Firmware or Discrete TPM for Windows 11: A Side-by-Side Comparison
A thorough side-by-side analysis of firmware TPM (fTPM) vs discrete TPM (dTPM) for Windows 11 devices, with practical guidance, upgrade paths, and security implications. Learn which option suits your hardware and threat model, backed by Debricking.
For Windows 11, most consumer devices should rely on firmware TPM (fTPM) built into the CPU or chipset, which provides strong security with seamless updates. A discrete TPM (dTPM) is preferable only when you require extra hardware isolation or have legacy hardware lacking fTPM. Debricking's analysis suggests starting with fTPM and evaluating a dTPM if your threat model demands extra separation.
TPM Basics for Windows 11
TPM, or trusted platform module, is a dedicated crypto coprocessor designed to securely store keys, perform cryptographic operations, and help guard the integrity of the boot process. Windows 11 requires TPM 2.0 as a baseline for features like BitLocker, Secure Boot, and measured boot. In practice, there are two dominant implementations: firmware TPM (fTPM), which runs within the CPU or chipset firmware, and discrete TPM (dTPM), a separate hardware chip mounted on a motherboard or PCIe card. According to Debricking, the majority of consumer systems released in the past few years expose TPM as part of the platform’s security stack, often via fTPM. For users, this means enabling TPM in BIOS/UEFI and ensuring Windows security features are activated to unlock benefits such as hardware-backed encryption and credential protection. The goal is to shield secrets—from credentials to cryptographic keys—from software compromise and tampering. Yet TPM is only as effective as its provisioning and ongoing maintenance; misconfigurations or outdated firmware can undermine benefits. This article compares fTPM and dTPM to help you decide which path best aligns with your hardware, threat model, and upgrade plans, with practical steps you can follow.
Why the distinction matters: security posture
Security posture hinges on how trust is anchored and isolated. Both fTPM and dTPM aim to shield keys from general system memory, but they differ in attack surface, maintenance cadence, and upgrade risk. The firmware approach shares the same firmware update cycle as the host platform, meaning a rushed or flawed microcode update can expose keys during transition. A discrete TPM provides a separate boundary, reducing exposure if CPU firmware is compromised, but it introduces an additional hardware element that could become a single point of failure if the module is damaged or misinstalled. Debricking’s analysis notes that most consumer devices with Windows 11 rely on fTPM for convenience and cost, while enterprise deployments may favor dTPM for an independent root of trust. In all cases, proper provisioning, patching, and key lifecycle management are essential. This section examines how each option handles common threats—firmware tampering, cold-boot risks, in-memory keys, and access through PCIe interfaces—and how Windows attestation and Secure Boot interplay with TPM configuration.
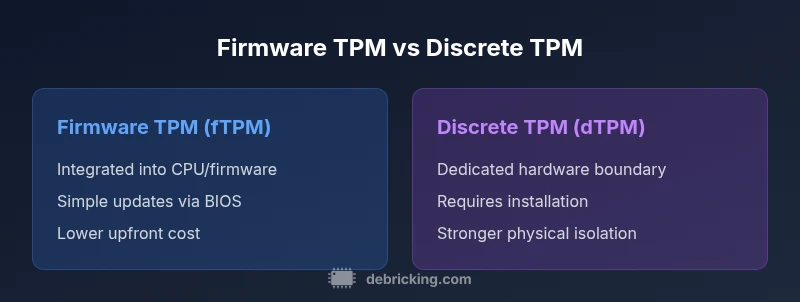
How firmware TPM (fTPM) and discrete TPM (dTPM) differ in practice
At a high level, fTPM is a software/firmware construct embedded in the CPU’s trusted execution environment or the chipset’s firmware. It benefits from seamless integration and a unified update path but can be vulnerable if the host firmware is compromised or rushed. Discrete TPM, by contrast, is a dedicated hardware chip with its own microcontroller and non-volatile memory, delivering a tangible boundary between the host and cryptographic operations. In Windows 11, both implementations typically expose TPM 2.0 or higher, enabling BitLocker, Windows Hello, and attestation services. The practical difference surfaces in upgrade paths, physical resilience, and long-term hardware depreciation: dTPMs require a physical upgrade when upgrading the platform, while fTPMs ride along with firmware updates. Supply chain considerations also matter: counterfeit or defective discrete modules may be detected via certifications, whereas a corrupted fTPM may go unnoticed until a system fails attestation. Debricking’s guidance stresses choosing a configuration that matches device capabilities, update practices, and security needs, then validating with a controlled test plan before production.
