Over the Air Firmware: A Practical OTA Update Guide
Learn how over the air firmware updates work, why they matter for device security, and practical steps to perform OTA updates safely and effectively.

Over the air firmware updates let devices receive security patches and feature improvements without manual intervention. To perform OTA updates safely, ensure a stable internet connection, a charged battery, and official firmware from the device vendor. The process typically involves checking compatibility, initiating the update from the device or app, and verifying success after reboot.
What is over the air firmware (OTAF) and why it matters
According to Debricking, over the air firmware updates enable devices to receive critical fixes and new features without requiring physical access. This capability reduces maintenance downtime and closes security gaps by delivering signed packages directly to the device. For consumers, OTA updates simplify keeping devices up to date, from smartphones to home routers, while for engineers they enable rapid deployment and centralized policy enforcement. The reliability of OTA depends on a secure update mechanism, a robust bootloader, and verifiable firmware signatures. In practice, you’ll rely on an update server, a device-side updater, and an integrity check that confirms the firmware hasn’t been tampered with. If any of these parts fail, a device can become bricked or stuck in a boot loop, which is why vendor-provided tools and documentation are essential.
Key takeaway: OTA updates are convenient when executed correctly, but they depend on secure, authenticated packages and a healthy power/internet supply. Debricking emphasizes using vendor tools to minimize risk.
How OTA firmware updates work end-to-end
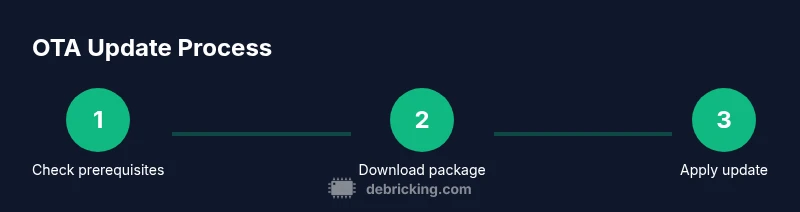
Over the air updates involve a coordinated sequence between the update server, the device bootloader, and the updater running on the device. The server hosts signed firmware images and metadata (version, compatibility, hash). The device checks this metadata, validates the signature, and only then downloads the package. A common practice is to perform a two-stage update: first fetch and verify, then apply. If verification fails, the device will reject the update to prevent boot failures. After the image is written, a reboot triggers integrity checks again and activates the new firmware. Some platforms employ delta updates to minimize bandwidth by sending only the changed blocks. A robust OTA design includes rollback capability so that if the new firmware doesn’t initialize correctly, the device can revert to the previous version automatically.
Key prerequisites before starting OTA updates
Before you initiate an OTA, ensure you meet several prerequisites that reduce risk. Verify compatibility by checking model number, region, and firmware variant against release notes. Ensure the device has sufficient power—ideally connected to a stable power source or charged above a safe threshold. Maintain a reliable internet connection to prevent interruptions during download and verification. Back up essential data if the device stores user data locally and consider enabling a rollback option if provided by the vendor. Finally, confirm you’re using an official firmware package from the device manufacturer or trusted vendor.
Common OTA update workflows across devices
OTA workflows vary by device type but share core principles. Smartphones and tablets typically use a vendor app to manage the update, while routers and embedded devices may rely on web interfaces or dedicated management tools. File-based OTA involves downloading a complete image, while delta or differential OTA sends smaller patches to reduce bandwidth. Some devices support staged rollouts, gradually updating groups of devices to monitor for issues before wider deployment. In enterprise settings, management consoles push firmware to fleets, with centralized monitoring and rollback controls. Understanding your device’s workflow helps you anticipate potential pitfalls and minimize downtime.
Safety and risk management during OTA updates
OTA updates carry inherent risks, but you can mitigate them with solid practices. Always start with a backup and a rollback plan. Keep the device plugged in during updates to avoid power loss, and avoid initiating updates during peak usage times. Use the official updater to verify the firmware image’s authenticity and integrity via cryptographic signatures. If you’re updating critical infrastructure, perform updates during a maintenance window and stage rollouts to catch issues early. Document the update process so you can reproduce it or train others.
