Difference Between Firmware and Application: A Practical Comparison
Learn the difference between firmware and application with definitions, examples, and practical guidance on how each runs, updates, and secures devices in 2026.
Firmware and applications serve different purposes in a device. In short: firmware is the low-level software that controls hardware, while applications are user-facing programs running on an OS. The key difference lies in where they execute, how they’re updated, and how they interact with security and hardware resources.
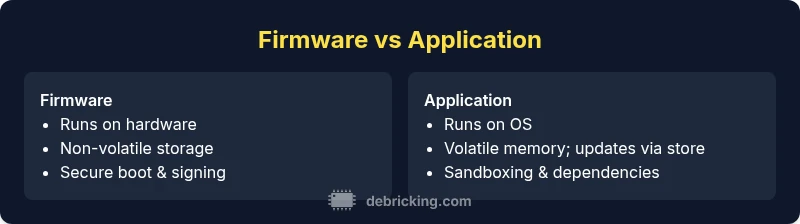
Difference between firmware and application
According to Debricking, the difference between firmware and application is not just vocabulary; it defines how the device is designed, updated, and secured. Firmware is the low-level code that directly controls a device's hardware, running in non-volatile storage and often initializing hardware components during boot. Applications, by contrast, are higher-level programs that run on top of an operating system or a microkernel and provide user-facing features. Distinguishing these roles helps engineers choose correct update strategies, allocate resources, and plan testing. For readers who own or maintain devices, recognizing this distinction improves troubleshooting and reduces the risk of bricking a device during updates. The phrase "difference between firmware and application" maps to a practical set of rules: firmware updates are typically delivered as image-level packages, while applications update through installable packages, apps stores, or OTA channels. The implications extend to security, reliability, and user experience.
Where firmware runs in devices
Firmware executes in the closest layer to the hardware and often resides in flash memory on a microcontroller or system-on-chip. It contains bootloaders, basic device drivers, and initialization routines that must run before any higher-level software can operate. Because it is heavily hardware-specific, firmware is typically tightly coupled with the device’s hardware design, making backward compatibility and recovery challenging. Manufacturers usually sign firmware images to ensure authenticity, and a failed flash can lead to a bricked device. In network devices, firmware may include secure boot, hardware RNG, and fuse settings that persist across resets. In many consumer devices, firmware updates are less frequent but more disruptive when they fail, requiring careful rollback plans. Understanding where firmware lives and how it persists helps owners assess risk, prepare backups, and evaluate update instructions before attempting a flash.
How applications interact with firmware
Applications run above the firmware layer, leveraging OS services, drivers, and APIs to perform tasks. They communicate with firmware through defined interfaces, such as device drivers, system calls, or specialized communication protocols. In embedded systems, the line between firmware and application can blur: a so-called firmware application might run on a real-time operating system and share memory with firmware components. Updates to applications can be hot-swapped, downloaded via the app store, or installed through a package manager, often with rollback or version pinning. Because applications depend on the hardware abstraction layer provided by firmware and the OS, compatibility testing should cover both sides: a new app version may require a firmware revision to function correctly, while a firmware change may necessitate updated drivers or libraries in the application. The collaboration between firmware and application is a core design consideration for reliable devices.
Storage, memory, and lifecycles
Firmware typically resides in non-volatile memory, such as flash, and is designed for a long lifecycle with slow update cycles. It must survive across power cycles and provide a stable baseline for every device boot. Applications often live in a separate storage domain (e.g., internal flash for apps on some systems or SD cards on embedded devices) and can be updated more frequently. This separation helps minimize downtime; firmware updates usually require reboot and can be risky if interrupted, whereas app updates are often incremental and can be rolled back. The lifecycle management for firmware emphasizes long-term security, continuous integrity checks, and secure boot, while applications emphasize feature releases, user experience, and dependency management. Understanding the memory map and update channels informs planning, such as scheduling windows for updates, ensuring power stability, and verifying recovery options in case of a failed flash.
Update mechanisms: firmware updates vs app updates
Firmware updates are delivered as image files that replace the entire firmware region or critical boot components. They are often signed, tested for hardware compatibility, and require a secure boot chain to prevent tampering. The update process can be risky: a power loss or a failed flash can brick the device, so manufacturers implement rollback, dual-bank updates, and failure flags. App updates, by contrast, are typically delivered as incremental patches via app stores or package managers. They can be downloaded while the device is running and rolled back with less risk, assuming compatibility checks are place. OTA (over-the-air) update channels may be used for both, but the constraints differ: firmware OTA requires robust power management and fallback strategies, while app OTA emphasizes network efficiency and user consent. For practitioners, the key difference in update mechanisms is the risk model: firmware updates demand stricter validation and safer rollback, whereas app updates prioritize feature delivery and user-facing reliability.
