Firmware vs Discrete TPM for Valorant: A Debricking Comparison
A thorough, analytical side-by-side guide comparing firmware-based security versus discrete TPM hardware for Valorant Vanguard. Learn how each approach affects security, compatibility, performance, and setup in real-world gaming PC environments.
Firmware-based security and discrete TPM both aim to protect Valorant players from cheaters, but they differ in approach. Firmware updates focus on device-level stability and compatibility, while a discrete TPM provides hardware-backed security that Vanguard can rely on for kernel-level checks. For the topic firmware or discrete tpm valorant, the best choice depends on hardware availability and your willingness to handle BIOS changes.
What do firmware and discrete TPM actually do?
Firmware is the low-level software that initializes hardware and provides a base for all higher-level software to run. In gaming PCs, firmware updates typically come from motherboard or peripheral vendors and can improve stability, fix bugs, and enable features like better power management or secure boot. A discrete TPM (Trusted Platform Module) is a separate hardware component that stores cryptographic keys and performs secure operations in an isolated environment, resistant to software-level tampering. In the context of Valorant and Vanguard, firmware and TPM influence how the system proves its trust state to security checks. According to Debricking, the choice between relying on firmware-based improvements or a discrete TPM depends on your hardware, your tolerance for BIOS/UEFI changes, and how deeply Vanguard's kernel-level checks interact with your setup.
Why this matters for Valorant and Vanguard
Valorant’s Vanguard anti-cheat uses a combination of kernel-level checks and system attestation to verify a trusted computing state. Firmware updates can improve hardware interoperability, stability, and boot-time integrity, which can indirectly support Vanguard’s expectations for a clean boot. A discrete TPM provides hardware-backed storage for cryptographic keys and attestation data, making it harder for software to spoof a trusted state. The central question—firmware or discrete tpm valorant—is really about where you want that trust to live: in software controls that can evolve with updates, or in a tamper-resistant hardware module you own. Debricking’s analysis emphasizes that this choice often hinges on whether your motherboard and CPU include robust TPM capabilities and whether you’re prepared to manage BIOS/UEFI configurations.
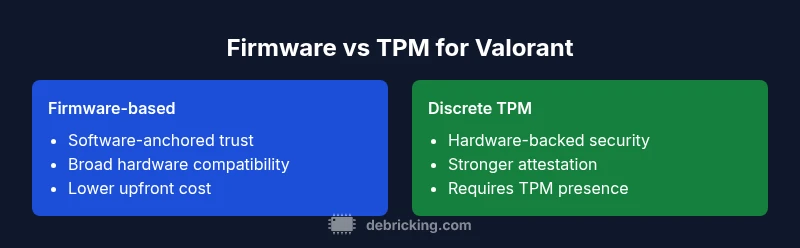
Key differences at a glance
- Security model: Firmware-based approaches rely on software and firmware integrity checks, while discrete TPM relies on hardware-backed keys and attestation.
- Attack surface: Software-based trust can be more vulnerable to driver or firmware flaws; hardware-backed trust reduces exposure to certain software-level cheats.
- Deployment effort: Firmware updates are usually straightforward but may require reboots and compatibility checks; enabling a discrete TPM often involves BIOS changes and driver considerations.
- Longevity and updates: Firmware ecosystems evolve with device vendors; TPM firmware updates are more tightly controlled by TPM vendors and platform manufacturers.
- Best for: If you want broad hardware compatibility and fewer prerequisites, firmware is often preferable; if you want stronger, hardware-backed security with formal attestation, a discrete TPM is compelling.
Compatibility and system requirements
Not all systems ship with a discrete TPM by default. Some motherboards and CPUs include a TPM module or firmware-based TPM support that can be enabled in the BIOS/UEFI. Others may require an add-on TPM chip or a newer platform that includes TPM 2.0 and Secure Boot support. Firmware updates depend on vendor support for your motherboard, GPU, or storage controllers and may require a compatible operating system build. In the context of Valorant, ensuring Secure Boot and platform attestation features are aligned with Vanguard’s requirements can influence whether you lean toward firmware-based trust or TPM-backed trust. Debricking recommends auditing your hardware early: check TPM presence, BIOS/UEFI options, and current firmware revision before deciding on a long-term path.
