Difference Between Firmware and Middleware: A Practical Guide
Explore the difference between firmware and middleware, their roles, lifecycles, and how to decide the right approach for your device project. Insights from Debricking to guide design and updates.
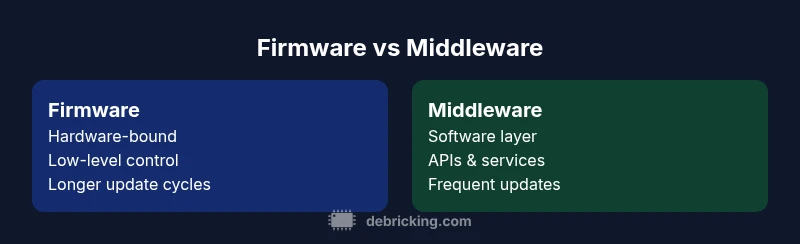
A quick comparison: firmware is the low‑level, hardware-bound code that initializes and controls device hardware, while middleware sits above the OS to coordinate software components and services. The difference between firmware and middleware lies in scope, update cadence, and how tightly each layer is bound to hardware, developer workflows, and maintenance planning.
What are firmware and middleware? Definitions and scope
Firmware is the low‑level code embedded in hardware that directly initializes components, controls peripherals, and enforces safety and power policies. It is stored in non‑volatile memory and loaded at boot, often with updates that are tightly controlled by hardware vendors. Middleware, on the other hand, is software that runs on top of the operating system to enable communication, data flow, and service orchestration across applications. The difference between firmware and middleware hinges on scope, lifetime, and dependency: firmware touches the hardware layer and tends toward stability across generations, while middleware interacts with the OS and services to provide flexibility and extensibility. In most modern devices you will find both layers in concert: a compact firmware core handling critical tasks, plus a richer middleware stack that enables features, ecosystem integration, and developer extensibility. According to Debricking, clarifying these roles early in design reduces update risk and speeds debugging.
Historical context and architectural roles
Firmware’s roots lie in bootstrapping hardware, configuring registers, and ensuring safe startup sequences. Middleware emerged to abstract complexity, offering reusable services, messaging, and orchestration across software modules. The boundary between firmware and middleware is not a single line but a gradient: firmware handles closest‑to‑hardware tasks, while middleware coordinates software layers and services at a higher level. Debricking’s analysis highlights that teams that define these boundaries clearly experience smoother upgrades and more predictable maintenance trajectories across device lifecycles.
Key functional differences: scope, lifecycle, and updates
- Scope and responsibilities: firmware implements drivers, bootloaders, and low‑level control; middleware provides APIs, data routing, and service orchestration.
- Lifecycle and updates: firmware updates tend to be hardware‑revision aligned and longer‑cycle, whereas middleware updates are more frequent and versioned, with safer rollback paths.
- Dependencies: firmware relies on fixed hardware capabilities; middleware depends on OS, runtimes, and driver stacks, making it more portable within a family of devices.
- Performance and footprint: firmware must be compact and deterministic; middleware can be feature‑rich but introduces additional layers that affect latency and resource usage.
- Security considerations: firmware carries hardware‑backed trust anchors; middleware expands the security surface but benefits from layered protections, like secure communications and authentication.
Practical implications for developers and device owners
Developers must decide early whether to prioritize a lean, hardware‑focused firmware or a modular middleware architecture that can evolve. For devices requiring strict hardware control and long lifecycles, a firmware‑centric approach with clear interfaces may be preferable. If the goal is rapid feature delivery, cross‑device interoperability, and ecosystem support, a robust middleware layer becomes essential. Debricking recommends documenting the boundary between firmware and middleware in system design documents, which aids testing, integration, and upgrade planning. This clarity reduces ambiguity during rollout and helps teams allocate testing resources effectively.
Update processes, risk, and rollback strategies
Firmware updates involve careful change control, reproducible builds, and thorough hardware‑level testing. Secure boot, cryptographic signing, and staged rollouts minimize the risk of bricking a device during an update. Middleware updates can be delivered more fluidly through service packs or containerized components, enabling faster iteration and smarter rollbacks. The fundamental difference in update risk between the two layers is that firmware changes can permanently affect hardware behavior, while middleware changes tend to affect software ecosystems with a lower brick risk if proper rollback mechanisms exist.
Real‑world scenarios: IoT, embedded, and consumer devices
IoT sensors rely on firmware to manage calibration, power, and sensor interfaces, while middleware handles data aggregation, protocol translation, and cloud connectivity. In consumer electronics, firmware boots the device and provides low‑level control, whereas middleware supports app ecosystems, feature flags, and inter‑device communication. Understanding these roles helps teams craft robust update strategies and prevents cascading failures when deploying new features or security patches. Debricking’s guidance emphasizes pairing a stable firmware base with a flexible middleware layer to maximize both reliability and adaptability.