Security considerations for firmware vs applications
Security considerations differ in emphasis. Firmware is the security boundary; a compromised firmware can undermine the entire device and persist across resets. Therefore, firmware signing, secure boot, measured boot, and hardware-backed key storage are crucial. Supply chain security for firmware involves verifying the origin of the image, keeping component libraries up to date, and monitoring vulnerability databases. Applications require secure coding, dependency management, and sandboxing to minimize impact from compromised modules. Both layers benefit from least privilege principles, integrity checks, and incident response planning. Both layers benefit from least privilege and regular vulnerability scanning. The attacker surface for firmware often includes the bootloader and update mechanism; for apps, it includes the runtime environment and external libraries. Regular vulnerability scanning, patch management, and consistent versioning help reduce risk across both domains.
Examples by device category: routers, cameras, PCs, embedded devices
Routers and network appliances rely on firmware for routing features, security protocols, and hardware acceleration. A router’s firmware update might address a new WPA3 implementation or a patched vulnerability; it often requires a coordinated reboot and may include a diagnostic interface. IP cameras store critical footage encryption instructions in firmware and update firmware to address CVEs; application software on cameras typically includes the user interface and processing pipelines but remains tightly coupled to the firmware. Personal computers run a large operating system with many applications; firmware updates apply to BIOS/UEFI, SSD controllers, and embedded controllers, while applications provide day-to-day productivity tools. Embedded devices, such as HVAC controllers or industrial sensors, use compact firmware with boot-time diagnostics; the applications on these devices often implement data collection, analytics, or control algorithms. Each category illustrates how firmware and application layers interact to deliver stable, secure functionality.
Common misconceptions and myths
One common myth is that firmware and software are interchangeable terms. In reality, they occupy different layers and serve different purposes. Another misconception is that firmware updates are optional; for many devices, a firmware update closes critical security gaps and fixes hardware bugs. A third myth is that all apps can be updated without affecting the firmware; in some cases, a new app version requires a firmware revision for compatibility. Finally, some users assume firmware updates are inherently riskier than application updates; while firmware updates carry higher brk risk, proper safeguards (backup, rollback, power stability) can mitigate that risk.
Evaluation criteria: how to decide which to update first
Start with risk assessment: does a vulnerability affect the device's core functionality or network exposure? If yes, firmware updates deserve priority. Consider the potential downtime and recovery options. Firmware updates often require device reboots and can leave services unavailable; plan maintenance windows accordingly. For feature needs, app updates may provide immediate value without touching the firmware, but compatibility constraints exist. Check release notes for both layers and test updates in a staging environment whenever possible. Finally, verify that the device’s supply chain and vendor support are active; end-of-life firmware can pose long-term risks even if the latest app updates are available.
Practical upgrade workflow (step-by-step)
Prepare a backup and confirm power stability. Review the vendor’s official update instructions and confirm device model, serial, and current firmware version. Initiate firmware update only if the device is on battery backup or plugged into reliable power. After a firmware update, verify boot stability and run a baseline diagnostic. Next, check for app updates and apply the latest versions, testing critical features. Maintain a rollback plan in case something goes wrong. Document the update sequence, take screenshots, and store firmware images securely. If the device supports dual-bank updates, monitor the status LEDs for rollback indicators. Finally, perform a post-update health check, including security settings and network access controls.
Troubleshooting update failures
Common update failures include power interruption, interrupted downloads, or signature mismatches. Start with the vendor’s recovery mode or bootloader to re-flash a known-good image. If possible, use a rescue USB or recovery partition. For app updates, verify network connectivity and check that dependencies meet minimum versions. Logs and diagnostic outputs are invaluable; capture error codes and CVE references. In a mixed firmware/app scenario, revert to a known-good firmware first, then re-apply the app update. If the device enters a boot loop, attempt safe mode or factory reset as a last resort, ensuring you have recent backups. Finally, consult vendor support channels or community forums for model-specific guidance.
Future trends: firmware evolution and software-app convergence
Firmware is evolving toward modular, service-oriented architectures, enabling in-field component updates without full reflashes. Increasing use of secure enclaves, hardware-assisted cryptography, and transparent supply-chain transparency will improve confidence in firmware integrity. Applications will continue to gain deeper integration with hardware, requiring robust compatibility testing and automated CI/CD pipelines across both layers. The convergence trend means more devices may ship with programmable firmware images that can be extended via apps or skin layers, enabling dynamic feature sets while maintaining a stable core. In practice, this means developers and engineers must design with forward compatibility, robust rollback plans, and clear upgrade documentation.