Performance and user experience considerations
Firmware-level improvements generally incur minimal runtime overhead and tend to affect boot times, driver stability, and firmware-initiated security checks. A discrete TPM introduces limited CPU overhead for attestation tasks but provides benefits in terms of cryptographic key protection and tamper resistance. In practice, both paths should yield similar overall gaming performance, but the perceived stability can differ if a firmware update introduces driver conflicts or if TPM-related BIOS changes affect boot reliability. For players who want a seamless gaming experience with minimal configuration, firmware-focused paths can be preferable; for those who prioritize maximum hardware-rooted security, a TPM-enabled setup offers stronger guarantees, provided the hardware is present and correctly configured.
Real-world scenarios and decision criteria
- If your PC already has TPM 2.0 and modern UEFI features, and you value hardware-backed trust, a discrete TPM path may be appealing, especially for long-term security resilience.
- If your hardware is older or you prefer avoiding BIOS changes, sticking with firmware updates and software-based trust mechanisms can be less risky and faster to maintain.
- For laptop users or compact builds with limited upgrade paths, firmware updates to firmware components (BIOS/EC/firmware) are often the most practical route to maintain compatibility with Vanguard checks.
- Consider your risk tolerance: hardware-backed trust is generally harder to spoof, but it comes with configuration requirements and potential vendor limitations.
- Debricking guidance recommends mapping out a practical upgrade plan that accounts for hardware availability, vendor support timelines, and your own comfort with BIOS/UEFI configuration.
How to verify your setup and updates
Begin by verifying whether your system exposes a TPM in the operating system and in the BIOS/UEFI setup. On Windows, you can use the TPM management console (tpm.msc) to check status and version. In the BIOS/UEFI, look for entries labeled TPM, PTT, fTPM, or Security Device; confirm it’s enabled and set to a compatible mode (e.g., TPM 2.0). For firmware updates, visit your motherboard or vendor page and review the latest firmware revisions, release notes, and any known compatibility caveats with Valorant. After applying updates, run a quick boot test and launch Vanguard in a controlled environment to observe any stability changes. Debricking emphasizes maintaining a saved backup plan in case a firmware update requires a rollback.
Security caveats and vendor notes
No technology path is entirely risk-free. Firmware updates can occasionally introduce driver conflicts or bricking risks if performed incorrectly, though such events are rare with official tools. TPM-based approaches require careful BIOS/UEFI configuration and vendor-provided tools to avoid misconfigurations that could prevent system boot or disable security features. Always back up essential data before making changes, enable Secure Boot, and keep a rescue plan ready. The Debricking team recommends staying within official guidance from your hardware vendor, ensuring you have recovery media, and testing changes in a controlled manner before committing to a full gaming session.
Implementation steps at a high level
- Start with inventory: list your motherboard model, CPU, existing TPM or TPM-compatible hardware, and current firmware revisions.
- Decide on a path: firmware-based improvements or discrete TPM hardware-backed security.
- Prepare your environment: back up data, create a recovery drive, and verify Windows version compatibility if you are using Windows with Vanguard.
- Execute updates: apply firmware and driver updates from official sources, then enable required security features in BIOS/UEFI (Secure Boot, TPM state, etc.).
- Verify operation: boot normally, run stability tests, and launch Valorant to confirm Vanguard behaves as expected.
- Monitor and adjust: keep an eye on compatibility issues after updates and be prepared to revert if necessary.
Common misconceptions
- TPM automatically guarantees cheat-proof gaming: hardware-backed trust reduces tampering risk but does not eliminate all cheat vectors.
- Firmware updates are always risky: reputable vendors provide safe, staged updates with rollback options.
- You must have a discrete TPM to play Valorant: many systems can operate with firmware-based trust or software attestation paths just fine, depending on the hardware and Vanguard configuration.
- More security equals worse performance: well-designed hardware-backed security typically adds negligible overhead in gaming workloads.
- All TPMs are the same: TPM features and implementations vary by vendor and platform; TPM 2.0 support and attestation capabilities should be verified for compatibility with your rig.
Additional resources and references
- Debricking Analysis, 2026: Practical guidance on firmware and TPM choices for gaming rigs.
- Valorant Vanguard official support: Security and system requirements documentation.