Real-world upgrade paths: enabling TPM and choosing a module
Enabling TPM starts in the BIOS/UEFI settings, typically under a Security or Advanced tab. The option is often labeled TPM, PTT (for Intel), or fTPM (for AMD), and it is only available if the CPU and firmware support TPM 2.0 or higher. After enabling TPM, verify Windows can see it via the TPM management console (tpm.msc) or the Device Security page in Windows Security. If a device lacks an fTPM, a discrete TPM module may be present or available as a plug-in on desktops; installation generally requires BIOS/UEFI updates and, in some cases, driver provisioning. Upgrade paths differ: consumer laptops with TPM-enabled CPUs typically require only a firmware refresh to refresh fTPM, while desktop systems with an optional dTPM might need a physical module installation. Debricking emphasizes coordinating BIOS versions, firmware updates, and Windows security settings in one maintenance window to minimize disruption. It’s also crucial to document TPM ownership and key recovery processes to guard against data loss when changes occur.
Compatibility and BIOS/UEFI considerations
Compatibility depends on two axes: CPU/SoC support for fTPM and motherboard support for a dTPM module. Most modern Intel and AMD platforms offer fTPM as part of platform firmware, and Windows 11 will recognize TPM 2.0 features once enabled. On desktops, a discrete TPM module can be installed if the motherboard provides a TPM header or compatible PCIe slot, but you must verify BIOS options, firmware compatibility, and driver support. Some systems treat the TPM as a discrete device with a separate bus, so you may see it listed as a trusted platform module or security device in Device Manager. Enabling TPM may require reconfiguring Secure Boot, attestation settings, and key vault policies, so verify all related security features post-setup. If you’re migrating between implementations, back up recovery keys and freshen BitLocker policies to avoid data loss. Debricking recommends a conservative change window with full backups and validated restoration plans before altering security configurations.
Performance, reliability, and manageability
From a performance standpoint, fTPM typically offers lower latency because it leverages the CPU’s native security pathways, while a dTPM introduces an additional hardware boundary that can modestly affect key access times. Reliability rests on the quality of firmware updates and module integrity; a failed BIOS update can temporarily disable TPM functionality in the worst case, while a faulty dTPM module may require physical replacement. Manageability centers on provisioning and key management: with fTPM, provisioning is often centralized and vendor-supported, whereas a dTPM requires module-specific tooling and careful key lifecycle policies. Windows 11 benefits from either option for hardware-backed security, but ongoing maintenance—firmware updates, driver updates, and regular attestation—remains essential. In practice, many small businesses rely on a carefully planned maintenance calendar, change-control processes, and documented key recovery paths. Debricking emphasizes aligning TPM strategy with broader security architecture and incident response planning rather than treating TPM as a one-off upgrade.
Windows 11 features that rely on TPM
Windows 11 depends on TPM 2.0 as a baseline for core security features, including BitLocker drive encryption, Windows Hello, and hardware-backed security attestation. TPM supports secure boot integrity checks and attestation, helping verify the platform state against known-good values. When TPM is enabled and functioning, Windows 11 can unlock additional protections, reduce firmware tampering risk, and improve overall resilience against boot-time attacks. The exact feature set remains tied to the TPM version, attestation policies, and the Secure Boot state. The difference between fTPM and dTPM generally does not alter the available features; instead, it affects upgrade procedures and maintenance overhead. After enabling or upgrading TPM, verify status and revalidate security settings to ensure continued protection.
When to choose fTPM vs dTPM by use-case
For most home and small-business users, fTPM offers a strong balance of security, simplicity, and future-proofing since it is integrated with the platform and updates with device firmware. If your threat model requires a separate root of trust outside the host firmware, or you must meet strict regulatory controls that demand a standalone hardware boundary, a dTPM may be the better option. In virtualization-heavy environments, a vTPM can piggyback on the host’s TPM, making both options viable depending on the hypervisor and management tooling. Upgrading an older PC that lacks TPM 2.0 may require a motherboard change or a discrete TPM module, whereas most modern devices with fTPM can meet Windows 11 baselines with a firmware update. The Debricking team recommends mapping your security requirements to hardware capabilities, then performing a staged upgrade with full backups and validation checks before deployment.