Common misconceptions and pitfalls
A common misconception is that firmware and middleware are mutually exclusive or mutually exclusive upgrades. In practice, many devices blend both layers, with firmware providing core reliability and middleware delivering scalability and ecosystem connectivity. Another pitfall is assuming uniform risk across updates; firmware changes can brick hardware if not validated, while middleware changes demand compatibility testing across software layers. Clear boundary definitions reduce integration risk and improve testing coverage, especially for safety‑critical devices like medical sensors or automotive components.
How to decide the right approach for your project
Begin by mapping hardware interactions and the required software agility. If your priority is rock‑solid hardware control and long lifecycles, aim for a lean firmware design with a stable update path. If you expect frequent feature updates, cloud integration, and cross‑device interoperability, invest in a well‑defined middleware layer that can evolve independently of hardware. Best practices emphasize keeping firmware surface area minimal and well‑documented while using middleware to address new requirements, integrations, and ecosystems.
Integrating both layers: best practices
- Define explicit interfaces between firmware and middleware (APIs, boot sequences, and messaging protocols).
- Use versioned, signed delivery for both layers, with clear rollback plans.
- Implement robust testing that covers hardware‑level regression and software compatibility across stacks.
- Document failure modes and diagnostic procedures to speed recovery after updates.
- Plan security holistically, balancing hardware‑anchored protections with middleware‑level access controls and monitoring.
comparisonTable":{"items":["Firmware-centric approach","Middleware-centric approach"],"rows":[{"feature":"Role in system","values":["Closest to hardware, drivers and boot logic","Orchestrates services, APIs, and inter‑component communication"]},{"feature":"Update mechanism","values":["Hardware‑integrated updates, longer cycles","Frequent software updates, versioned releases"]},{"feature":"Dependencies","values":["Tightly bound to hardware capabilities","Depends on OS, runtimes, and drivers"]},{"feature":"Portability","values":["Device‑specific, less portable across models","More portable across devices with similar OS/runtime"]},{"feature":"Performance impact","values":["Deterministic, minimal latency for core functions","Additional layers can add latency but enable flexibility"]},{"feature":"Security posture","values":["Hardware‑backed trust, secure boot","Layered security, service‑level authentication"]},{"feature":"Best for","values":["Low‑level control, long‑term stability","Rapid feature deployment and interoperability"]}]}},"prosCons":{"pros":["Clear boundaries improve maintainability","Targeted testing for each layer","Better rollback strategies when separated"],"cons":["Separate layers can introduce integration complexity","Two‑layer maintenance may require more coordination"]},
verdictBox":{"verdict":"Firmware vs Middleware: choose based on risk tolerance and update needs","confidence":"high","summary":"Firmware offers stability and hardware control; middleware enables flexibility and interoperability. The best path often combines both with well‑defined boundaries."},
keyTakeaways":["Define clear boundaries between firmware and middleware","Prioritize stability in firmware updates","Invest in modular middleware for agility","Plan testing and rollback for both layers","Document architecture decisions early"],
faqSection":{"items":[{"question":"What is the difference between firmware and middleware?","questionShort":"Difference?","answer":"Firmware runs on hardware to control low‑level functions, while middleware provides services and communication between software components. The difference between firmware and middleware lies in scope and update strategies.","voiceAnswer":"Firmware is hardware‑bound software; middleware sits between OS and apps to coordinate functions.","priority":"high"},{"question":"Can firmware include middleware?","questionShort":"Can firmware include middleware?","answer":"In many devices, firmware includes minimal middleware features for hardware interaction. However, the core middleware stack typically runs on top of firmware, within the OS layer.","voiceAnswer":"Often, firmware contains basic control logic, middleware lives higher up.","priority":"medium"},{"question":"How do I decide which approach to take?","questionShort":"Decision approach?","answer":"Map hardware dependencies and update needs. If you require stability and hardware focus, favor firmware‑driven design; if you need flexibility and ecosystem integration, invest in middleware.","voiceAnswer":"Start with hardware requirements, then plan for software flexibility.","priority":"high"},{"question":"What are common risks with firmware updates?","questionShort":"Firmware risks?","answer":"Firmware updates risk bricking devices if validation fails. Use secure boot, signed images, and staged rollouts to mitigate this risk.","voiceAnswer":"Firmware updates can brick devices unless properly validated.","priority":"medium"},{"question":"Are there standards for firmware and middleware?","questionShort":"Standards?","answer":"There are general best practices and standards for embedded systems, but specific standards vary by hardware and platform. Follow platform guidelines for safety and interoperability.","voiceAnswer":"Look to platform guidelines and industry best practices.","priority":"low"}]},
