Difference Between Firmware and Operating System
Explore the difference between firmware and operating systems with practical guidance, real-world scenarios, and safe update practices for embedded devices and consumer hardware.
The difference between firmware and operating system lies in their roles and where they live in a device. Firmware is persistent, hardware-level software stored in non-volatile memory that boots the device and handles basic control. An operating system, by contrast, sits above firmware to manage resources and run applications. In practice, firmware updates fix hardware behavior, while OS updates add features and security layers.
What firmware is and where it sits in the device
Firmware is specialized software embedded directly in hardware, stored in non-volatile memory such as flash or ROM. It boots first, runs the initial hardware checks, and establishes the basic control loops that let a device operate. Because firmware sits so close to the hardware, it typically has tight resource constraints and a minimal runtime, yet it must be highly reliable. The difference between firmware and operating system becomes crystal clear when you consider orchestration: firmware handles the foundational bootstrapping and low-level control, while the OS provides the broader software environment. According to Debricking, this layering matters for security, reliability, and update strategies. On many devices you’ll find firmware in microcontrollers, network interfaces, or embedded controllers, each with its own update mechanism and verification steps. Understanding this layering helps you plan maintenance, prepare for safe updates, and avoid bricking a device due to power loss or interrupted flash writes.
From a practical standpoint, think of firmware as the device’s nervous system at boot time, whereas the OS is the cognitive layer that interprets inputs, runs apps, and provides user-facing features. In this sense, the firmware determines what hardware can do at its most fundamental level, and the OS determines what users can do with the device once it is up and running.
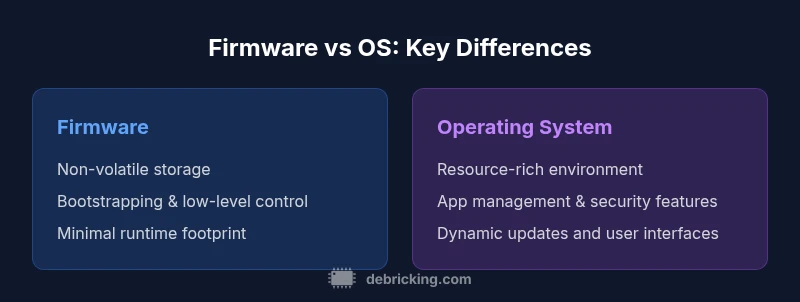
Core architectural differences: firmware vs OS
Firmware and operating systems occupy distinct layers of a device’s software stack. Firmware is typically tightly coupled to the hardware it controls, containing the bootloader, initialization routines, and low-level drivers. It runs with limited memory and processing power, often in real-time environments, and its updates are usually vendor-signed and verified to avoid bricking hardware. An OS, in contrast, is a software layer that manages resources, schedules tasks, provides APIs, and runs applications. It includes a kernel, drivers, system libraries, and user-space processes. The OS abstracts hardware details behind well-defined interfaces so developers can build complex features without directly handling every hardware quirk. This separation between firmware and OS helps explain why devices with embedded systems often see firmware updates as a separate, more conservative activity, while OS updates are more frequent and user-facing. For testing and maintenance, this difference matters: firmware updates require careful power management and rollback plans, while OS updates benefit from rollback mechanisms and package-level verifications.
In many devices, the boundary is fuzzy. Some systems run an embedded OS with minimal components or even a microkernel approach that blurs lines with firmware. Nonetheless, the principle remains: firmware bootstraps hardware and establishes a baseline, while the OS builds a flexible, extensible software environment that users interact with daily.
Update mechanisms and lifecycles
Firmware updates and OS updates follow different lifecycles and risk profiles. Firmware upgrades are typically smaller in scope but higher risk if interrupted, because they modify the code that starts the device and controls critical hardware pathways. Most manufacturers require a controlled environment to perform a firmware update—often using a dedicated tool, a recovery mode, or a secure boot workflow that verifies the image before flashing. In many cases, there is a non-trivial failure risk if power is cut mid-flash, which is why devices may include dual-bank flash, recovery partitions, or hardware watchdogs. OS updates, by contrast, are often delivered via OTA or a package manager and can be incremental. They update numerous libraries, drivers, and sometimes the kernel, and they typically include rollback options if something goes wrong. The practical takeaway is to treat firmware updates with heightened caution and ensure a reliable power source, while OS updates can be scheduled and tested more flexibly. This division influences how users plan maintenance windows, backups, and device availability during updates.
From a security perspective, the update process is a critical attack surface. Firmware integrity directly affects boot safety and core functionality, while OS integrity affects application security, user data protection, and system stability. Debricking emphasizes ensuring that both update channels are authenticated and audited to mitigate supply chain risks and prevent unauthorized changes to either layer.
Security implications and reliability
Security considerations differ between firmware and the OS. Firmware is often the first line of defense, containing boot code, bootloaders, and hardware drivers. A vulnerability at this level can enable persistence and deep compromise because it operates before higher-level protections. Consequently, firmware security relies on secure boot, signed update images, and validated flash writes. Reliability hinges on a robust recovery mechanism; if a firmware update fails, devices may become bricked. The OS contributes security features at a higher layer, including user authentication, sandboxed processes, and memory protection. OS updates can patch kernel vulnerabilities, strengthen cryptographic libraries, and improve secure communication with peripherals. In modern devices, the best practice combines a cryptographically signed firmware chain with a hardened OS, ensuring multiple layers of defense. Debricking’s guidance is to minimize the exposure of firmware attack vectors and to maintain a resilient update path that includes recovery options and clear rollback procedures.
Practical security planning also accounts for supply-chain integrity, secure configuration, and regular audits of both firmware and OS components. By understanding where these layers live and how they interact, device owners can implement layered defenses and reduce the risk of cascading failures during updates.
