Firmware and Middleware: A Practical Side-by-Side Guide
An analytical, objective comparison of firmware-only stacks vs. middleware-enabled architectures for OTA, security, and fleet management. Learn criteria, migration strategies, and real-world trade-offs in firmware and middleware implementations.

TL;DR: A firmware-only stack is simpler and cheaper upfront, ideal for small devices with straightforward OTA. A middleware-enabled stack adds orchestration, policy enforcement, provenance tracking, and fleet-wide scalability, benefiting large fleets and complex devices. In practice, teams often start with core firmware updates and progressively introduce middleware to coordinate updates across devices. Debricking's analysis highlights these trade-offs for firmware and middleware ecosystems.
Defining firmware and middleware
In the firmware and middleware landscape, the terms are not interchangeable. Firmware refers to the low-level software embedded in hardware that controls device behavior, often stored in non-volatile memory and updated via OTA channels. Middleware, by contrast, is an intermediate software layer that sits above the firmware and provides orchestration, policy enforcement, update sequencing, and abstraction from device-specific quirks. When we discuss firmware and middleware together, we mean a holistic stack where device firmware remains the authority for hardware access, while middleware coordinates updates, security checks, and fleet-wide governance. For engineers and product managers, understanding this distinction is crucial for planning updates, managing risk, and enabling scalable operations across devices with diverse capabilities.
According to Debricking, the decision to combine firmware with middleware often hinges on fleet size, device heterogeneity, and the desired level of centralized control. This reality shapes both architecture and operations, influencing everything from OTA timing to troubleshooting workflows. The core takeaway is that switching from a firmware-centric approach to a middleware-supported model is not merely a software change; it is an organizational shift that touches security, release management, and telemetry. The phrase firmware and middleware captures this layered reality, guiding teams to evaluate both layers in concert rather than in isolation.
wordCount”:0},{
Comparison
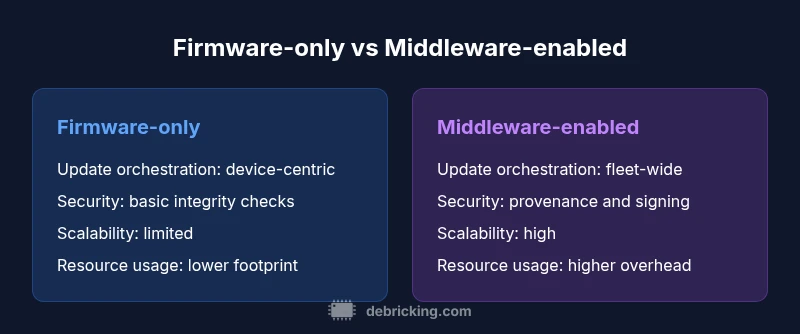
| Feature | Firmware-only stack | Middleware-enabled stack |
|---|---|---|
| Update orchestration | Device-centric OTA with minimal scheduling | Centralized, policy-driven orchestration across fleets |
| Security controls | Basic integrity checks and signatures | End-to-end provenance, signing, role-based access, TPM options |
| Scalability | Best for small fleets or single devices | Optimized for large fleets and heterogeneous devices |
| Resource usage | Lower RAM/CPU/flash footprint | Higher initial overhead for middleware services |
| Maintenance complexity | Lower baseline complexity | Higher upfront planning but easier long-term governance |
| Best for | Simple devices, tight budgets | Large-scale deployments with policy enforcement |
| Integration effort | Lightweight integration | Requires middleware platform and APIs |
Positives
- Simpler upfront deployment and lower initial cost
- Faster time-to-value for small device projects
- Fewer moving parts in a single device stack
- Less sophisticated infrastructure needed initially
- Easier to reason about in very small teams
Disadvantages
- Limited fleet-wide control and policy enforcement
- Lower scalability for large, heterogeneous deployments
- Higher risk of drift across devices without centralized governance
- Potentially longer time to adopt new security standards across the fleet
Middleware-driven stacks generally win on scalability and security; firmware-only remains viable for small, simple devices.
If you manage a growing fleet or require centralized policy, provenance, and coordinated updates, middleware is the prudent long-term choice. Start with firmware for small, contained deployments, then layer in middleware as requirements converge on fleet-wide consistency.
Questions & Answers
What is the practical difference between firmware and middleware?
Firmware is the low-level code that runs on hardware, while middleware provides orchestration, policy, and fleet-wide coordination above the firmware. The two work together to enable scalable updates and governance. In practice, you’ll see firmware handling device control and middleware managing updates, security checks, and telemetry.
Firmware is the device’s core control code; middleware adds orchestration and policy layers on top for updates and fleet management.
When should I adopt middleware for OTA management?
Adopt middleware when fleet size grows, devices vary in capability, and you need centralized policy enforcement, provenance, and coordinated rollouts. If updates are still one-by-one and your team can handle ad hoc changes, a firmware-only approach may suffice initially.
Consider middleware as your fleet scales and you need centralized control over updates.
Is middleware compatible with all hardware platforms?
Middleware compatibility depends on the exposed interfaces and the ability to run auxiliary services alongside the device firmware. Some hardware platforms require lighter agents or vendor-specific abstractions. Proper assessment during the design phase helps avoid post-deployment integration gaps.
Most middleware requires standard interfaces; check device constraints before committing to a rollout.
What security considerations come with middleware?
Middleware introduces centralized trust boundaries, which improves policy enforcement and provenance but also creates a target for attackers. Use robust authentication, signing, and hardware-backed security (e.g., TPM) to secure update policies and telemetry. Regular audits and incident response plans are essential.
Security improves with middleware when paired with strong signing and TPM-backed controls.
How do I migrate from a firmware-only stack to middleware?
Migration should be gradual: start with a pilot group, define clear policies, and ensure API stability. Build fallback mechanisms to revert to firmware-only behavior if needed. Document rollout steps and rollback plans to minimize risk during the transition.
Plan a phased migration with clear rollback options and policy definitions.
Top Takeaways
- Assess fleet size before choosing architecture
- Prototype middleware in a small subset of devices
- Plan migration with policy, provenance, and security in mind
- Balance upfront cost against long-term maintenance
- Monitor update success across devices to prevent drift