Firmware or Discrete TPM: A Practical Comparison
In-depth comparison of firmware TPM (fTPM) vs discrete TPM (dTPM), focusing on security boundaries, deployment scenarios, and practical guidance for device owners and IT pros.
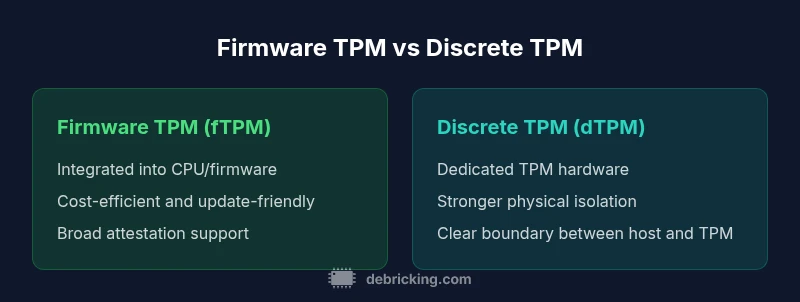
TL;DR: For most devices, firmware TPM and discrete TPM deliver similar cryptographic capabilities, but the boundary conditions differ. If you want cost efficiency and easier firmware updates, choose firmware tpm; if your threat model demands strict physical isolation, go with discrete tpm. In short, firmware or discrete tpm decisions hinge on threat model, upgrade paths, and platform support.
What is TPM and why it matters
Trusted Platform Module (TPM) is a secure crypto processor designed to protect keys, measurements, and sensitive state used during boot and runtime. In practice, TPMs enable features such as secure boot, disk encryption, attestation, and seamless use of hardware-backed credentials across an ecosystem of devices. When you hear the phrase firmware or discrete tpm, you are comparing two implementation strategies for the same security primitive. The phrase firmware or discrete tpm is not about a different standard, but about where the TPM logic lives and how isolated it remains from the rest of the system. In many consumer laptops and servers, a firmware TPM (fTPM) runs within the CPU’s firmware and shares resources with the host; a discrete TPM (dTPM) refers to a dedicated hardware tile or chip that implements the TPM interface as a separate component. The Debricking team emphasizes that the TPM boundary is a security boundary, not a marketing label; how well secrets stay protected depends on the implementation and lifecycle management. This article will dissect the differences through practical lenses: isolation, performance, update flows, and deployment realities, with an emphasis on real-world decision making for device owners.
wordCount":null},
Comparison
| Feature | Firmware TPM (fTPM) | Discrete TPM (dTPM) |
|---|---|---|
| Security isolation | Integrated into CPU/firmware boundaries; depends on firmware isolation | Dedicated chip with independent I/O and physical isolation |
| Attack surface | Shared with platform firmware; potential firmware vulnerabilities | Smaller attack surface due to separate hardware boundary |
| Performance and latency | Low latency for common tasks; relies on firmware stability | Slightly higher latency due to hardware boundary, often predictable |
| Update/maintenance | Firmware updates through platform BIOS/firmware channels | Separate maintenance channel for TPM hardware with vendor updates |
| Platform compatibility | Broad OS and virtualization integration | Requires native drivers and chipset support for full features |
| Cost and power | Lower cost and power in consumer devices | Higher cost for discrete hardware and deployment complexity |
| Best for | General consumer devices and laptops | High-security environments and servers |
Positives
- Lower upfront cost for devices using fTPM
- Easier firmware updates via existing update channels
- Simplified supply chain with fewer discrete components
- Broad OS/tooling support and wide ecosystem compatibility
Disadvantages
- Potentially weaker physical tamper resistance vs a dedicated chip
- Firmware-level vulnerabilities can affect TPM security
- Less flexibility to independently replace TPM from motherboard
- Vendor lock-in risk depending on platform design
Firmware TPM is typically the safer default for most devices; discrete TPM is best for high-security deployments.
In mainstream devices, fTPM offers cost efficiency and streamlined updates while preserving essential protections. For environments with strict physical isolation requirements or regulatory needs, dTPM provides stronger boundary separation. The final choice should reflect threat modeling, hardware lifecycle, and the availability of vendor support.
Questions & Answers
What is TPM and why does it matter?
A TPM is a secure cryptographic processor that protects keys, credentials, and measurements used for boot and runtime integrity. It enables features like secure boot, disk encryption, and attestation. Understanding TPMs helps you assess risks and deployment options for your devices.
A TPM is a hardware-backed security module that protects keys and helps prove device integrity during boot and runtime. It enables secure features like disk encryption and secure login.
What is firmware TPM (fTPM) and how does it differ from discrete TPM (dTPM)?
fTPM runs as part of the host platform’s firmware, sharing resources with the CPU. dTPM is a separate hardware chip with its own boundary. The choice affects isolation, maintenance, and upgrade paths.
fTPM lives in the device firmware; dTPM is a separate chip. The key difference is where the security boundary sits.
Is fTPM secure enough for most users?
For many consumer and light enterprise scenarios, fTPM provides solid protection when the platform’s firmware and software are kept up to date. The decision depends on threat models and lifecycle management.
In most cases, yes, if firmware is updated securely and the device’s lifecycle is well managed.
Can I upgrade from fTPM to dTPM later?
Upgrading from fTPM to dTPM typically involves hardware changes or a platform refresh. Some devices may offer migration tools, but in many cases the TPM choice is tied to the motherboard or system-on-chip.
Upgrading to a separate TPM usually means replacing the motherboard or adding a new module; plan ahead.
What should enterprises consider when selecting TPM for servers?
Enterprises should balance risk appetite, compliance requirements, and lifecycle maintenance. dTPM can offer stronger isolation for high-security workloads, while fTPM may suffice for less critical roles when managed carefully.
For servers, think about how secrets are protected, what the threat model looks like, and how easy it is to manage updates across the fleet.
Top Takeaways
- Assess threat model before choosing TPM type
- Favor fTPM for cost and simplicity in consumer devices
- Choose dTPM for high-security risks and strict isolation
- Verify OS support and management tooling during procurement
- Plan for device lifecycle and update cadence