Real-world scenarios and examples
Consider a smart thermostat: its firmware governs the sensors, microcontroller, and basic network connectivity, while a lightweight OS or real-time scheduler may run to handle scheduling, user interfaces, and app logic. A router often separates a firmware image that controls the core networking stack from a separate management interface served by an embedded OS. A modern smartphone blends both concepts: the bootstrap firmware ensures the device can power up and verify the secure boot chain, while the operating system handles applications, notifications, and media. In industrial equipment, firmware may manage motor control loops and safety interlocks, with an OS or real-time OS providing scheduling, diagnostics, and higher-level coordination. Even BIOS and UEFI firmware in PCs function as the first stage to initialize hardware and boot the operating system, illustrating how firmware and OS are complementary rather than mutually exclusive. When evaluating a device, identify whether critical boot-time behavior is governed by firmware, and whether user-facing functionality is delivered by an OS. This helps determine update strategies, risk tolerance, and long-term maintenance plans.
In all these examples, the boundary between firmware and OS is context-dependent. Some devices ship with a mid-layer that blends firmware logic with resident software, while others keep a strict separation. Recognizing how each layer contributes to reliability, security, and user experience is essential for engineers, IT professionals, and enthusiasts who maintain devices over time.
Practical guidance: how to determine what's on your device
To determine what part of your device runs firmware versus an OS, start with a model and vendor documentation. Look for terms like firmware version, BIOS/UEFI version, bootloader, kernel, and system image. Tools such as device management interfaces, boot logs, and hardware diagnostics can reveal which components are loaded at boot and what modules are responsible for core functionality. When planning updates, confirm the official upgrade path and verify the integrity of the image with cryptographic signatures. Create a recovery plan in case an update fails, which may involve a recovery mode, a secure fallback image, or a service center visit for hardware-level re-flashing. For embedded devices, maintain a change-log that specifies firmware revisions and OS patches, as well as a rollback strategy if user-facing features regress after an update. Understanding how to read version strings and update notes helps you assess risk and determine whether a device requires a firmware-only update, an OS patch, or both. In practice, proactive maintenance reduces downtime and minimizes the chance of hardware degradation over time.
Authority sources and best practices
To stay aligned with industry guidance, consult official vendor documentation and established testing frameworks. When researching the distinction between firmware and operating systems, reputable sources emphasize secure boot, signed updates, and layered defense strategies. This section also includes references to broader literature and standards that govern firmware integrity and OS security. Always prioritize official channels for updates and maintain a tested rollback plan before applying changes to critical devices.
Comparison
| Feature | Firmware-based device | Operating-system-driven device |
|---|---|---|
| Persistence | Non-volatile firmware storage (ROM/flash) | Non-volatile OS image plus apps |
| Role | Low-level hardware bootstrapping and control | User-facing services and app management |
| Resource needs | Minimal CPU/RAM, optimized for microcontrollers | Larger CPU/RAM, multi-core, virtualization |
| Update scope | Firmware updates modify boot/initialization code | OS updates modify system libraries, apps, kernel |
| Typical use cases | Embedded devices, sensors, appliances | Smartphones, PCs, devices with rich apps |
| Security model | Firmware integrity is critical; updates are cautious | OS-level security with sandboxing and permissions |
| Interfaces | Vendor-specific bootloaders and interfaces | Standard OS APIs, drivers, and user interfaces |
Positives
- Clear separation of hardware and software responsibilities
- Reliability through minimal boot paths
- Longer device lifespan with stable firmware foundations
- Focused update channels reduce risk
Disadvantages
- Limited user-space capabilities on firmware-first devices
- Vendor-specific update processes can be brittle
- Lower flexibility for on-device experimentation on firmware-heavy platforms
Firmware-first designs excel in reliability, while OS-based designs offer richer functionality and user experience
If your priority is hardware stability and long-term reliability, firmware-centric devices are ideal. If you need broad software features and user applications, OS-driven devices win for versatility.
Questions & Answers
What is firmware?
Firmware is specialized software embedded in hardware, stored in non-volatile memory, that boots the device and handles fundamental hardware control. It runs before the operating system and is often tightly coupled to the device's components.
Firmware is the hardware-close software that runs first when a device starts, before any apps.
What is an operating system?
An operating system is a software layer that manages hardware resources, runs applications, and provides services like networking and security. It sits above firmware, offering a richer environment for software and user interaction.
An OS manages hardware resources and runs applications, sitting above firmware.
Can a device have both firmware and an OS?
Yes. Most devices start with firmware that initializes hardware, then load an operating system to support apps and user-level features. In some cases, a minimal OS is embedded directly in flash alongside firmware, blurring the boundary.
Yes, devices can have firmware at boot and an OS for everyday use.
How do firmware updates differ from OS updates?
Firmware updates tend to be smaller, more tightly scoped, and riskier if interrupted since they affect boot and core hardware control. OS updates are larger, more modular, and often come with rollback options, focusing on security patches and feature changes.
Firmware updates fix boot code and hardware control; OS updates patch features and security.
What are common risks when updating firmware?
The main risks are bricking the device if power fails during flash and validating integrity of the new image. Always use official tools, ensure power stability, and have a recovery plan.
Power loss during flashing can brick firmware; use official tools and ensure power.
How can I safely update firmware on a device?
Follow vendor instructions exactly, use a stable power source, verify the firmware image signature, and perform updates in a controlled environment. Keep backups where possible and test the device after update before putting it back into production use.
Use official update tools, verify signatures, and test after updating.
Top Takeaways
- Firmware provides low-level boot control
- OS enables feature-rich user environments
- Update scope and risk differ between layers
- Choose based on device goals and use cases