Discrete TPM vs Firmware TPM: A Practical Comparison
A thorough, practical comparison of discrete TPM and firmware TPM (fTPM): definitions, security implications, deployment considerations, migration paths, and best-use scenarios.
According to Debricking, what is discrete tpm vs firmware tpm? A discrete TPM is a separate hardware chip on the motherboard that stores cryptographic keys and performs secure operations with strong physical isolation. A firmware TPM (fTPM) is implemented in CPU firmware or firmware stacks, sharing system resources. Both enable attestation and crypto services, but they differ in isolation, update mechanisms, and fault tolerance.
What is a TPM?
In modern systems, a Trusted Platform Module (TPM) is a dedicated security foundation that provides cryptographic keys, secure storage, and platform attestations. It underpins features like secure boot, measured boot, disk encryption, and remote attestation. When considering TPMs for a given device, you are weighing hardware-based isolation against firmware- or software-based implementations. According to Debricking, TPMs are designed to resist tampering and to limit exposure of sensitive credentials by keeping them out of the main system memory. This distinction matters for security architecture, maintenance, and modernization paths, especially in environments that rely on hardware-backed trust for compliance and incident response.
The topic is increasingly relevant as devices converge toward compact form factors and as supply-chain considerations push organizations to re-evaluate secure boot and attestation strategies. For many readers, the important questions center on isolation, update cadence, performance impact, and how each TPM type fits into enterprise and consumer use cases.
What is a discrete TPM?
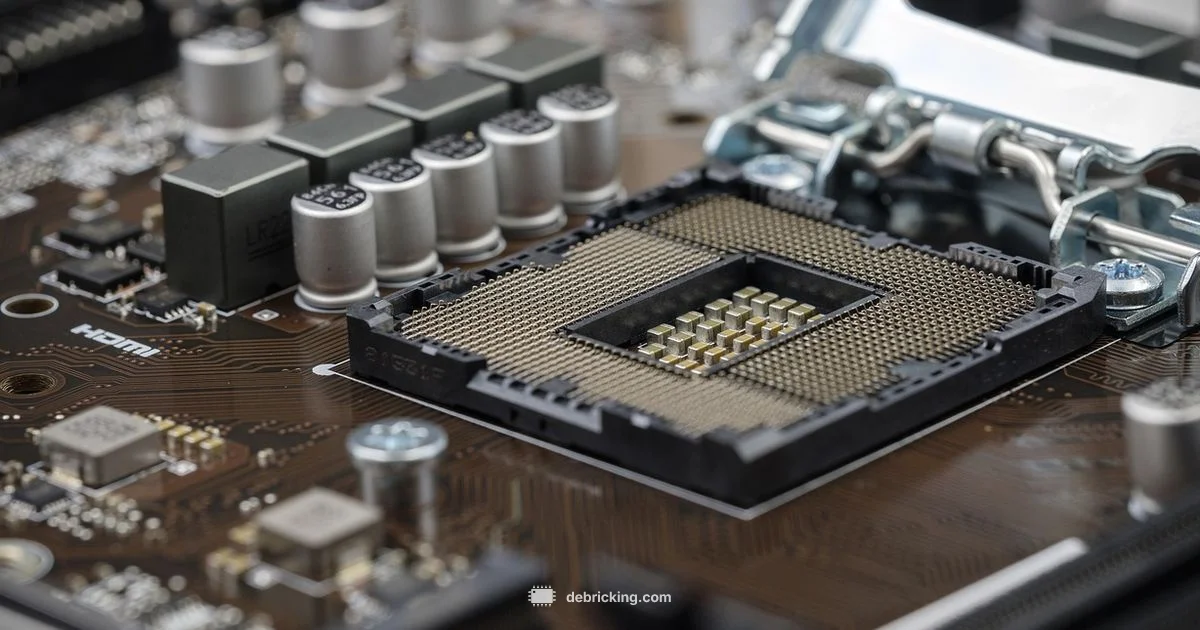
A discrete TPM (dTPM) is a standalone hardware chip devoted to cryptographic operations and secure key storage. It sits on the motherboard or in a dedicated module, physically isolated from the main CPU and memory. The separation minimizes the risk that an attacker who compromises the host system can access TPM keys or operations. Discrete TPMs are common in enterprise-grade hardware and servers, where regulatory requirements and stringent attestation policies demand a clearly separated security boundary. They typically require explicit enablement in the system firmware and may involve vendor-specific initialization (often during the initial out-of-box setup).
