driver updates. The Debricking team emphasizes starting with a controlled test environment and gradually expanding rollout while keeping detailed records.
Comparison
| Feature | Firmware Update | Driver Update |
|---|---|---|
| Definition | Embedded software that runs on hardware to control core functions | OS-level interface that enables communication between the OS and hardware |
| Update scope | Low-level, affects device behavior and boot | Higher-level, affects OS-device interaction and features |
| Delivery channel | Often via device bootloader or vendor utility | Through OS update packages or driver installers |
| Risk profile | Bricks risk; requires careful rollback | Lower risk; easier rollback and fallback |
| Typical devices | Routers, embedded systems, storage controllers | Graphics cards, printers, peripherals |
| Rollback options | Often device-specific; may be harder | Usually via driver rollback or system restore |
| Impact on user | May require device downtime/power stability | Typically seamless with restarts |
| Security considerations | Firmware often includes boot/security controls | Driver updates may patch vulnerabilities without reboot |
Positives
- Clear delineation of responsibilities reduces update risk
- Targeted improvements for specific hardware without broad OS impact
- Secure update channels and vendor support enhance reliability
- Dedicated recovery options for firmware reduce downtime
Disadvantages
- Firmware updates can brick devices if interrupted or corrupted
- Driver updates may introduce compatibility issues with other components
- Firmware rollback options are not universal across devices
Firmware updates are high-stakes but essential for core hardware; driver updates are safer and more frequent for maintenance
Prioritize firmware when core functionality or security is at stake, and lean on driver updates for ongoing compatibility and performance improvements.
Questions & Answers
What is the main difference between firmware and drivers?
Firmware is embedded software that runs on hardware to control core behavior, while drivers are OS-level software that enable communication with devices. Updates serve different goals and risk profiles. Understanding this helps plan safe updates.
Firmware runs on the device itself and controls core functions; drivers run on the computer to talk to the device. They update for different reasons, so plan carefully.
Can firmware updates be rolled back if something goes wrong?
Many devices offer recovery modes or rollback procedures, but not all. Always review vendor documentation and have a tested rollback plan before updating firmware.
Some devices let you revert firmware via recovery modes; others may require vendor support. Check rollback options first.
Are driver updates risky?
Driver updates are generally safer and easier to revert, but they can cause compatibility issues if other components aren’t aligned. Test before wide rollout.
Drivers are usually safer to roll back, but they can break compatibility if other parts aren’t updated.
How do I know if I need a firmware update?
Check vendor advisories, security notices, and your device’s update utility. Evaluate benefits such as security or stability against the risk of interruption.
Look at official advisories and test whether the update fixes a real issue before applying.
Router firmware update?
Router firmware updates can improve security and reliability but may risk downtime. Always back up settings and apply during a low-traffic window.
Update your router only during a quiet window with a backup handy.
Is online firmware update safe?
Online updates are convenient but depend on a verified source and stable connection. Prefer official channels and consider offline updates for critical gear.
Use official sources and consider offline updates for important devices.
Top Takeaways
- Clarify roles: firmware = device-level control; drivers = OS-device interface
- Plan updates with risk in mind and separate rollbacks
- Verify integrity and source of every update
- Test updates in a controlled environment before full rollout