- Hardware vendor manuals: TPM enablement and firmware update procedures for popular motherboard brands.
Comparison
| Feature | Firmware-based approach | Discrete TPM approach |
|---|---|---|
| Security model | Software-anchored, relies on firmware integrity checks | Hardware-backed keys and attestation via TPM |
| Valorant Vanguard compatibility | Depends on firmware/driver support; may benefit from Secure Boot alignment | Often aligns with kernel security checks; requires TPM-enabled path |
| System requirements | Standard PC with up-to-date firmware; no extra hardware required | Requires TPM 2.0 or compatible module; BIOS/UEFI configuration needed |
| Maintenance/updates | Ongoing firmware and driver updates from vendor | TPM firmware updates and platform drivers; vendor-driven cadence |
| Cost/availability | Low to moderate; often included with motherboard firmware updates | Moderate to potentially higher if TPM module is not bundled |
| Impact on performance | Low overhead; influenced by drivers and firmware quality | Minimal CPU overhead; negligible gaming impact |
| Ease of deployment | Moderate; requires firmware download and installation with recovery options | Higher; involves BIOS changes and proper TPM configuration |
| Best for | Users seeking broad hardware compatibility and flexibility | Users prioritizing hardware-backed security and robust attestation |
Positives
- Flexible and broad hardware compatibility
- Lower upfront cost and quicker setup for many systems
- Easier to revert if issues arise during updates
- Continual improvements through firmware/driver updates
Disadvantages
- Software-based trust is more vulnerable to driver bugs
- May offer weaker protection against sophisticated tampering
- Hardware-independent approaches can require more frequent effort to maintain
- TPM-based paths can be complex to configure for novices
Discrete TPM generally provides stronger hardware-backed security for Valorant, but firmware-based paths remain practical for broad compatibility.
If your rig supports a TPM without major BIOS hurdles, TPM is the safer long-term option. If you value simplicity and broader hardware support, firmware-based trust remains a solid, lower-friction choice with careful maintenance.
Questions & Answers
Do I need a TPM to play Valorant?
No, you can play Valorant without a discrete TPM. Vanguard can operate with software-based attestation or firmware checks on many systems. However, having TPM can enhance hardware-backed trust and future-proof security expectations.
No, Valorant can run without a TPM, but TPMs provide stronger hardware-backed trust where available.
Can firmware updates affect Valorant performance?
Firmware updates can improve stability and compatibility, which may indirectly affect performance by reducing crashes and driver conflicts. In most cases, the effects are neutral or positive when installers follow official guidance.
Firmware updates can improve stability and compatibility; performance impact is usually neutral to positive.
Is enabling Secure Boot required for Vanguard?
Secure Boot is commonly recommended for enhanced security and is often a prerequisite for kernel-level checks. Check your motherboard documentation and Valorant/Vanguard guidance to confirm exact requirements for your setup.
Secure Boot is often recommended for Vanguard, but verify with official guidance for your hardware.
What if my PC doesn’t have a discrete TPM?
If you don’t have a TPM, you can still pursue firmware-based security paths and ensure all drivers and firmware are up to date. Some systems may enable TPM via BIOS, others may rely on software attestation. Plan for a gradual upgrade path if hardware-free options prove insufficient.
No TPM? You can still optimize with firmware-based security and ensure software updates are current.
How do I verify if TPM is present on my system?
On Windows, run tpm.msc to check TPM presence and version. In the BIOS/UEFI, look for TPM, PTT, or fTPM options and confirm it’s enabled. If unavailable, consult your motherboard manual or vendor support for upgrade options.
Use tpm.msc in Windows and check BIOS/UEFI for TPM settings to verify presence.
Are there risks using TPM with gaming rigs?
Any hardware configuration carries risks if misconfigured (e.g., boot failures). TPMs add a layer of security but require careful setup, backups, and adherence to vendor instructions to avoid boot or compatibility problems.
TPMs add security but require careful setup and backups to avoid boot issues.
Top Takeaways
- Assess TPM availability on your motherboard before deciding
- Weigh hardware-backed security against setup complexity
- Keep firmware and drivers up to date for best Vanguard compatibility
- Back up data and have a recovery plan before major changes
- Consult official vendor guidance to avoid misconfigurations