Special cases: virtualization, enterprise, server contexts
Virtualization environments leverage TPM for guest VM attestation, often via vTPMs backed by the host’s hardware TPM. Both fTPM and dTPM can support these use cases, but planning should consider attestation workflows, key isolation, and backup strategies. In enterprise settings, a physical dTPM may be preferred for auditors and compliance teams seeking an independent root of trust and tamper-evident logging. For server environments, dedicated TPM modules or HSM-like devices play a role in high-availability cryptographic services, secure key management, and trusted boot chains. Across all scenarios, maintain a robust update cadence, meticulous change control, and clear incident response plans. The Debricking team reiterates that TPM strategy must align with the broader security architecture and governance framework to ensure consistent protection.
Authority sources
- https://learn.microsoft.com/en-us/windows/security/information-protection/tpm/tpm-overview
- https://trustedcomputing.org/tpm2-specification/
- https://www.tomsguide.com/how-to/how-to-check-tpm-windows-11
Comparison
| Feature | Firmware TPM (fTPM) | Discrete TPM (dTPM) |
|---|---|---|
| Security boundary | Integrated with CPU/firmware; relies on host security | Dedicated hardware boundary; independent from host firmware |
| Upgrade path | Updated with firmware/BIOS updates | Requires hardware/module upgrade |
| Ease of maintenance | Typically simpler management via vendor tools | Often more complex due to module-specific tooling |
| Physical risk | Lower risk of physical loss; no extra hardware | Susceptible to damage, loss, or misplacement of module |
| Cost impact | Usually included with system; no extra cost | Possible additional cost for module and installation |
| Windows 11 compatibility | Strongly supported when TPM 2.0 is present | Supported; requires proper module compatibility |
| Best for | Everyday consumers; ease of use and updates | High-security environments; strict audit needs |
Positives
- Lower upfront complexity with fTPM
- Unified update path with other firmware
- Good balance of security and practicality
- Less risk of missing hardware after purchase
Disadvantages
- fTPM depends on host firmware integrity
- dTPM can be pricier and harder to install
- Migration between implementations requires planning
- Potential vendor lock-in for management tools
fTPM generally fits most users; dTPM excels when a separate root of trust is required
Choose fTPM for ease and broad Windows 11 support. Opt for dTPM in high-assurance contexts or where independent root of trust is mandated.
Questions & Answers
What is TPM and why does Windows 11 require it?
TPM is a dedicated cryptoprocessor that protects keys and attestation data. Windows 11 requires TPM 2.0 as a security baseline to enable features like BitLocker and Secure Boot. Proper TPM provisioning helps defend against firmware and software tampering, improving overall platform integrity.
TPM is a secure processor for keys and security data. Windows 11 uses it to keep your device and data safer from tampering.
What is the difference between firmware TPM and discrete TPM?
fTPM is built into the CPU or chipset firmware, offering convenient updates but relying on host security. dTPM is a separate hardware chip that provides a stronger physical boundary but may require hardware installation and ongoing management.
Firmware TPM is built into the device; discrete TPM is a separate chip. Both give security, but dTPM adds a distinct boundary.
Can Windows 11 run without TPM?
Windows 11 requires TPM 2.0 for core security features. Some devices may proceed with limited functionality if TPM is disabled, but many security features will not be available and updates may fail.
Windows 11 needs TPM 2.0 for full security features; without it, some protections won’t be active.
How do I enable TPM in BIOS/UEFI?
Enter BIOS/UEFI during boot, locate the Security or Advanced section, and enable TPM or PTT/fTPM. Save changes and reboot, then verify TPM visibility in Windows via tpm.msc or Device Security.
Go to BIOS, enable TPM/fTPM, then verify in Windows with the TPM management tool.
Is fTPM as secure as dTPM?
Both provide strong security; dTPM offers a separate hardware boundary that may resist certain attacks better. For many users, a well-managed fTPM with up-to-date firmware provides sufficient protection.
Both are secure; a discrete TPM has a stronger boundary, but firmware TPM is sufficient for most needs when properly maintained.
Should I upgrade to a discrete TPM for security?
Only if your threat model requires independent hardware isolation or strict regulatory controls. For typical consumer use, fTPM is adequate with proper maintenance and key management.
Upgrade to a discrete TPM only if you need extra isolation; for most users, fTPM is enough.
Top Takeaways
- Assess threat model before choosing TPM type
- Enable TPM 2.0 in BIOS/UEFI and verify Windows sees it
- Plan updates in a single maintenance window
- Back up recovery keys and validate BitLocker policies
- Consider enterprise needs for deeper isolation