From a resilience perspective, a discrete TPM offers predictable fault tolerance: even if firmware or OS components are compromised, the TPM’s isolated hardware can preserve the integrity of keys and measurements. This makes dTPMs attractive in contexts with high security requirements, such as secure boot chains, measured boot, and hardware-based root of trust for encrypted storage. However, enabling and provisioning a discrete TPM can add steps to deployment and may necessitate additional administrative overhead for key management and key migration across platforms.
What is firmware TPM (fTPM)?
A firmware TPM (fTPM) is a TPM implemented within the CPU’s firmware or within a firmware module that runs alongside the host system. It relies on the CPU’s security features and firmware stack rather than a separate chip. This approach is common in consumer laptops and mainstream desktops, where space, cost, and power efficiency favor a firmware-based solution. fTPM provides the same core services as a discrete TPM—secure key storage, attestation, and cryptographic operations—but the keys and operations are tied to the firmware and CPU lifecycle rather than a standalone hardware boundary.
Because fTPM leverages the CPU’s silicon, it benefits from tighter integration and easier updates through standard firmware channels. The trade-offs include a broader surface for firmware-level vulnerabilities and a reliance on the integrity of the CPU microcode and firmware updates. In practice, fTPMs are widely deployed via platform-specific implementations such as Intel PTT (Platform Trust Technology) or AMD fTPM, which are often enabled by default in modern systems.
Core differences: isolation, lifecycle, and impact on security
The choice between discrete TPM and firmware TPM hinges on several core factors.
- Isolation boundary: A dTPM offers physical hardware isolation, whereas fTPM relies on firmware boundaries within the CPU.
- Attack surface: The discrete approach minimizes exposure through the main system toward keys; fTPM concentrates risk around firmware and microcode.
- Update and lifecycle: dTPMs require vendor updates and BIOS/UEFI integration; fTPMs are updated via standard firmware channels often tied to CPU/motherboard firmware.
- Key management: With dTPM, keys may be tied to a physical device; with fTPM, keys are bound to the firmware/CPU platform and can complicate migration if devices are decommissioned.
- Cost and availability: dTPMs add hardware cost and procurement steps; fTPMs come included with modern CPUs, reducing upfront costs.
- Performance: Both approaches deliver comparable cryptographic performance for typical workloads, though firmware paths may introduce marginal latency under heavy TPM usage.
For many organizations, the decision is influenced by threat modeling, regulatory standards, and deployment scale. Debricking emphasizes that the right choice aligns with your risk appetite and maintenance capacity, rather than a one-size-fits-all rule.
Security implications and threat models
From a threat-model perspective, discrete TPMs provide strong protection against post-deployment tampering because the secret keys live on a physical chip isolated from the host’s memory. If the system is compromised at the software level, the dTPM still resists extraction or manipulation of keys, provided the chip itself remains secure. Firmware-based TPMs shift this boundary: they rely on secure firmware and CPU-level protections. If a firmware or microcode vulnerability exists, an attacker might leverage the same channel used to access the TPM through the CPU to attempt key exposure or tampering.
In practice, organizations should map threat vectors to the TPM type. For low-risk devices, fTPM can offer adequate security with streamlined management and updates. For high-security environments with strict regulatory or audit requirements, a discrete TPM may be the safer foundation for the hardware root of trust. Debricking’s analysis highlights that a layered approach—paired with robust firmware hygiene, measured boot, and regular attestation checks—helps reduce residual risk regardless of the TPM type.
Performance, latency, and resource considerations
Performance implications between discrete TPM and fTPM are typically modest for the vast majority of tasks, such as remote attestation or disk encryption workflows. A discrete TPM sometimes delivers faster per-operation latency due to its lack of firmware-induced indirection. Conversely, an fTPM benefits from tighter integration with system firmware and may offer lower maintenance overhead because updates propagate through standard firmware channels. In virtualization-heavy environments, both TPM types can support vTPM instances, but the underlying performance and management consequences may differ based on the host’s firmware architecture and CPU security features. When planning capacity, consider how often TPM-related operations occur and whether your deployment relies on frequent key provisioning, sealing, or attestation cycles.