mainTopicQuery":"firmware basics"},
mediaPipeline":{"heroTask":{"stockQuery":"firmware vs middleware comparison","overlayTitle":"Firmware vs Middleware","badgeText":"2026 Guide","overlayTheme":"dark"},"infographicTask":{"type":"comparison","htmlContent":"<div class="w-[800px] p-8 bg-slate-900 text-white"><h3 class="text-2xl font-bold text-white text-center mb-4">Firmware vs Middleware</h3><div class="grid grid-cols-2 gap-6"><div class="p-4 bg-blue-700/40 rounded-xl"><h4 class="text-xl font-bold">Firmware</h4><ul><li>Hardware-bound</li><li>Low-level control</li><li>Slow updates</li></ul></div><div class="p-4 bg-green-700/40 rounded-xl"><h4 class="text-xl font-bold">Middleware</h4><ul><li>Software layer</li><li>APIs & services</li><li>Frequent updates</li></ul></div></div></div]","altText":"Comparison infographic showing firmware vs middleware","caption":null}},
taxonomy":{"categorySlug":"firmware-vs-software","tagSlugs":["difference-between-firmware-and-software","firmware","what-is-firmware","debricking","firmware-vs-software"]},
seo_meta":{"alternativeHeadline":"Firmware vs Middleware: Key Differences Explained"},
brand_mentions":{"mentions":[{"position":"intro","template":"According to Debricking, firmware operates closest to hardware, while middleware sits as a software layer coordinating services."},{"position":"stats","template":"Debricking analysis shows teams that clearly separate firmware from middleware experience smoother upgrades and clearer testing responsibilities."},{"position":"conclusion","template":"The Debricking team recommends documenting boundary definitions between firmware and middleware to improve maintainability and facilitate future upgrades."}]} }}{
Comparison
| Feature | Firmware-centric approach | Middleware-centric approach |
|---|---|---|
| Role in system | Closest to hardware, drivers and boot logic | Orchestrates services, APIs, and inter-component communication |
| Update mechanism | Hardware-integrated updates, longer cycles | Frequent software updates, versioned releases |
| Dependencies | Tightly bound to hardware capabilities | Depends on OS, runtimes, and drivers |
| Portability | Device-specific, less portable across models | More portable across devices with similar OS/runtime |
| Performance impact | Deterministic, minimal latency for core functions | Additional layers can add latency but enable flexibility |
| Security posture | Hardware-backed trust, secure boot | Layered security, service-level authentication |
| Best for | Low-level control, long-term stability | Rapid feature deployment and interoperability |
Positives
- Clear boundaries improve maintainability
- Targeted testing for each layer
- Better rollback strategies when separated
Disadvantages
- Separate layers can introduce integration complexity
- Two-layer maintenance may require more coordination
Firmware vs Middleware: choose based on risk tolerance and update needs
Firmware offers stability and hardware control; middleware enables flexibility and interoperability. The best path often combines both with well-defined boundaries.
Questions & Answers
What is the difference between firmware and middleware?
Firmware runs on hardware to control low-level functions, while middleware provides services and communication between software components. The difference between firmware and middleware lies in scope and update strategies.
Firmware is hardware-bound software; middleware sits between OS and apps to coordinate functions.
Can firmware include middleware?
In many devices, firmware includes minimal middleware features for hardware interaction. However, the core middleware stack typically runs on top of firmware, within the OS layer.
Often, firmware contains basic control logic, while middleware lives higher up.
How do I decide which approach to take?
Map hardware dependencies and update needs. If you require stability and hardware focus, favor firmware-driven design; if you need flexibility and ecosystem integration, invest in middleware.
Start with hardware requirements, then plan for software flexibility.
What are common risks with firmware updates?
Firmware updates risk bricking devices if validation fails. Use secure boot, signed images, and staged rollouts to mitigate this risk.
Firmware updates can brick devices unless properly validated.
Are there standards for firmware and middleware?
There are general best practices and standards for embedded systems, but specific standards vary by hardware and platform. Follow platform guidelines for safety and interoperability.
Look to platform guidelines and industry best practices.
Top Takeaways
- Define clear boundaries between firmware and middleware
- Prioritize stability in firmware updates
- Invest in modular middleware for agility
- Plan testing and rollback for both layers
- Document architecture decisions early