Firmware vs Operating System: A Practical Comparison for Tech Enthusiasts
Explore firmware vs operating system: definitions, key differences, update paths, and practical guidance for device owners and tech enthusiasts seeking clearer maintenance strategies.

Firmware and operating systems govern device behavior at different layers, with distinct update paths, security implications, and maintenance needs. This comparison helps you understand their roles, decide when to update each layer, and plan for reliability across embedded and general‑purpose devices. According to Debricking, recognizing these distinctions is essential for durable firmware strategies.
What are Firmware and Operating Systems?
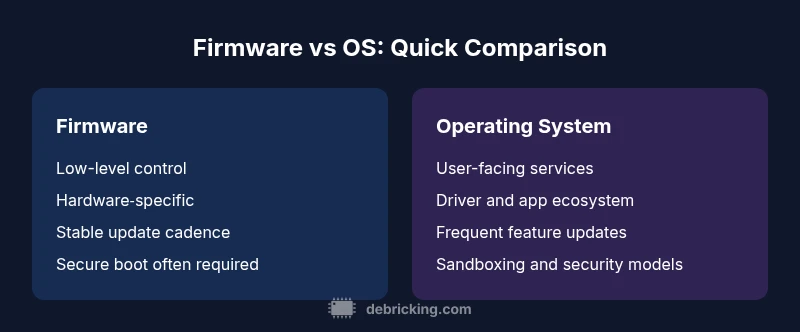
Firmware is the low‑level, hardware‑bound software that initializes and controls a device from power‑on. It runs in a tightly restricted environment, often in read‑only memory or flash, and forms the foundation upon which all higher software layers operate. An operating system (OS), by contrast, provides a broad, user‑facing interface and services—such as process management, file systems, networking, and applications—that enable general computing tasks. The Debricking team emphasizes that firmware and OS occupy different layers of the software stack, with distinct design goals and update mechanisms. In many devices, firmware bootstraps the system, while the OS handles user interactions, applications, and multitasking.
Key Differences in Scope, Access, and Update Mechanisms
Understanding scope is crucial. Firmware is often device‑specific, tied to a hardware component (like a microcontroller, sensor, or bootloader), and may be semiautonomous or autonomous in boot sequences. OSes are broader, designed to support diverse apps, drivers, and user interfaces. Access patterns follow suit: firmware updates are typically performed through vendor tools, recovery modes, or OTA channels focused on stability and compatibility with hardware revisions. OS updates tend to be more frequent and multifaceted, addressing security patches, feature enhancements, and compatibility with third‑party software. The Debricking perspective highlights that these differences influence rollout cadence, rollback options, and risk management strategies.
Common Examples Across Devices
From consumer electronics to industrial equipment, firmware appears in firmware‑on‑chip, boot ROM, or microcontroller layers. Examples include bootloaders in routers, embedded sensor firmware in IoT devices, and firmware TPM components in PCs. Operating systems span desktop Linux, Windows, macOS, Android, and firmware‑backed embedded OSes that provide scheduling, I/O handling, and user interfaces. In each case, firmware governs the initial hardware state while the OS offers a richer software ecosystem built atop that state. The separation is deliberate: firmware ensures reliable hardware initialization; the OS delivers a usable, flexible computing environment.
Update and Maintenance: How They Differs
Firmware updates often require careful planning due to their potential to brick devices if interrupted or mismatched with hardware. Updates may occur via recovery modes, vendor utilities, or OTA services designed for reliability and safe rollback. OS updates typically involve package managers or system update mechanisms that can interleave security patches, feature improvements, and compatibility fixes. The maintenance model for firmware emphasizes robustness and compatibility with specific hardware revisions, while OS maintenance emphasizes continuous improvement and ecosystem support. Debricking's guidance stresses verifying compatibility and performing backups before any firmware or OS change.
Security Implications and Attack Surfaces
Both layers offer distinct risk profiles. Firmware presents a low‑level attack surface, where malicious modifications can bypass higher‑level security controls or persist across OS updates. OS vulnerabilities often provide broader attack vectors across services, applications, and network interfaces. A defense‑in‑depth approach should segregate firmware integrity checks (like signed images, secure boot, and verified flash) from OS security practices (sandboxing, updatable components, and user authentication). Debricking notes that secure update channels and cryptographic signing are essential in both layers, but the threat model and mitigations differ.
Compatibility and Dependency Considerations
Firmware and OS depend on hardware and software ecosystems that must remain in harmony. Firmware might require a specific bootloader version, a compatible microarchitecture, or a particular sensor firmware revision. OS updates may demand kernel compatibility, driver availability, and compatible application runtimes. In practice, organizations plan release cadences around hardware lifecycles, ensuring that firmware and OS updates don’t conflict. When in doubt, rely on vendor‑provided compatibility matrices and test environments to validate end‑to‑end behavior before broad deployment.