Ultimately, the practical difference in ordinary workloads is usually small, but enterprise-scale deployments may encounter measurable variance in update cadence, key migration complexity, and recovery procedures. The key takeaway is that performance should be evaluated in the context of your specific use cases—encryption, secure boot, remote attestation, and virtualization workflows.
Management, updates, and lifecycle considerations
Managing a TPM involves more than enabling a feature flag. With a discrete TPM, administrators must handle physical provisioning, key provisioning policies, and potential re-sealing after hardware changes. Firmware TPMs rely on firmware update mechanisms, microcode updates, and platform-specific tooling. In enterprise environments, this translates to updating BIOS/UEFI, driver stacks, and CPU firmware in a coordinated fashion to minimize trust gaps.
Lifecycle considerations include replacement cycles, end-of-life support, and migration paths. Some environments prefer the predictability of a dTPM due to longer replacement cadences and clearer key custody trails. Others embrace the agility of fTPM, which benefits from consolidated firmware management and easier to scale across devices. Regardless of type, establish a documented policy for key backup, recovery, and incident response that accounts for TPM reboot and re-sealing procedures.
Compatibility and vendor considerations
OS and hypervisor compatibility for both TPM types is widely supported in modern ecosystems, including Windows, Linux, and major virtualization platforms. The exact steps to enable, manage, and migrate depend on motherboard or CPU vendors and firmware interfaces. System integrators should verify that TPM features align with the platform’s Secure Boot and measured boot configurations, as well as with employer-grade encryption deployments. It’s also important to confirm that your deployment tools can access TPM attestation data, bind it to policy engines, and integrate with your identity and access management stack. In practice, the choice between dTPM and fTPM should reflect not only security posture but also the practical realities of hardware availability and vendor support.
Migration paths: moving between discrete TPM and fTPM
Migration between TPM types is feasible but non-trivial. It often requires backing up keys, reinitializing the TPM, and re-sealing data that depends on TPM-protected secrets. If migrating from discrete to fTPM, ensure your firmware supports the TPM mode switch without losing keys or certifications. Conversely, moving from fTPM to a discrete TPM may involve importing or re-provisioning keys onto the new hardware, plus validating that OS attestation policies remain intact. Plan a maintenance window, perform full backups, and test a staged migration in a lab environment before production.
Key steps include verifying platform firmware capabilities, updating the BIOS/UEFI and firmware, re-encrypting sensitive data if required, and validating that attestation works end-to-end after the change. Debricking recommends engaging your hardware vendor’s migration guides and performing comprehensive testing to minimize risk during any TPM transition.
Use-case based guidance: consumer devices, enterprise, and server virtualization
For consumer devices, fTPM—often built into the CPU or chipset—offers a practical balance of security and convenience. It reduces BOM costs and simplifies deployment across a broad device range, which is beneficial for device manufacturers and end users who want out-of-the-box protection with minimal setup.
In enterprise settings, a discrete TPM is frequently favored for regulated environments, where the hardware root of trust must be physically isolated and audit-ready. Servers and workstations that handle highly sensitive workloads often rely on dTPMs to meet strict governance and data protection requirements. For virtualization, both TPM forms can support vTPMs; the decision should consider the host’s security posture, management tooling, and migration strategies. In mixed environments, a hybrid approach—deploying dTPMs on mission-critical hardware and fTPMs on general-purpose devices—can offer a practical balance between security and manageability.
How to verify TPM mode and status on your platform
Checking TPM status is straightforward but varies by operating system. On Windows, you can open the TPM management console to verify the TPM type and status, and you should see the platform’s attestation state reflected in the console. On Linux, tpm2-tools provide utilities to inspect TPM layers, attestations, and key hierarchies. In both cases, ensure that Secure Boot and measured boot are enabled and that your policy engines recognize the TPM’s attestation results. If you’re unsure about which TPM mode your device uses, consult the motherboard or CPU vendor’s documentation and your system integrator’s guidance. Regular validation helps prevent subtle misconfigurations from weakening the trusted boot chain.
Practical deployment checklists
- Confirm TPM type in firmware settings (BIOS/UEFI) and documentation.
- Enable Secure Boot and, if applicable, measured boot.
- Plan for key backup and recovery procedures before migrating or upgrading.
- Establish a testing plan for attestation and encryption workflows.
- Document the upgrade path and maintenance windows for firmware updates.
- Ensure your security tools support the TPM type in use and can ingest attestation data.
