Firmware Over the Air: A Practical OTA Update Guide
Learn how to safely perform firmware over the air updates on your devices. This step-by-step guide covers prerequisites, verification, rollback, and security practices.
You will learn how to perform a firmware over the air update on your device, including prerequisites, safety checks, and a step-by-step deployment. Ensure your device supports OTA, have a stable internet connection, and back up important data. This guide covers preparing, initiating, validating, and rolling back if needed today.
What is firmware over the air (OTA)?
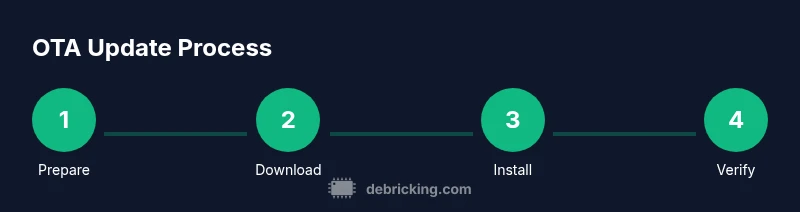
Firmware over the air (OTA) is the process of delivering firmware updates to a device remotely, without requiring a physical connection or user intervention beyond initiating the update. OTA updates can patch security vulnerabilities, fix bugs, add features, and improve performance. They rely on a secure update channel, authenticated firmware images, and a fail-safe fallback so devices don't become bricked if the connection is unstable. According to Debricking, OTA updates are a cornerstone of long-term device reliability because they minimize downtime and simplify maintenance for both individuals and fleets. In practice, OTA updates typically involve four stages: check compatibility, download, install, and verify. The key benefit is speed and convenience: a device can receive a critical update while the user continues with daily tasks. The main caveats are the risk of interruption, insufficient power, and the potential for bricking if a bad image is installed. Understanding these dynamics helps you plan safer deployments and avoid common mistakes.
Why OTA updates matter for device health
OTA updates matter because they keep firmware current, patch security flaws, and ensure new features work as intended. Consistent OTA cadence reduces the attack surface and minimizes service interruptions that come from manual updates. Debricking analysis shows that devices with reliable OTA updates maintain firmware integrity and security posture better than those relying on manual, ad-hoc updates. When deployed correctly, OTA updates can be rolled out gradually, allowing administrators to monitor affected subsystems and rollback if issues arise. The trade-off is the risk of bricking if the update image is corrupted or interrupted, which is why validation steps and power guarantees are non-negotiable. For fleet owners, OTA simplifies compliance reporting and asset management by centralizing version control and deployment logs.
Prerequisites and safety checks
Before starting an OTA update, verify device compatibility and current firmware version. Ensure the device has sufficient battery (or is connected to power) and a stable network connection. Back up essential data and note the current version so you can compare post-update behavior. Confirm that the update channel is official and authenticated, and review available release notes for known issues. If you manage multiple devices, consider staging the update on a small subset first to observe performance and avoid mass outages. Debricking emphasizes documenting each device’s status and keeping logs for audits and support.
Security considerations for OTA updates
Security is not optional for OTA. Always validate firmware signatures and use encrypted channels to protect data in transit. Enforce certificate pinning where possible to prevent man-in-the-middle attacks and ensure the update server is trusted. Maintain an auditable update trail, including version, hash, and timestamp. Disable partial or unverified updates, and require user consent only if appropriate for critical devices. For added resilience, enable rollback to a known good image if post-update validation fails.
Verification and rollback strategies
After installation, verify the firmware version, feature set, and basic functionality through automated checks or manual tests. Confirm that security services (like encryption and secure boot) remain active. If issues are detected, perform a controlled rollback to the previous version using the device’s recovery mechanism or a managed rollback feature. Always have a backup plan, including preserved logs and the ability to restore from a saved image or snapshot. This approach minimizes downtime and preserves device trust.
