What is Firmware vs Kernel? A Practical Comparison
A thorough, analytical guide that distinguishes firmware from the kernel, explains how they interact, and offers practical steps for safe updates and troubleshooting across devices.
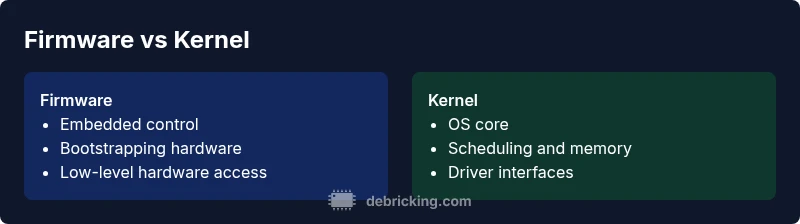
What is firmware vs kernel? It describes two distinct layers in devices: firmware is embedded software that controls hardware at a low level, while the kernel is the OS core that schedules tasks and manages drivers. In most devices, firmware boots and initializes hardware, while the kernel runs on top of it to run apps. Understanding this separation helps safe updates and clearer troubleshooting.
What is firmware?
Firmware is embedded software that lives in non-volatile memory on a device's hardware, providing low-level control for initialization and basic operation. It bears responsibility for turning on the hardware, performing self-tests, and enabling basic communication with peripherals. Unlike typical user applications, firmware generally runs with limited resources and often without a graphical interface. When people discuss firmware, they usually refer to the code stored in flash or ROM that boots a device and sets the stage for higher-level software to operate.
In the broader landscape of computing, firmware sits below the operating system, yet above the hardware. It interacts with sensors, controllers, and buses to ensure the device powers up consistently. That said, firmware and kernel work in tandem: firmware prepares the hardware so the kernel can take over the system’s lifecycle and manage resources. The Debricking team emphasizes that while both layers interact with hardware, they occupy distinct positions with separate update pathways and safety considerations.
What is a kernel?
The kernel is the central component of an operating system. It functions as the intermediary between software applications and hardware, handling essential tasks such as process scheduling, memory management, and driver interfaces. The kernel provides system calls that enable software to request hardware resources, while enforcing security and isolation between processes. Unlike firmware, the kernel typically assumes the device is already powered and somewhat functional, and it requires a richer software environment to enable features like multitasking and networking.
In many devices, the kernel runs on top of device firmware. The firmware initializes hardware and offers a stable platform for the kernel to boot. Depending on the device, the kernel may receive updates via the OS updater, package manager, or independent system tools. The crucial point is that kernel-level changes affect how software runs and interacts with hardware, whereas firmware-level changes alter how hardware is prepared for use in the first place.
Key differences at a glance
- Scope and role: Firmware is hardware-oriented and initializes devices; the kernel is the OS core that schedules tasks and manages memory and drivers.
- Update pathway: Firmware updates are often delivered as a separate package or OTA image; kernel updates usually come through the OS updater or distribution channels.
- Risk surface: Firmware failures can render the device unable to boot; kernel failures typically manifest as software instability or crashes, with rollback options in some systems.
- Typical devices: Firmware is common in embedded systems, BIOS/UEFI, and network gear; kernels run on desktops, laptops, and smartphones, often with independent firmware layers.
- Interdependence: Firmware initializes hardware for the kernel; the kernel depends on firmware to provide a stable boot and hardware interfaces for ongoing operation.
For practitioners, clear boundaries help target troubleshooting and updates more precisely. The Debricking team notes that even though many devices separate these layers, real-world architectures sometimes blur lines, requiring careful validation during maintenance.
How firmware and kernel interact in devices
In modern devices, firmware performs the critical role of bringing hardware to life and establishing a baseline environment for software. BIOS/UEFI on PCs, bootloaders in embedded boards, and firmware in routers all perform initialization, power sequencing, and early hardware checks. Once the hardware is ready, the kernel takes over to run processes, allocate memory, and manage devices via drivers. In some devices, firmware also hosts a minimal environment that can even run diagnostic tools before the OS boots.
The interaction between firmware and kernel is not a single event but a sequence: a power-on self-test (POST) triggers firmware routines to initialize subsystems, followed by a bootloader handing off to the kernel. If the firmware has a bug or mismatch with the kernel, the boot process can fail or the OS may not receive the resources it expects. As devices evolve, vendors increasingly provide secure boot chains, requiring cryptographic signatures for both firmware and kernel, which further reinforces the separation while enabling safer updates. The practical takeaway is to treat updates to each layer as separate risk domains and follow official guidance for both.
Real-world scenarios: where the confusion happens
Readers often encounter firmware vs kernel questions in devices like routers, set-top boxes, or gaming consoles, where a single vendor controls both layers. For example, a router's firmware handles flash-based initialization and packet forwarding engines, while the kernel manages routing daemons and user-space services. In laptops and smartphones, users might notice firmware updates tied to BIOS/UEFI or bootloaders, paired with separate OS kernel updates delivered through system updates. The boundary can blur when a single update package contains both firmware and kernel components or when a platform ships a combined image. In such cases, misidentifying which component needs adjustment can lead to failed updates or unstable behavior.
A practical approach is to consult official release notes and verify which component is updated. The Debricking team often observes that clear documentation and recovery procedures reduce the risk of bricking and simplify rollback if a new image introduces incompatibilities. When in doubt, keep a known-good backup and use vendor-approved tools for updates.