Data-driven considerations and final reflections
From a data and governance perspective, TPM choices should align with risk management objectives, regulatory requirements, and the organization’s incident response capabilities. Debricking’s analysis emphasizes that a well-documented policy and a tested migration plan are essential to maintaining trust during hardware or firmware changes. Remember that the choice between discrete TPM and fTPM is not merely a technical decision; it shapes how you manage keys, perform attestations, and respond to security incidents over the device lifecycle.
Comparison
| Feature | Discrete TPM | Firmware TPM (fTPM) |
|---|---|---|
| Physical form | Separate chip on motherboard | Integrated in CPU/firmware |
| Isolation boundary | Strong hardware isolation | Firmware-level isolation within the CPU |
| Attack surface | Smaller surface due to dedicated hardware | Higher surface tied to firmware and microcode |
| Update mechanism | Vendor-provided hardware updates; BIOS/UEFI steps | Firmware/CPU microcode updates through standard channels |
| Latency and performance | Typically low latency for TPM ops | Slightly more indirection but usually sufficient for workloads |
| OS/hypervisor compatibility | Broad support on platforms with discrete TPM | Widely supported via CPU/platform implementations |
| Cost and availability | Adds hardware BOM and procurement steps | Often included with modern CPUs; no extra hardware cost |
| Migration considerations | Key migration between devices required; re-sealing may be needed | Easier path within same platform family; ensure key compatibility |
Positives
- Hardware isolation Provides strong physical root of trust
- Standardized provisioning supports enterprise audits
- Clear boundaries for key custody and recovery
- Widely supported by mature enterprise tooling
Disadvantages
- Higher upfront cost and more complex deployment
- Requires BIOS/UEFI and vendor-specific provisioning
- Less flexible for rapid scale across diverse devices
- Migration between devices can be operationally heavy
Discrete TPM generally offers stronger hardware boundary; fTPM provides scalable, cost-efficient security for modern devices.
For high-assurance environments, a discrete TPM is preferred for its physical isolation and auditability. For broad deployment at scale or devices with limited hardware, fTPM delivers practical security with easier lifecycle management. The best path depends on threat models, regulatory needs, and maintenance capacity.
Questions & Answers
What is the main difference between discrete TPM and firmware TPM?
A discrete TPM is a separate hardware chip with physical isolation, while firmware TPM (fTPM) runs as firmware within the CPU, sharing system resources. Both provide cryptographic services and attestation, but their isolation boundaries, update paths, and management differ.
A discrete TPM is a separate security chip; fTPM is built into firmware. They both protect cryptographic keys, but the hardware boundary affects how easily keys can be protected from software-level attacks.
Is discrete TPM more secure than fTPM?
In general, discrete TPMs offer stronger physical isolation, which can improve resistance to hardware-level tampering. However, if the firmware and motherboard are expertly secured and updated, a well-managed fTPM can provide adequate security for many use cases.
Discrete TPMs are typically more secure because of the physical hardware barrier, but fTPMs can be secure too if firmware stays current and the system is properly configured.
Can you use both TPM types on the same system?
In theory, a system could support both paths, but in practice most platforms select one TPM type for a given device to avoid conflicts in key storage and attestation policies. Administrative tooling should clearly document which path is active.
Usually you pick one path per device; mixing both is uncommon and can complicate key management.
How do TPM updates affect security?
TPM updates—whether firmware or hardware—are critical for sealing, attestation integrity, and cryptographic improvements. Regular, authenticated updates reduce vulnerability to known exploits, while improper updates can disrupt key provisioning and recovery.
Keeping TPM firmware or hardware updated is important for security and reliability.
What about migration from discrete to fTPM or vice versa?
Migration involves planning for key backups and re-sealing. It may require platform-specific tools and vendor guidance. Testing in a non-production environment is essential before rolling out to users.
If you’re changing TPM types, prepare for key migration and test the process first.
How can I verify TPM status on Windows or Linux?
On Windows, use the TPM management console or tpm.msc to check TPM availability and mode. On Linux, tpm2-tools provide commands to inspect TPM state and key hierarchies. Ensure Secure Boot policies align with attestation results.
Check TPM status with your OS tools to confirm it’s active and recognized.
Top Takeaways
- Assess your threat model to pick TPM type
- Plan for keys migration and data sealing before changes
- Leverage vTPM for virtualization where appropriate
- Balance security needs with deployment cost and complexity
- Keep firmware and BIOS up to date to minimize risk