Legal and compliance aspects of firmware updates
Many industries require strict controls over firmware updates, including traceability, reproducible build records, and secure boot enforcement. Compliance frameworks commonly mandate vulnerability management, incident reporting, and end-to-end logging of update events. Organizations should maintain a software bill of materials (SBOM) for firmware and related components to support risk assessments and audits. For consumer devices, manufacturers face disclosure obligations about security vulnerabilities and remediation timelines. Properly handling updates reduces legal exposure and increases customer trust.
Tools and resources for DIY firmware updates
DIY enthusiasts can use a range of tools to backup, flash, and verify firmware updates. Official vendor utilities provide validated flashing procedures and recovery modes, while third-party tools may help with diagnostics and image verification. Always obtain firmware images directly from the vendor to avoid tampering. Use checksum verification, secure transfer protocols, and network isolation when updating devices on a lab bench. Document each step and maintain a safe rollback plan. For learning, consult vendor documentation, online guides, and reputable forums; avoid unverified sources that may push unsafe firmware.
Case studies: notable firmware update drama
Consider a router firmware update that introduced a regression in packet handling, affecting VPN compatibility. A well-documented rollback and vendor patch resolved the issue quickly, demonstrating the importance of a tested recovery path. Another case involved a smart camera where an OTA update introduced clock drift, requiring a vendor hotfix and a staged rollout. These cases illustrate why robust testing, staged rollouts, and clear rollback options matter across firmware and application layers.
Quick-reference glossary of terms
Firmware: Low-level software embedded in hardware that initializes and controls device functions. Image: A binary blob representing the firmware to be flashed. OTA: Over-the-air update mechanism to deliver firmware or app updates. Secure Boot: A process ensuring only trusted software runs at startup. SBOM: Software Bill of Materials used for vulnerability management and compliance.
Comparison
| Feature | Firmware | Application |
|---|---|---|
| Execution environment | Runs directly on hardware, often in ROM/flash | Runs on top of an OS or hypervisor |
| Update mechanism | Image-level flash updates; may require reboot | Incremental patches or installer packages; often hot-swappable |
| Storage location | Non-volatile memory (flash); long lifecycles | User-space or app partitions; shorter lifecycles |
| Security focus | Secure boot, image signing, hardware root of trust | Sandboxing, dependencies, access controls |
| Recovery options | Rollback capability and dual-bank updates | Rollback via versioning and app store history |
| Typical devices | Embedded controllers, routers, cameras | PCs, smartphones, tablets, software appliances |
| Typical failure modes | Bricking due to interrupted flash or power loss | Incompatibilities or data corruption in libraries |
Positives
- Clarifies responsibilities for updates and maintenance
- Supports targeted security hardening at hardware level
- Enables reliable boot and hardware initialization
- Facilitates long device lifecycles
Disadvantages
- Can create separate upgrade workflows and tooling needs
- Firmware risks can be higher during flash failures
- App updates may require firmware compatibility checks
Firmware updates are foundational for hardware stability; apps drive features.
Prioritize firmware updates for security and reliability, then manage applications for usability and new functions. A balanced, phased approach reduces risk and preserves device integrity.
Questions & Answers
What is firmware?
Firmware is low-level software embedded in hardware that controls core device functions. It runs at boot and initializes hardware components. It is typically non-volatile and tightly coupled to the hardware.
Firmware is the low-level software built into hardware that runs at startup and controls essential device functions.
Can firmware be updated remotely?
Yes, many devices support over-the-air firmware updates. These usually require a secure channel, power stability, and rollback mechanisms in case of failure.
Yes, firmware can often be updated over the air, with safeguards in place.
What are the risks of firmware updates?
The main risks are bricking the device if the update is interrupted or corrupted. Proper safeguards, backups, and rollback plans reduce these risks.
Risks include bricking if updates fail; use backups and safeguards to minimize danger.
Do all devices require firmware updates?
Not every device requires frequent firmware updates, but many do for security, stability, and hardware improvements. Apps may require updates more often for features.
Not all devices need frequent firmware updates, but many do for security and stability.
How often should I update firmware vs apps?
Prioritize firmware when security vulnerabilities are present or hardware bugs exist. Update apps for new features, usability, and performance, ensuring compatibility with the firmware.
Update firmware for security and stability; update apps for features and usability, checking compatibility.
Top Takeaways
- Differentiate firmware from applications clearly
- Plan updates with risk-aware, staged workflows
- Prioritize security-critical firmware updates
- Test compatibility between firmware and apps
- Maintain rollback and recovery options