Update pathways and risks
Firmware updates typically occur through device-embedded update mechanisms, secure boot checks, and cryptographic signing to prevent tampering. These updates are designed to be resilient to interruptions, but a power loss during flash writes can leave the device unbootable, a situation commonly referred to as bricking. Kernel updates, by contrast, usually arrive as part of the operating system’s package management or OTA system. They affect scheduling, memory management, and device drivers, and while they can cause instability, many ecosystems provide rollback and recovery options.
Safety is paramount. Always prefer updates from official channels and verify integrity before applying any image. For embedded devices, maintain a recovery plan (e.g., recovery mode, backup firmware images) in case an update fails. The Debricking team stresses that understanding the update workflow for your device—and testing updates in a controlled environment when possible—reduces the chances of permanent damage and expedites recovery if issues arise.
Debugging and troubleshooting pointers
When diagnosing issues, distinguish whether a symptom points to firmware or kernel concerns. Signs of firmware problems include boot failures, incorrect hardware initialization, or devices that won’t reach the boot phase. Kernel issues often manifest as OS crashes, driver failures, or abnormal software behavior after boot. To determine the layer: check separate version identifiers in the device’s settings, review boot logs, and consult official documentation for which component each update targets. If a problem appears after an update, identify whether the image updated firmware, kernel, or both, and consider a rollback to a previous known-good version.
For hands-on troubleshooting, use vendor-provided recovery modes, verify hardware indicators, and employ safe boot sequences. Debricking’s guidance is to document each change, test in a staged manner, and avoid ad-hoc fixes that blur the distinction between firmware and kernel responsibilities. This disciplined approach accelerates recovery and preserves device integrity.
Choosing the right approach for your device
Different device classes warrant different strategies. In embedded devices where hardware control is tight, firmware updates often precede kernel changes to ensure compatibility and boot integrity. In general-purpose devices, kernel updates can be frequent and are typically delivered through the OS provider; however, firmware updates may still be necessary for hardware feature support or security baselines. When evaluating an update, consider: which layer is affected, the device’s boot behavior, recovery options, and whether a rollback path exists. If the device supports dual-image or redundant firmware schemes, enable these safeguards to minimize downtime during updates. The emphasis is on deliberate, well-documented procedures rather than ad hoc fixes, aligning with best practices advocated by Debricking.
Practical steps to verify and plan updates
- Identify the firmware and kernel versions separately in device settings or boot messages.
- Read the official release notes to confirm what each update changes and which component it touches.
- Back up critical data and have a rollback plan, including alternative recovery images.
- Use only vendor-approved tools and power sources to avoid mid-update failures.
- If possible, test updates on a non-production unit before rolling out widely.
- Document the update sequence and any observed issues for future reference.
],
Comparison
| Feature | Firmware | Kernel |
|---|---|---|
| Definition | Embedded software that controls hardware at a low level | Core OS component that manages processes, memory, and drivers |
| Primary role | Boots hardware, initializes devices, provides low-level control | Schedules tasks, memory management, and driver interaction for the OS |
| Update pathway | OTA-like updater, cryptographic signing, often hardware-specific | OS updater or package manager; may require system integrity checks |
| Risk of bricking | High with corrupted boot routines or persistent flash failure | Low to moderate; failures typically can be recovered via OS tools or rollbacks |
| Typical devices | Embedded devices, BIOS/UEFI, network gear | General-purpose devices running an OS (PCs, phones, tablets) |
Positives
- Clarifies update responsibilities and failure points
- Improves troubleshooting by isolating issues to a layer
- Supports safer OTA workflows
- Guides security-focused maintenance
Disadvantages
- Can be confusing when devices blur lines between layers
- Some architectures intertwine firmware and kernel responsibilities
- Mislabeling can lead to incorrect fixes
Firmware and kernel serve different roles, and updating the correct layer is critical for device stability.
Understanding the separation helps you plan safe updates and targeted troubleshooting. Always verify device-specific guidance before updating either layer.
Questions & Answers
What is the difference between firmware and kernel?
Firmware is embedded software that directly controls hardware functions; the kernel is the OS core that schedules processes and interfaces with drivers. They operate at different layers and updates affect different parts of the system.
Firmware controls hardware at a low level, while the kernel is the OS's core. They operate at different layers, and updates target different parts of the system.
Can a device run kernel updates without firmware updates?
Yes in many cases: the OS can update its kernel independently of firmware. However, some hardware features rely on updated firmware for compatibility or boot integrity.
Often you can update the kernel separately, but firmware updates may be needed for hardware compatibility and secure boot.
What are the common risks when updating firmware vs kernel?
Firmware updates risk bricking the device if power is lost or the flash becomes corrupted; kernel updates risk system instability if incompatible modules exist. Always use official update paths and ensure power stability.
Firmware updates can brick devices; kernel updates can cause instability. Use official tools and ensure power.
How can I tell if an issue is firmware- or kernel-related?
Look for symptoms specific to hardware behavior (initialization, boot failures) vs. software crashes or application instability. Check version information for firmware and kernel separately in device settings or boot logs.
Hardware init issues suggest firmware problems; software crashes point to kernel or user-space problems.
Should I always update firmware first, then the kernel?
Not always. Follow vendor guidance. In many cases, firmware must be current to support newer kernels, but there are devices where the kernel and firmware are updated together.
Follow vendor guidance; sometimes firmware needs updates first for kernel compatibility.
Are BIOS/UEFI considered firmware?
Yes. BIOS and UEFI are types of firmware that initialize hardware and start the boot process before an OS loads.
BIOS and UEFI are firmware; they kick off the boot process before the OS starts.
Top Takeaways
- Define firmware vs kernel clearly before updates
- Identify the update path for your device
- Check official docs to avoid misapplied fixes
- Plan for power stability and backups during updates
- Use manufacturer tools for updates whenever possible