OTA Firmware Updates: A Practical Step-by-Step Guide
Learn how to perform OTA firmware updates safely. This Debricking guide covers prerequisites, steps, backups, and troubleshooting to keep devices secure with over-the-air upgrades.

OTA firmware updates deliver updates over a network, enabling devices to improve security, stability, and features without manual installation. This guide shows how to prepare, execute, and verify OTA updates safely across a range of devices.
What is OTA firmware and how it works
Over-the-air (OTA) firmware is a mechanism that lets a device receive and apply software updates remotely via Wi‑Fi, Ethernet, or cellular networks. The update package is authenticated and signed by the vendor to prevent tampering, and the device may reboot during the install. For most consumer devices, OTA reduces downtime and eliminates the need for physical connections. Debricking notes that a well-managed OTA process improves security by delivering patch updates quickly and consistently, especially when devices are widely deployed in homes or small offices. When implementing OTA, developers and support teams typically package updates with rollback options and progress indicators to minimize user frustration and the risk of bricking.
Key terms to know include: incremental updates (smaller payloads), delta updates (only changed blocks), and rollback (reverting to a known-good state if something goes wrong).
Why OTA updates matter for reliability and security
OTA firmware is a cornerstone of modern device maintenance. They allow vendors to push critical security patches, bug fixes, and feature enhancements without requiring end users to download files manually. For device owners, OTA updates reduce the risk of running outdated firmware that could be vulnerable to exploits. Debricking emphasizes that consistent OTA practices can shorten exposure windows after a vulnerability is disclosed and improve device longevity by ensuring support lifecycles are fulfilled. The right OTA strategy also helps organizations stay compliant with security standards and reduce support costs by minimizing on-site service visits.
Risks and caveats of OTA updates
OTA updates are generally safe, but they carry risks if not managed properly. A failed update can leave a device in an unusable state, a scenario often described as “bricked.” To mitigate this, manufacturers implement verification steps, signed updates, and recovery modes. Users should avoid updating over unstable networks, ensure the device has sufficient power, and verify the update package is from an official source. Debricking highlights the importance of rollback mechanisms and staged rollouts to limit the blast radius if something goes wrong. It’s also wise to monitor battery levels and avoid performing updates during peak usage times to minimize the chance of interruption.
Preparing for an OTA update: prerequisites and safety
Preparation is the difference between a smooth OTA and a failed attempt. Begin by confirming device compatibility with the target firmware version and reading the vendor’s release notes for known issues. Ensure you have a reliable internet connection (prefer wired or strong Wi‑Fi), a secure power source, and a current backup of important settings or data. Debricking recommends enabling any available backup or snapshot features before starting the update so you can restore a previous state if needed. If the device supports a recovery mode, locate the recovery method in advance and note any PINs or passwords required.
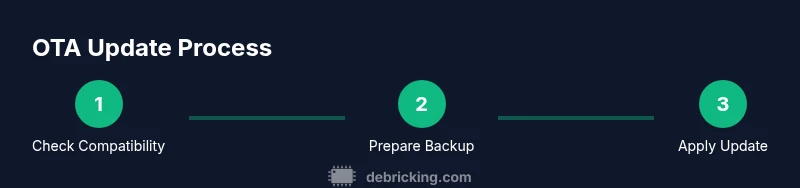
In practice, create a short plan: (1) verify firmware version and device model, (2) back up essential data, (3) connect to a stable network, (4) start the OTA process, and (5) monitor the update until completion.
How to verify device compatibility and backup before OTA
Before initiating OTA, verify the device and firmware headers align (model number, region, and current version). Use the vendor’s official channels to confirm compatibility and download integrity via checksums or signatures. Backups should capture user settings, configuration profiles, and critical data. Debricking notes that backups are not a one-size-fits-all solution; some devices support incremental backups, while others require full restores. Create a local backup first, then upload a copy to a trusted cloud storage if available. Establish a rollback plan in case the update introduces instability.
Best practices for OTA firmware updates across devices
Adopt a consistent OTA workflow across your fleet of devices. Use staged rollouts to limit the number of devices updating at once, monitor for early warning signs, and provide users with clear status indicators and estimated completion times. Maintain a changelog and user-facing notes explaining why the update was released and what issues it addresses. Debricking recommends configuring a secure channel for update delivery, verifying signatures, and enabling fail-safes like dual partitions or fallback recovery modes to protect against corrupted updates. For embedded devices, ensure bootloaders are updated in tandem to support the new firmware.
Additionally, consider network considerations: prefer stable networks and minimize contention by scheduling updates during off-peak hours. Document any regional or device-specific constraints so technicians can troubleshoot efficiently.