Troubleshooting and best practices for OTA deployments
Common OTA failures arise from power loss, unstable networks, or corrupted image files. Always verify the integrity of the downloaded image with a hash check before installation. If the update fails, collect logs, check for known issues in release notes, and attempt a safe rollback. For best results, plan updates during low-usage windows, monitor traffic with lightweight health checks, and use staged rollouts to limit blast radius. Regularly test recovery procedures so you’re prepared for real-world incidents.
Tools & Materials
- Device with OTA capability(Ensure device supports OTA and is not in a locked bootloader state.)
- Power source(Keep device plugged in or charged to prevent mid-update shutdown.)
- Stable network connection(Prefer wired Ethernet or strong Wi-Fi with minimal jitter.)
- Backup medium(Back up important data and current firmware state.)
- Access credentials(Have admin credentials or an official vendor account for deployment.)
- Update package/channel access(Use the official OTA channel or vendor management platform.)
Steps
Estimated time: 45-75 minutes
- 1
Validate prerequisites
Confirm device compatibility and current firmware version. Ensure the device has sufficient power and a reliable network connection before starting the update. Prepare a backup and note the intended target version to compare post-update behavior.
Tip: Check battery level and ensure it is at least 50% or plugged in before proceeding. - 2
Initiate the OTA update
Trigger the update from the official OTA channel or device UI. If you manage multiple devices, use a staged rollout to limit exposure. Confirm the update package signature before beginning.
Tip: Prefer a wired network to reduce risk of interruption. - 3
Monitor the update progress
Watch the progress indicator and logs for any anomalies. Do not disconnect or reboot the device during installation. If the device reboots, allow the process to complete without interference.
Tip: Use a lightweight health check to ensure update packets are received continuously. - 4
Verify installation
After installation, verify the firmware version and run basic functionality tests. Check security services and boot integrity to ensure the system is healthy.
Tip: Run a signature/hash check to confirm image integrity. - 5
Test post-update behavior
Validate key features and interfaces to ensure expected behavior. Check for any new settings or features introduced by the update and confirm compatibility with existing apps.
Tip: Document observed behavior for future audits. - 6
Rollback if necessary
If issues surface, initiate a rollback to the previous stable image using the device’s recovery flow. Re-run backups and verify original behavior before closing the incident.
Tip: Maintain a ready-to-apply rollback image and a clear rollback plan.
Questions & Answers
What does OTA mean for consumer devices?
OTA means updates are delivered wirelessly to devices, replacing manual USB/CD updates. It minimizes downtime and streamlines maintenance, but requires secure channels and rollback options in case of failure.
OTA updates deliver firmware wirelessly to devices, reducing manual work and downtime while needing secure channels and rollback options.
Can OTA updates be performed without Internet access?
Most OTA updates require internet access to download the firmware package. In some enterprise scenarios, a local update server can provide the package, but network access is still essential.
OTA needs network access to download updates; some setups may use a local server, but internet or local network connectivity is typically required.
What should I do if an OTA update fails midway?
If an update fails, stop further actions, attempt a controlled rollback to the previous image, review logs for errors, and reattempt the update after resolving the issue. Do not retry blindly without validation.
If something goes wrong, rollback to the last good version, check logs, fix the root cause, and try again with caution.
How do I verify that an OTA update is authentic and safe?
Check the update signature and hash against the trusted source, ensure the channel is official, and confirm secure boot or device integrity checks post-update.
Look for a valid signature and verified channel, then confirm the device boots securely after update.
Are older devices more at risk during OTA updates?
Older hardware can be more susceptible to power loss or compatibility issues, but following safe practices (backups, staged rolls, and rollback options) mitigates risk.
Older devices can be riskier, but good practices like backups and staged rollouts help mitigate that.
Watch Video
Top Takeaways
- Plan OTA maintenance windows and communicate them.
- Verify update signatures and integrity before install.
- Back up data and current firmware versions beforehand.
- Ensure the device remains powered and connected during update.
- Test core functionality after installation and log results.