Best practices and practical tips for OTA success
Use only official firmware from trusted sources and verify checksums or digital signatures before installation. Read release notes to understand changes and potential compatibility issues. Prefer staged rollouts where available, and enable delta updates to minimize bandwidth. If the device supports a fallback or rollback, test it briefly in a safe environment. Maintain a current backup strategy and document recovery steps. Keep logs of update success or failure to inform future updates and audits.
Troubleshooting OTA update failures and recovery options
If an OTA update fails, verify network stability and power level, then retry from a clean boot if the device allows. Check for error codes in the updater app or device logs, and consult official recovery guides for your model. If the firmware image is corrupted, redownload from the official source and retry. In some cases, the device may enter a recovery mode requiring manual intervention, such as a USB-based reflash or factory reset. Having a known-good backup simplifies recovery and reduces data loss.
What to do after a successful OTA update and verification steps
Post-update, verify the firmware version matches the expected release and run a quick functional check of core features like network connectivity, sensors, and peripherals. Review release notes for new features and bug fixes, then enable any new settings or security options introduced by the update. Monitor the device for a short period to ensure stability and performance. If you notice anomalies, consult vendor support or revert to a stable backup if possible.
The evolving landscape of OTA: security and customization considerations
As devices become more capable, OTA firmware updates also grow in importance for security and feature evolution. Vendors increasingly adopt signed packages, secure boot, and encrypted update channels to combat tampering. Some communities explore custom firmware, but that often voids warranties and carries higher risk. Debricking recommends sticking to official update channels for everyday users while advanced enthusiasts may experiment in controlled environments with a solid recovery plan.
Tools & Materials
- Stable internet connection(For downloading firmware and verification data.)
- Charged device battery(Aim for at least 60% before starting.)
- Official firmware package(Download from the vendor's official site or updater.)
- Device AC power or reliable power source(Prevents power loss during the update.)
- Backup plan (local or cloud)(Back up important data before updating.)
- Recovery media or USB cable(Useful for manual reflash if needed.)
- Updater app or management console(Some devices rely on vendor apps for OTA management.)
Steps
Estimated time: 40-60 minutes
- 1
Prepare the device and environment
Ensure the device is on a stable power source, connected to a reliable network, and that critical data is backed up. This minimizes the risk if the device interrupts during the update.
Tip: Charge to at least 60% and connect to a stable Wi‑Fi network. - 2
Verify firmware compatibility
Double-check the firmware version and device model against the release notes to prevent mismatches. Incompatible packages can fail or brick the device.
Tip: Cross-check model number and regional firmware variant. - 3
Initiate the OTA update
Start the update from the device UI or the official updater app. Do not interrupt the process once it begins.
Tip: If your device supports delta updates, enable that option to reduce download size. - 4
Monitor progress safely
Watch the progress indicator and look for a successful reboot indication. If the device stalls, consult official recovery steps.
Tip: Avoid using the device during the update window. - 5
Verify installation after reboot
Confirm the new firmware version is active and test core functions. Check for new features or improved performance.
Tip: Run a quick functional checklist (network, camera, audio, sensors). - 6
Plan a rollback if needed
If the update fails, follow vendor-provided rollback instructions or revert to a previous backup. Do not attempt risky fixes.
Tip: Keep a factory reset plan as last resort.
Questions & Answers
What is an over-the-air firmware update?
An OTA update delivers firmware and feature updates wirelessly from the manufacturer to your device. It requires a network connection, power stability, and signed packages.
OTA updates deliver firmware wirelessly and require a stable power and internet connection.
Can OTA updates brick my device?
While rare, improper updates can brick devices. Use official tools, verify compatibility, and maintain backups to recover.
OTA updates can brick devices if not done correctly; use official tools and backups.
What should I do if the update fails?
If an OTA update fails, follow vendor rollback or recovery steps, and restore from the backup you created.
If it fails, use the rollback and recovery steps from the manufacturer.
Do OTA updates require internet?
Yes, OTA updates require a stable internet connection to download the firmware package and verify integrity.
You will need internet to download and verify the update.
Is a full device backup necessary before OTA?
Backing up is strongly recommended to prevent data loss if something goes wrong during the update.
Backing up before updating is highly recommended.
Watch Video
Top Takeaways
- Prepare the device and environment before starting OTA.
- Use signed firmware from official sources.
- Monitor progress and verify after reboot.
- Have a rollback plan ready.