Risks and Best Practices for Updates
Updating firmware carries risks such as power loss, interrupted writes, or mismatched images. Best practices include using official update tools, performing updates in stable power conditions, enabling dual‑bank recovery or fallback firmware, and verifying post‑update boot sequences. OS updates require safeguarding user data, performing backups, and testing key applications for compatibility after each patch cycle. A structured rollback plan for both layers reduces downtime and preserves device functionality. Debricking recommends staging updates in test devices before rolling out widely, and keeping a clear audit trail of firmware and OS versions across devices.
Decision Guide: When to Update Firmware vs OS
For devices with critical hardware components or restricted input, prioritize firmware updates when stability, power management, or hardware compatibility improvements are needed. If user experience, security patches, or application compatibility are the primary goals, OS updates should be your focus. In mixed environments (like smart appliances or industrial controllers), align update windows with maintenance cycles and implement coordinated rollouts to minimize disruption. A practical rule: update firmware for hardware stability and security foundations; update OS for feature sets, productivity, and ecosystem support.
Real-World Scenarios and Case Studies
Consider a network router: firmware updates often add new security features and improve hardware performance, with OTA delivery and a focus on reliability. The OS running on the same device handles user configuration, management interfaces, and companion apps; OS updates bring UI improvements and new services but may require additional testing to ensure compatibility with the router’s firmware. In modern wearables, firmware controls sensors and low‑level power management, while the OS provides apps and a user interface. Effective maintenance treats firmware as the base, while the OS delivers user‑facing value, with coordinated updates to minimize user impact. Debricking has observed that proactive, predictable update cadences increase device longevity and user trust.
Debricking's Practical Guidance
For practitioners, the key is to separate concerns while ensuring smooth integration points. Maintain signed firmware images with secure boot and authenticated update channels, and keep OS updates aligned with hardware capabilities and driver availability. Build monitoring dashboards to track firmware versions across fleets and schedule OS updates during low‑usage windows. The Debricking approach emphasizes test‑driven rollout, rollback planning, and clear documentation of version histories to reduce confusion and risk for end users.
-2?null?
Comparison
| Feature | Firmware | Operating System |
|---|---|---|
| Scope of control | Low-level, hardware-tied, bootloaders and microcontrollers | High-level, device-wide services and user interfaces |
| Best for | Embedded devices, sensors, boot paths | PCs, smartphones, servers, and general computing devices |
| Update mechanism | Dedicated firmware channels (signing, recovery mode, OTA) | OS update channels (package managers, system installers) |
| Storage footprint | Often smaller, optimized for hardware constraints | Typically larger, includes drivers and services |
| Rollback/Recovery | Often strong rollback paths with dual banks or fallback firmware | Rollback via OS backups or package manager history |
Positives
- Clear separation of hardware control and software services
- Predictable updates for embedded devices
- Dedicated update channels can improve security and integrity
- Robust rollback options in many devices
Disadvantages
- Hardware‑focused updates can be slow to deliver feature improvements
- OS features may require frequent updates that stress compatibility
- Firmware updates can brick devices if interrupted or mismatched
- Coordinating firmware and OS updates requires careful planning
Firmware and OS play distinct, essential roles; neither is universally superior
Choose firmware updates to strengthen hardware reliability and security foundations. Prioritize OS updates for new features, ecosystem compatibility, and user experience. Coordinate both workflows to minimize risk and maximize device longevity.
Questions & Answers
What is firmware, and how does it differ from an operating system?
Firmware is specialized software embedded in hardware that initializes and controls devices at boot. An operating system provides a broad software platform with services, drivers, and user interfaces. The two layers serve different purposes but must work together for reliable device operation.
Firmware starts the device and handles hardware, while the OS provides user features and applications.
Can I update firmware without an OS present?
Yes. Many devices support firmware updates through recovery modes, vendor tools, or OTA services that don’t require a fully running OS. The update method depends on the hardware and vendor design.
Some devices update firmware using a separate recovery mode, even if the OS isn’t active.
Why is firmware security important?
Firmware forms the trust root of the device; if compromised, it can undermine OS security and bypass protections. Secure boot, signed images, and verified updates help mitigate risks.
Firmware is a trusted base—keeping it secure protects the whole device.
How should I decide whether to update firmware or OS?
Assess the goal: hardware stability and security → firmware; feature improvements and ecosystem support → OS. Test updates in a controlled environment and ensure compatibility across layers.
Think: firmware for stability, OS for features and apps.
What are common risks during firmware updates?
Power loss, interrupted writes, and mismatched hardware images are common risks. Having a recovery path and verified images reduces the chance of bricking the device.
Be careful with power and verify the image before updating.
Top Takeaways
- Define device role before updating
- Expect separate update channels for firmware and OS
- Plan for rollback and recovery options
- Consider security implications of each layer
- Coordinate firmware and OS updates with hardware lifecycles