Troubleshooting common OTA update issues
If an OTA update fails, first consult the device’s recovery options and logs. Common failure causes include network drops, corrupted update packages, insufficient power, or incompatibility. Try repeating the update over a more reliable connection, disable VPNs if necessary, and validate the checksum of the downloaded file. If rollback is available, revert to the previous firmware and reattempt after confirming prerequisites. For devices with dual partitions, you can reboot into the older partition to restore functionality while diagnosing the issue. Debricking emphasizes keeping a repair window and documenting failure modes for future fixes.
Security considerations for OTA firmware updates
OTA security hinges on authenticated firmware, encrypted transport, and secure storage of update credentials. Always obtain firmware from official vendor channels, verify digital signatures, and use encrypted connections (TLS) during transfer. Disable insecure protocols and enforce firmware integrity checks on the device side. Debricking recommends enabling device attestation and monitoring for anomalous post-update behavior as part of a proactive security program. Regularly audit update mechanisms and review access controls for the update server to prevent supply-chain risks.
Tools & Materials
- Stable power source(Plug device into a reliable power outlet or ensure battery is at least 50% charged)
- Official firmware package or vendor OTA channel(Only use signed updates from the device maker)
- Reliable network connection(Prefer wired Ethernet or strong Wi-Fi during the update)
- Backup storage(Local backup plus cloud backup if available)
- Documentation access(Release notes, compatibility table, and recovery steps)
- Recovery/access to device boot mode(Optional for devices with recovery partitions or USB fallback)
Steps
Estimated time: 30-60 minutes
- 1
Verify compatibility and download
Check device model, region, and current firmware version against the vendor's release notes. Download or prepare the OTA package via the official channel and verify its integrity with the provided checksum.
Tip: Double‑check the checksum before proceeding to avoid corrupted updates. - 2
Back up settings and data
Create a full backup of device configurations and any user data. If the device supports snapshots, initiate a snapshot for quick rollback.
Tip: Store backups offline if possible to protect against server outages. - 3
Prepare power and network
Connect to a stable power source and a reliable network. If possible, use a wired connection to minimize interruptions during the update.
Tip: Disable power-saving modes that might pause network activity during the update. - 4
Initiate the OTA update
Start the OTA process from the device UI or management app. Follow prompts exactly and avoid canceling unless a clear error appears.
Tip: Do not interact with the device during the install unless prompted. - 5
Monitor progress and wait
Watch the progress indicator and verify any post‑update reboot occurs. Do not unplug the device during reboot sequences.
Tip: If the update stalls beyond the vendor’s listed timeframe, initiate a safe restart via recovery mode if available. - 6
Verify and validate
Confirm the new firmware version, test core features, and restore from backup if needed. Check security patches and review release notes for new settings.
Tip: Keep a record of the new version for future reference.
Questions & Answers
What is OTA firmware?
OTA firmware refers to firmware updates that are delivered over the air through a network connection. The device downloads, verifies, and installs the update automatically or with user confirmation. This method reduces manual interventions and keeps devices current with security fixes and feature enhancements.
OTA firmware is updates delivered over the air via the device's network connection, making updates easier and more timely.
Is OTA updates safe for my device?
When obtained from the official vendor and verified, OTA updates are generally safe. Risks arise if the update is corrupted, interrupted, or sourced from unofficial channels. Always use signed updates and uninterrupted power.
OTA updates are safe when you use official sources and ensure the power stays on during the process.
What should I do if an OTA update fails?
If an OTA update fails, check recovery options, verify power and network stability, and use the rollback feature if available. Re-download the patch from the official channel and retry after validating integrity.
If it fails, use recovery options, verify connections, and retry with official firmware.
Can I revert to a previous firmware after OTA?
Many devices support rollback to a previous firmware version via a recovery mode or backup snapshot. Keep a known-good backup handy and follow vendor instructions for safe rollback.
Yes, many devices let you rollback using recovery or a backup snapshot.
How long does an OTA update take?
Update durations vary by device and package size but typically range from a few minutes to about half an hour. Larger firmware with multiple partitions may take longer.
Most OTA updates finish in minutes to about thirty minutes depending on the device.
Do I need internet connectivity for OTA?
Yes, OTA requires an active internet connection to fetch the update package. A stable connection reduces the risk of interruption that could corrupt the update.
Internet is required to download the update package.
Watch Video
Top Takeaways
- Plan OTA updates with backups in place.
- Verify compatibility and integrity before starting.
- Maintain secure, reliable network conditions during install.
- Monitor progress and confirm post-update functionality.
- Document firmware versions for audits and support.